XCrypt Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 20,323 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 24 |
| First Seen: | January 31, 2017 |
| Last Seen: | February 18, 2026 |
| OS(es) Affected: | Windows |
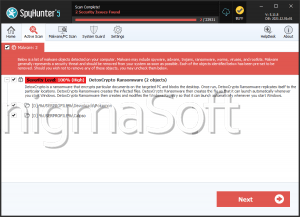
The XCrypt Ransomware was first observed on January 29, 2017. The XCrypt Ransomware is not based on an open source code or part of a RaaS (Ransomware as a Service) service, but that it seems to have been created independently. It is likely that the creator of the XCrypt Ransomware is located in Russia. The XCrypt Ransomware's ransom note, contained in a file named 'Xhelp.jpg,' has a Russian text. However, it does not seem that the XCrypt Ransomware targets computer users in Russia; attacks involving the XCrypt Ransomware have been detected all over the world and are not limited to Russian speakers.
Table of Contents
How the XCrypt Ransomware may Infiltrate a Computer
PC security analysts suspect that most of the XCrypt Ransomware infections are delivered using phishing email messages, which trick computer users into opening the included file attachment. Emails used to deliver the XCrypt Ransomware use falsified email addresses to make it seem as if the email is coming from a trusted source. Many of these emails will use social engineering techniques designed to trick computer users into opening a corrupted file attachment and downloading threats onto their computers. The XCrypt Ransomware can infect multiple versions of Windows, including both 32-bit and 64-bit operating systems. The XCrypt Ransomware is larger than many other ransomware Trojans, but it works fast and carries out an effective attack. The XCrypt Ransomware communicates with its Command and Control server using a Telegram channel, a method that has been abused by other ransomware Trojans in recent months.
How the XCrypt Ransomware Carries out Its Attack
Once the XCrypt Ransomware has infected a computer, it will communicate with its Command and Control server and relay information about the infected computer, including its location and information about its configuration. The XCrypt Ransomware encrypts the victim's files using the AES 256 encryption, a method that's typical of these attacks. The files encrypted by the XCrypt Ransomware will not have their name or extension changed, although they will no longer be accessible by the victim's applications. The XCrypt Ransomware targets numerous file types, including databases, spreadsheets, Office documents, images, videos and numerous others. The XCrypt Ransomware delivers its ransom note in a file named 'Xhelp.jpg' that contains a ransom message in Russian, which is reproduced below in translation to English:
'Your computer has been hacked! the XCrypt
All your files are now encrypted.
Unfortunately for you, the programmers and the police can not help you.
To decrypt, refer to the operator via ICQ.
IMPORTANT! Write down the number of our ICQ 714595302
The window is loaded on your desktop, but you can delete it and lose our contacts, thus lose all your files.
Icq 714 595 302'
Communicating with the People Responsible for the XCrypt Ransomware
Most ransomware Trojans avoid popular or commercial messaging platforms, usually opting for anonymous messaging services of some sort, or an email address from a private email server. The XCrypt Ransomware uses an unconventional approach, where victims are asked to communicate with the people associated with the XCrypt Ransomware via ICQ, a popular messaging platform. PC security researchers strongly advise computer users to avoid communicating with the people responsible for the XCrypt Ransomware attack and refrain from making any payments especially. Although the XCrypt Ransomware does encrypt the victim's files irreparably, con artists will rarely keep their promise to decrypt the affected files. In many cases, the victim's files will remain encrypted, and the con artists may ignore them or even ask for more money. Instead, take preemptive measures to limit the damage from attacks like the XCrypt Ransomware. Some ways in which you can protect your computer from these attacks include having backup copies of your files, on the cloud or an external memory device, and always using a reliable security program that is fully up-to-date. Backups allow you to recover your files after an attack especially.
Analysis Report
General information
| Family Name: | Trojan.Kryptik.KAA |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
6f1c969841a08b02db7e40a0e3de3932
SHA1:
2940a4b9e71912d93ea979118272452a0d26a243
SHA256:
E8E37E4EDFE4B1AF00DAF74EE04830467BFD9289CCA5D1A550A0069CFC57E7A4
File Size:
687.10 KB, 687104 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have exports table
- File doesn't have security information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.File Traits
- HighEntropy
- No Version Info
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 384 |
|---|---|
| Potentially Malicious Blocks: | 3 |
| Whitelisted Blocks: | 380 |
| Unknown Blocks: | 1 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block