XWorm 6.0 Malware
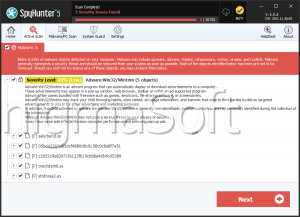
Security researchers have traced XWorm from a compact remote-access framework into a highly modular platform that operators use to run a wide range of malicious operations on compromised Windows hosts. First flagged in 2022 and linked to a group using the handle EvilCoder, XWorm has been actively developed and reworked by individuals using the personas XCoder (lead developer until mid‑2024) and, more recently, sellers such as XCoderTools. Its continued evolution and reappearance demonstrate how quickly a tool can fragment, be repackaged, and re‑enter the wild.
Table of Contents
How XWorm Is Built — Core + Plugins
XWorm's architecture centers on a small client that reaches out to a Command‑and‑Control (C2) server and a large set of plug‑in payloads that are loaded into memory on demand. The design allows operators to keep the lightweight client on a host while dynamically pushing functionality (DLLs) to perform specific tasks. The project's ecosystem has also included ancillary tools promoted by the developers: a .NET malware builder, a separate RAT called XBinder, and a utility that attempts to bypass Windows User Account Control (UAC). The developer community around XWorm has advertised other components and fake installers (notably malicious ScreenConnect installers) as distribution lures.
Infection Chains And Delivery Techniques
Researchers have observed multiple, shifting infection workflows for XWorm. Early chains relied on phishing messages that delivered Windows shortcut (LNK) files; the LNKs executed PowerShell, which dropped decoy files (for example, a harmless TXT) and a deceptive executable (commonly masquerading as Discord) that ultimately launched the real payload. More recent campaigns distributing the 6.x family have used malicious JavaScript attachments in phishing emails that display a decoy PDF while executing background PowerShell that injects XWorm into legitimate processes such as RegSvcs.exe to avoid detection. Threat actors have also pushed cracked or trojanized versions of XWorm components through GitHub repos, file‑sharing sites, Telegram channels, and YouTube, attempting to trick less skilled operators into installing backdoored builders.
Evasion, Remote Control, And Operator Features
XWorm integrates multiple anti‑analysis checks that abort execution when it detects virtualization or sandbox indicators. Once active, the client accepts commands from the C2 that cover common RAT operations (file transfer, process and service manipulation, executing shell commands, opening URLs), system control (shutdown/restart), and more aggressive actions such as launching DDoS activity. The modular plugin model lets a remote operator run more than 35 different DLL payloads in memory without writing them to disk, giving XWorm a flexible attack surface while reducing forensic traces.
Plugin Delivery Protocol
XWorm 6.x implements a hash‑first plugin protocol: the C2 issues a 'plugin' command that contains the SHA‑256 hash of the requested DLL plus runtime arguments. The client checks whether it already has that plugin cached; if not, it requests the file with 'sendplugin'. The server replies with a 'savePlugin' command carrying the plugin as a base64 blob and its SHA‑256 hash. The client decodes the blob, verifies the hash, and loads the DLL directly into memory for execution.
Notable Plugins And What They Do
- RemoteDesktop.dll — establishes an interactive remote session.
- WindowsUpdate.dll, Stealer.dll, Recovery.dll, merged.dll, Chromium.dll, SystemCheck.Merged.dll — credential and data theft from OS and applications (Windows keys, Wi‑Fi passwords, browser‑stored credentials, including bypasses for app‑bound encryption, and harvesters for FileZilla, Discord, Telegram, MetaMask).
- FileManager.dll — filesystem access and manipulation.
- Shell.dll — hidden execution of operator commands through cmd.exe.
- Informations.dll — host/system fingerprinting.
- Webcam.dll — captures webcam images/video to confirm a real victim.
- TCPConnections.dll, ActiveWindows.dll, StartupManager.dll — enumerates network connections, active windows, and autostart entries.
- Ransomware.dll — file encryption/decryption routines (shares code with NoCry‑style ransomware).
- Rootkit.dll — installs a modified r77 rootkit.
- ResetSurvival.dll — modifies the Windows Registry to survive certain device resets.
Other malware distributed via XWorm infections include:
- DarkCloud Stealer
- Hworm (VBS RAT)
- Snake KeyLogger
- Coin miners
- Pure Malware
- ShadowSniff (Rust stealer, open‑source)
- Phantom Stealer
- Phemedrone Stealer
- Remcos RAT
Operational Setbacks, Fragmentation, and Weaponized Forks
XWorm's development has not been linear. In the second half of 2024, the persona XCoder abruptly deleted their Telegram presence, casting doubt on the project's future. That gap, however, spawned opportunistic activity: cracked XWorm v5.6 packages that were themselves trojanized to infect other threat actors, and social engineering campaigns targeting 'script kiddies' via GitHub and other public channels — campaigns that researchers estimate attempted to compromise tens of thousands of devices (reportedly over 18,000).
Analysts also found modified forks, including a variant labeled XSPY (reported origin: Chinese‑language variant) and a critical remote code execution (RCE) weakness in some builds that allowed someone possessing the C2 encryption key to execute arbitrary code on infected hosts. The toolkit's fragmentation makes attribution and takedown more difficult; different sellers and forks can appear and disappear independently.
The 2025 Resurfacing: XWorm 6.0 And Marketplace Activity
On June 4, 2025, a vendor calling itself XCoderTools posted XWorm 6.0 on cybercrime forums priced at $500 for lifetime access, claiming the release was completely re‑coded and that the previously reported RCE flaw had been fixed. It is unclear whether this release came from the original author or from a third party leveraging the XWorm brand. Observed XWorm 6.0 samples are configured to contact a C2 at 94.159.113[.]64 on port 4411 and implement the plugin protocol described above, enabling rapid, in‑memory delivery of dozens of DLL modules.
Bottom Line
XWorm's life cycle — from active development through abandonment to reappearance under new sellers and trojanized cracked builds — is a reminder that malware is an ecosystem. Even if an original author disappears, their code can be forked, weaponized, and redeployed by others. Defenders must therefore focus on resilient controls and detection strategies that assume adversaries will reuse and repackage existing toolsets.