XCry Ransomware
The XCry Ransomware is an encryption ransomware Trojan that was detected in January of 2019. The XCry Ransomware caught the attention of PC security researchers because it seems to be the first encryption ransomware Trojan written using Nim, a coding language designed to build command-line applications, Web servers and kernels. Nim-based programs can typically run across platforms without being modified heavily, making the XCry Ransomware more threatening particularly because it may be adapted for distribution on Mac OS or Linux easily. The XCry Ransomware is a strong threat that carries out an effective ransomware attack.
How the XCry Ransomware's Infection Works
The XCry Ransomware operates nearly identically to most encryption ransomware Trojans, taking the victim's files hostage and the asking for payment in exchange for the captured data. To take the victim's files hostage, the XCry Ransomware uses a strong encryption algorithm to make the victim's files inaccessible, targets the user-generated file, which may include databases, media files, and numerous other file types, such as the files with the following file extensions:
.jpg, .jpeg, .raw, .tif, .gif, .png, .bmp, .3dm, .max, .accdb, .db, .dbf, .mdb, .pdb, .sql, .dwg, .dxf, .cpp, .cs, .h, .php, .asp, .rb, .java, .jar, .class, .py, .js, .aaf, .aep, .aepx, .plb, .prel, .prproj, .aet, .ppj, .psd, .indd, .indl, .indt, .indb, .inx, .idml, .pmd, .xqx, .xqx, .ai, .eps, .ps, .svg, .swf, .fla, .as3, .as, .txt, .doc, .dot, .docx, .docm, .dotx, .dotm, .docb, .rtf, .wpd, .wps, .msg, .pdf, .xls, .xlt, .xlm, .xlsx, .xlsm, .xltx, .xltm, .xlsb, .xla, .xlam, .xll, .xlw, .ppt, .pot, .pps, .pptx, .pptm, .potx, .potm, .ppam, .ppsx, .ppsm, .sldx, .sldm, .wav, .mp3, .aif, .iff, .m3u, .m4u, .mid, .mpa, .wma, .ra, .avi, .mov, .mp4, .3gp, .mpeg, .3g2, .asf, .asx, .flv, .mpg, .wmv, .vob, .m3u8, .dat, .csv, .efx, .sdf, .vcf, .xml, .ses, .qbw, .qbb, .qbm, .qbi, .qbr , .cnt, .des, .v30, .qbo, .ini, .lgb, .qwc, .qbp, .aif, .qba, .tlg, .qbx, .qby , .1pa, .qpd, .txt, .set, .iif, .nd, .rtp, .tlg, .wav, .qsm, .qss, .qst, .fx0, .fx1, .mx0, .fpx, .fxr, .fim, .ptb, .ai, .pfb, .cgn, .vsd, .cdr, .cmx, .cpt, .csl, .cur, .des, .dsf, .ds4, , .drw, .eps, .ps, .prn, .gif, .pcd, .pct, .pcx, .plt, .rif, .svg, .swf, .tga, .tiff, .psp, .ttf, .wpd, .wpg, .wi, .raw, .wmf, .txt, .cal, .cpx, .shw, .clk, .cdx, .cdt, .fpx, .fmv, .img, .gem, .xcf, .pic, .mac, .met, .pp4, .pp5, .ppf, .nap, .pat, .ps, .prn, .sct, .vsd, .wk3, .wk4, .xpm, .zip, .rar.
It seems that the XCry Ransomware's intended targets are Web servers and corporate networks rather than individual computer users. The XCry Ransomware marks the files encrypted by its attack by adding the file extension '.xcry7684' to each affected file. The XCry Ransomware delivers its ransom note in the form of an HTML file named 'HOW_TO_DECRYPT_FILES.html' that is dropped on the infected computer. The full text of the XCry Ransomware's ransom note reads:
'Your files have been encrypted.
To decrypt your files, follow instructions
Open your explore, in the pathbar, enter %appdata%
Find the file encryption_key and send it to email: funnybtc@airmail.cc
Await payment instructions'
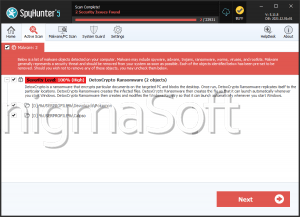
Protecting Your Data from Threats Like the XCry Ransomware
It seems that the main way in which the XCry Ransomware is being distributed is through fake updates to Adobe Flash and other third-party programs and spam email attachments. Because of this, learning to handle software downloads and spam emails is essential to prevent attacks like the XCry Ransomware. Since threats like the XCry Ransomware make the encrypted files impossible to restore, the best protection against these threats is file backup, which should be kept on external devices. Apart from file backups, a good security program that is fully up-to-date should be used to protect your computer from intrusions. File backups, strong security software, and preventive measures when browsing the Web are generally very effective measures to ensure that your computer is protected from all malware, including threats like the XCry Ransomware.