Crazy Ransomware
The Crazy Ransomware is a file-locking Trojan that can stop media such as documents from opening with its attacks. As part of the VoidCrypt Ransomware or Void Ransomware's family, it lacks a free decryption solution. For Windows users, backing up media to other devices and installing security solutions for removing the Crazy Ransomware automatically is a sufficient response.
Increasingly-Familiar Faces in Extortion for the New Year
As the new year rolls onward, many threat actors stay with already-proven tools to attack victims and make cryptocurrency out of it. The particularly-thriving VoidCrypt Ransomware family, while it's a latecomer to the threat landscape, is active noticeably. Like the newest the Crazy Ransomware, most variants issue few changes besides the all-but-mandatory updates to the attacker's e-mails for communication. Otherwise, it's a very typical group member, not dissimilar to samples of (in no particular order) the Exploit Ransomware, the Legend Ransomware, the Spade Ransomware or the Lalaland Ransomware.
The Crazy Ransomware blocks the user's files by encrypting them with a secure algorithmic routine, which impacts most media, such as text documents, spreadsheets, music, movies or pictures. Not to confuse with the internal encryption process, the Trojan also adds an extension that consists of several elements: the campaign's e-mail, an ID and the 'crazy' string. The identification text is a set of semi-random alphanumeric characters per victim.
Malware researchers verify the Crazy Ransomware's using the same, not-particularly-professional ransom note as most other versions of the VoidCrypt Ransomware. This pop-up has a two-day deadline and provides two e-mails for speaking with the threat actor. Although it specifies a Bitcoin transaction, the number isn't available – which might be a negotiating tactic. The use of English leaves the Crazy Ransomware demographics vague since criminals deploying English-based Trojans may target most parts of the world.
Crunching Back a Trojan's Unrealistic Expectations of Profit
Victims have simple ways of counteracting any encryption, even in cases of non-decryptable families. Backups on other devices can provide a straightforward recovery for any data and are crucial, especially for often-attacked formats like documents. Users should avoid depending on backup methods that malware researchers often rate as vulnerable, including local backups, the Restore Points, and network-shared drives without any additional access protection.
The Crazy Ransomware also includes some features that users may overlook during the infection. It disables SQL server-related software like Microsoft's MSDTC, deletes admin, backup, and error-logging data, and disables some Windows recovery features. Windows users may need to repair their Boot Configuration Data file afterward.
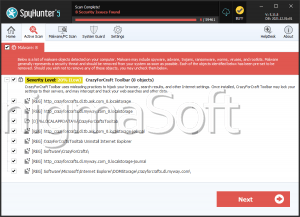
Besides the never-ceasing relevance of backups, users also should protect their computers with appropriate security products. Most AV vendors have services up to the task of deleting the Crazy Ransomware, as part of a well-known family with few anti-detection features.
The Crazy Ransomware isn't that 'crazy,' as a Trojan that, by and large, doesn't stray from proven ways of doing business illicitly. It's in the hands of users to make its ransom attempts seem not worth the effort since the alternative of paying an unknown ransom is crazy.