Albiriox MaaS Malware
A newly surfaced Android threat, known as Albiriox, represents the latest evolution in on‑device fraud operations. Advertised under a malware‑as‑a‑service model, it delivers an extensive toolkit for remote control, automated abuse, and stealthy manipulation of victims' devices.
Table of Contents
A Commercialized Threat Built for Fraud
Albiriox is marketed as a full-featured MaaS offering designed to support on‑device fraud (ODF), real‑time device interaction, and seamless screen manipulation. Early activity suggests the operators initially conducted a limited recruitment phase in late September 2025 before transitioning to a broader commercial rollout. Indicators tied to forum discussions, language use, and supporting infrastructure point toward Russian‑speaking cybercriminals spearheading the project.
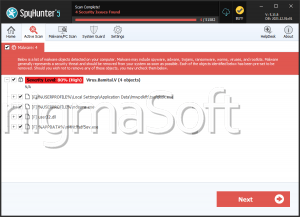
The developers also provide a custom builder that reportedly integrates with the Golden Crypt crypting service, enabling customers to evade antivirus tools and mobile security defenses.
Targeting a Broad Application Landscape
The malware embeds an extensive hard‑coded list of more than 400 targeted applications. These span a wide range of sensitive categories, including banking, fintech, cryptocurrency exchanges, payment processors, digital wallets, and online trading platforms. This broad targeting approach aligns with its goal of capturing credentials, initiating fraudulent transactions, and maintaining covert access to financial apps.
Covert Deployment Through Social Engineering
Distribution relies heavily on deceptive lures designed to trick users into installing disguised droppers. Attackers pair social engineering themes with packing and obfuscation techniques to sidestep static analysis tools. One campaign focused on Austrian users employed German‑language SMS messages and shortened URLs leading to counterfeit Google Play Store pages for apps such as 'PENNY Angebote & Coupons.'
Victims who selected the fake 'Install' button unknowingly downloaded a dropper APK. After launch, the app requested permission to install additional software, pretending to initiate a routine update. This action triggered the deployment of the main Albiriox payload.
A related campaign rerouted potential victims to a fraudulent PENNY‑themed website, where they were prompted to supply their phone number to receive a WhatsApp download link. Only Austrian numbers were accepted, and all submissions were sent to a Telegram bot controlled by the operators.
Remote Control and Covert Operation
Once active, Albiriox establishes communication with its Command‑and‑Control server through an unencrypted TCP socket. This enables threat actors to push commands used for full remote interaction. Key capabilities include:
- VNC‑based device control, supported by an additional remote‑access module
- On‑demand extraction of sensitive data
- Black or blank screen deployment to obscure malicious activity
- Remote volume adjustments to maintain operational stealth
One variant uses Android's accessibility services to present all interface elements to the operators. This technique is expressly designed to circumvent the restrictions of Android's FLAG_SECURE feature, which prevents screenshots and screen recordings within many financial applications.
Bypassing Interface Protections for Fraud
The accessibility‑driven streaming mechanism gives attackers a node‑level representation of the device interface. Because it avoids traditional display capture techniques, it does not trigger built‑in protections employed by banking and cryptocurrency apps. As a result, the attackers gain persistent, unrestricted visibility of sensitive screens.
Overlay Attacks and Credential Harvesting
In line with other Android banking trojans, Albiriox employs overlay attacks tied to its hard‑coded list of targeted applications. These overlays appear as legitimate login panels or system dialogs, enabling effective credential theft. Additionally, the malware serves misleading screens, such as fake update prompts or completely black displays, to hide its activities while fraudulent operations proceed in the background.
A Fully Equipped ODF Platform
Albiriox demonstrates all hallmark characteristics of advanced on‑device fraud malware. Its blend of VNC‑based remote manipulation, accessibility‑driven automation workflows, targeted overlays, and dynamic harvesting techniques allows attackers to circumvent authentication controls and slip past conventional fraud‑detection mechanisms. By operating directly inside a victim's legitimate session, the malware grants its operators an exceptionally high level of control and an equally significant opportunity for abuse.