Exploit Ransomware
The Exploit Ransomware is a crypto locker variant belonging to the VoidCrypt Ransomware family. As such, it operates much in the same way as VoidCrypt, apart from using different contact emails and having a unique extension for the files it encrypts. Affected users will not be able to decrypt the locked data by simple brute-forcing.
The first signs they may notice when the Exploit Ransomware has invaded their computers will be when their files change from having their normal names to ones that have been modified significantly. The Exploit Ransomware follows a complex pattern for the files it encrypts - the threat appends an email address, a specific ID assigned to the victim, and its particular file extension at the end of every original filename. The email address is 'alix1011@mailfence.com,' while the extension is '.exploit. As for its ransom note, the Exploit Ransomware drops a .hta file named '!INFO.HTA' in every folder containing encrypted data. The files generate a pop-up window displaying the instructions from the hackers.
According to the note, users are expected to make a payment in Bitcoin. To further push their victims into initiating contact, the criminals threaten that after 48 hours have passed, the ransom amount will be doubled. They allow for a couple of small non-important files attached to the email message to be decrypted for free. A secondary email address at 'alixxm1011@protonmail.com' that should be used if the victims do not receive a response after contacting the primary email.
The full set of instructions left by the people behind the Exploit Ransowmare is:
'!!! Your Files Has Been Encrypted !!!♦ your files has been locked with highest secure cryptography algorithm ♦
♦ there is no way to decrypt your files without paying and buying Decryption tool♦
♦ but after 48 hour decryption price will be double♦
♦ you can send some little files for decryption test♦
♦ test file should not contain valuable data♦
♦ after payment you will get decryption tool ( payment Should be with Bitcoin)♦
♦ so if you want your files dont be shy feel free to contact us and do an agreement on price♦
♦ !!! or Delete you files if you dont need them !!!
♦Your ID
our Email :alix1011@mailfence.com
In Case Of No Answer :alixxm1011@protonmail.com.'
As you can see, users have to contact the extortionists behind the ransomware to get their data back. They are told they must contact the cyber criminals as quickly as possible or the price of decryption doubles. The message offers one last bit of intimidation by warning users that attempting to decrypt the ransomware could cause permanent data loss.
Exploit ransomware was discovered by Xiaopao.
What Should Victims Do?
We highly recommend that victims don’t contact the attackers behind Exploit. Doing so only opens you up to further risk. It is unlikely the criminals will live up to their end of the deal and give you the decryption key you need once they get your money. It is more likely they will disappear with your money and you’ll never hear from them again.
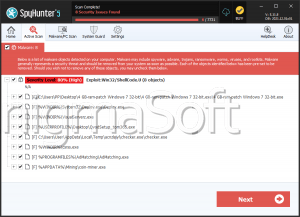
Instead, you should look to remove the virus from your computer. Use an antivirus program to remove Exploit from your computer. Doing this won’t undo the encryption, but it will allow you to restore your files from a backup without having your data encrypted all over again.
If you don’t have an external backup, such as an external hard drive or cloud storage, you might have success with file recovery software. Don’t depend on these software programs though, as they rely on data stored on the computer. This data, called Shadow Volume Copies, is commonly deleted by ransomware viruses. Attackers want to make it as difficult as possible for you to restore your files and have to pay them instead.
How Does Ransomware Infect Computers?
Exploit ransomware gets o computers in the same way that other viruses do. Email spam is the most common attack method, but it isn’t the only one. Attackers send thousands of unsolicited emails in the hopes that some people fall for them. The messages appear to be from legitimate sources and contain links or attachments. Readers are encouraged to interact with these attachments, but doing so presents a serious risk. Opening the link or attached file infects your computer with the Exploit VoidCrypt ransomware.
Attackers also hide viruses inside pirated software and illegal activation tools. More often than not, these illicit programs install viruses on your computer. It’s worth your time, money, and the health of your computer to purchase software through official channels. Not only do you support developers, but you protect your computer and prevent the spread of computer viruses.
Take care when downloading software as hackers upload viruses to freeware sites and malicious download sources. Only use official websites and trusted third-party websites when downloading installation files to keep your data safe.
Don’t forget to invest in some robust antivirus software. These programs monitor your computer and catch problems such as Exploit before they can become serious issues. Antivirus programs are the first line of defense against malicious programs.