Atomic Ransomware
Ransomware attacks continue to evolve, targeting both individuals and organizations with increasingly sophisticated tactics. One of the latest threats, Atomic ransomware, exemplifies how cybercriminals leverage encryption and data theft to maximize pressure on victims. Protecting your devices, data, and online identity is critical to avoid the devastating consequences of such attacks.
Table of Contents
How Atomic Ransomware Works
Atomic ransomware belongs to the notorious Makop malware family. Once executed, it begins encrypting files across the victim's system using robust RSA and AES encryption algorithms. During the encryption process, Atomic alters file names by appending the victim's unique ID, a contact email address, and the '.atomic' extension. For instance, 'report.pdf' may appear as 'report.pdf.[2AF20FA3].[data-leakreport@onionmail.com].atomic' after the attack.
After locking the files, the malware changes the desktop wallpaper and generates a ransom note named '+README-WARNING+.txt.' This note informs victims that not only have their files been encrypted, but sensitive information has also been stolen. The attackers threaten to leak this data unless the ransom is paid, adding another layer of coercion.
The Ransom Note and Its Demands
The ransom message urges victims to contact the criminals via 'data-leakreport@onionmail.com' or 'support-leakreport@onionmail.com' to negotiate payment. It warns against using third-party recovery tools or modifying encrypted files, claiming that such actions will lead to irreversible data corruption.
Unfortunately, decrypting files without the attacker's unique key is nearly impossible unless security researchers create a free decryptor. Even then, paying the ransom does not guarantee file recovery, as attackers often fail to provide the promised tools once they receive the payment. Moreover, paying fuels further criminal activity.
Distribution Methods and Infection Vectors
Atomic ransomware is typically distributed through deceptive online practices designed to exploit user trust or curiosity. Attackers commonly use malicious email attachments, phishing campaigns, pirated software, and software cracks or key generators to spread their payloads. Technical support scams and fake software updates are also frequent infection methods.
Cybercriminals also rely on malicious documents, executables, and script files hidden in archives like .zip or .rar. In some cases, drive-by downloads from compromised websites, malvertising campaigns, or vulnerabilities in outdated software can be exploited. External storage devices such as infected USB drives may also serve as vectors, especially within corporate environments.
Removing Atomic Ransomware and Data Recovery
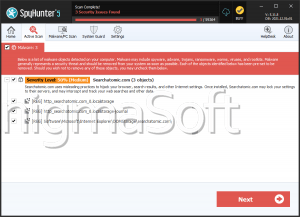
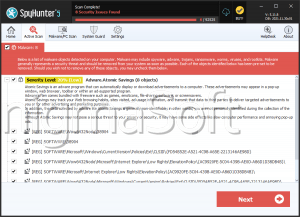
Once a device is infected, immediate removal of the ransomware is essential to stop further encryption or lateral spread across the network. However, removing the malware will not decrypt files already locked. Recovery is only possible through secure backups created before the infection or, in rare cases, using publicly available decryptors if one is developed for the specific strain.
Victims are strongly advised not to engage with the attackers or pay the ransom. Instead, they should focus on professional system cleanup and restoring files from offline or cloud-based backups.
Best Practices to Stay Safe from Ransomware
Effective protection against ransomware like Atomic involves a multi-layered security approach and cautious online behavior. Users should combine preventive measures, backup strategies, and robust security tools to minimize their exposure to threats.
- Proactive Cyber Hygiene
Maintaining updated software and operating systems is one of the best defenses against ransomware, as unpatched vulnerabilities are prime entry points. Avoid downloading files from untrusted websites, and be extremely cautious when opening email attachments or clicking on links, especially if they come from unknown or suspicious sources.
- Strong Security Infrastructure
Installing reliable anti-malware solutions with real-time protection is essential to detect and block ransomware payloads before they execute. Regular backups, stored on offline or secure cloud services, ensure that critical data remains safe even in the event of an attack. Enabling email filters, disabling macros in documents, and segmenting networks in corporate environments are additional steps that significantly reduce risk.
Conclusion
Atomic ransomware is a dangerous threat that combines data encryption with extortion through the threat of data leaks. By exploiting unsuspecting users with malicious attachments, pirated software, and fraudulent websites, cybercriminals behind Atomic aim to maximize their profits while causing substantial harm. Adopting strong cybersecurity practices, maintaining regular backups, and staying vigilant online remain the best defenses against ransomware attacks of this kind.