DetoxCrypto Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 6,208 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 1,986 |
| First Seen: | August 22, 2016 |
| Last Seen: | September 18, 2023 |
| OS(es) Affected: | Windows |
The DetoxCrypto Ransomware is an encryption ransomware Trojan that, as part of its attack, takes advantage of the hugely popular mobile game Pokemon GO. New variants of the DetoxCrypto Ransomware, first observed in August of 2016, include one themed after the popular game and one that has been named the 'Calipso version' of this threat. The DetoxCrypto Ransomware recycles large parts of the code and is very similar to other ransomware Trojans. However, the DetoxCrypto Ransomware is a new type of ransomware infection that computer users will need to be on the lookout for. It is very likely that new versions of the DetoxCrypto Ransomware will appear in the future.
Table of Contents
The DetoxCrypto Ransomware Intoxicates Your Files
The earliest version of the DetoxCrypto Ransomware uses images from the Pokemon GO game in the ransom note that it displays on the infected computer's Desktop. This version of the DetoxCrypto Ransomware replaces the victim's desktop wallpaper image with its ransom note. A second version of the DetoxCrypto Ransomware, discovered only a day later, uses a ransom note that does not include the Pokemon GO imagery and includes an interesting feature. This later version of the DetoxCrypto Ransomware, named DetoxCrypto Ransomware (Calipso Version) has the capacity of taking a screenshot of the victim's Desktop when it first runs on the infected computer.
Both versions of the DetoxCrypto Ransomware are nearly identical; they first infect the victim's computer contained in an EXE file, which delivers four different files to the victim's computer. The following are the four files that have been linked to the DetoxCrypto Ransomware attack:
- The first file related to the DetoxCrypto Ransomware is the image file that is used to replace the victim's Desktop wallpaper image. In the case of earlier versions of the DetoxCrypto Ransomware, this image is related to the Pokemon GO game.
- The second of these files contains audio content, which is played in the background when the DetoxCrypto Ransomware ransom note is displayed on the infected computer.
- The DetoxCrypto Ransomware's actual file encryption process is carried out by a file named MicrosoftHost.exe. There is no relationship between this file or the DetoxCrypto Ransomware with Microsoft. Rather, this name is used to mislead computer users that check their Task Manager, since the file process will blend in with legitimate Microsoft and Windows memory processes.
- The fourth file linked to the DetoxCrypto Ransomware attack is a second executable file named either Calipso.exe or Pokemon.exe (depending on the version of the DetoxCrypto Ransomware attack) which displays the DetoxCrypto Ransomware's ransom note in an independent window while playing the audio file in the background.
The DetoxCrypto Ransomware may be the First Version of Its Kind
The DetoxCrypto Ransomware ransom note instructs computer users to contact the con artists using email, rather than using a TOR based payment method. The fact that two versions of the DetoxCrypto Ransomware were detected in such a short span of time could point either to a threat developer that is creating new versions of the DetoxCrypto Ransomware with new features, or configuration methods are being added. One reason why this is unlikely is the stark difference in the two methods of the attack. One is themed around Pokemon GO and uses fun, childish music. The other takes screenshots in the background and uses an audio file that reads out loud a ransom note that is worded more threateningly. One theory that could explain the DetoxCrypto Ransomware phenomenon is that these two versions of the DetoxCrypto Ransomware could belong to a new Ransomware as a Service (RaaS) that may have just begun to offer its services. In these services, con artists can purchase ransomware threats like the DetoxCrypto Ransomware that are customized to their specifications and managed by a party different to the one doing the distribution.
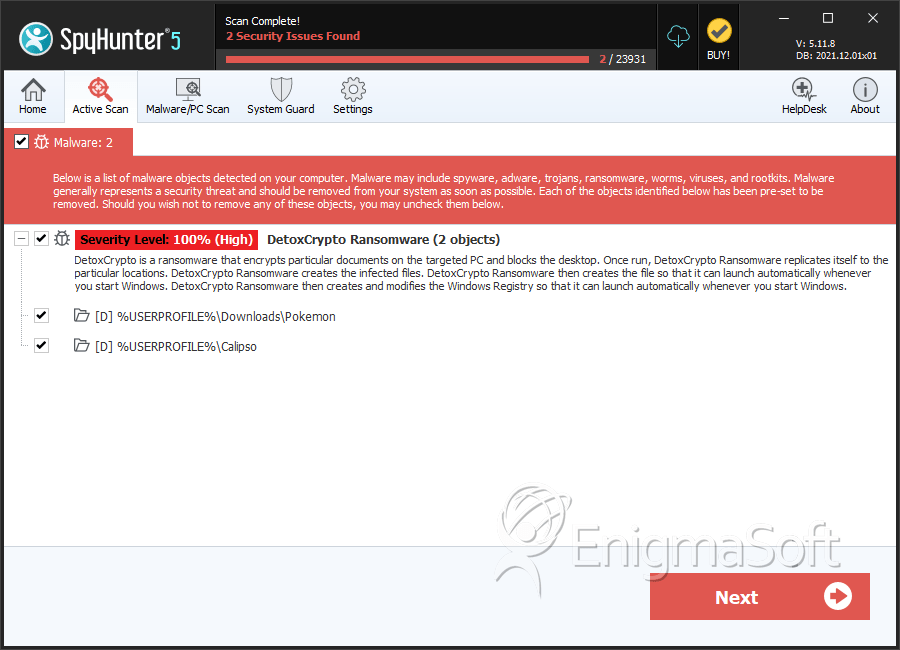
SpyHunter Detects & Remove DetoxCrypto Ransomware
Directories
DetoxCrypto Ransomware may create the following directory or directories:
| %USERPROFILE%\Calipso |
| %USERPROFILE%\Downloads\Pokemon |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.