Win.Trojan.Symmi
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 1,674 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 23,525 |
| First Seen: | December 3, 2012 |
| Last Seen: | April 2, 2026 |
| OS(es) Affected: | Windows |
Win.Trojan.Symmi is a computer Trojan horse that could perform several actions on your system where your personal information is put at risk of being stolen. The Win.Trojan.Symmi threat may load up from a malicious source and then open up access for remote attackers where they could infiltrate the infected system. Through Win.Trojan.Symmi data stored on the hard drive may be taken and potentially lead to identity theft and other serious issues. To eliminate the risks of Win.Trojan.Symmi actions it must be removed. Removal of Win.Trojan.Symmi may be done through the use of an antispyware tool capable of detecting and safely removing Trojan horse threats from a Windows computer.
Table of Contents
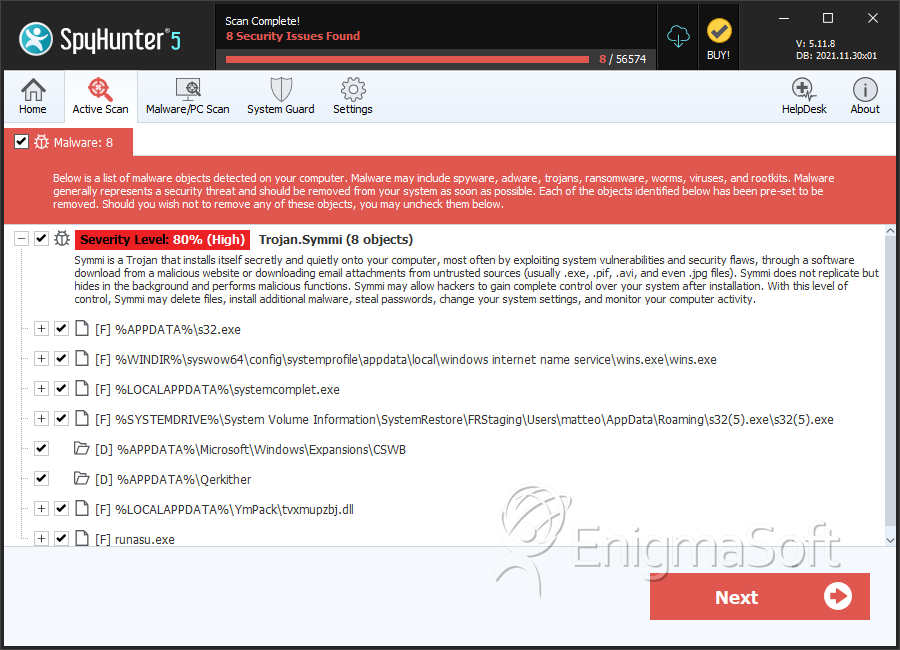
SpyHunter Detects & Remove Win.Trojan.Symmi
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | wins.exe | c11c83a7d9e7fa0efaf90cebd49fbd0b | 555 |
| 2. | s32(5).exe | 1eef5dc22d6e706c9573d1116107fc3b | 15 |
| 3. | systemcomplet.exe | 13434bbdf32856323ed5d58c827012fc | 10 |
| 4. | tvxmupzbj.dll | edc244ac5f6559f4f2808f037d3757f1 | 2 |
| 5. | s32.exe | 1caff1a22e6e0f482727924ec19343de | 1 |
| 6. | runasu.exe | 3a52b9faf8925c54c23bdc34b9395477 | 1 |
| 7. | secmanager.exe | 638180afb707955b12c7ef7269eb33a3 | 1 |
| 8. | 3855a3d17767b15b46fa1226cf5dd8f6 | 3855a3d17767b15b46fa1226cf5dd8f6 | 1 |
| 9. | name.exe | 58acfddd2e027434835f0334d58f2f17 | 0 |
| 10. | file.exe | 3b8a9cd288e85f4a6120971e32e4e1ed | 0 |
Directories
Win.Trojan.Symmi may create the following directory or directories:
| %APPDATA%\Microsoft\Windows\Expansions\CSWB |
| %APPDATA%\Qerkither |
Analysis Report
General information
| Family Name: | Trojan.Symmi |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
8034aa3b4a130c0761c97c49fa643279
SHA1:
03e2f9f94422d757a4057e945bf1dcbee345a88c
SHA256:
E501844C1CCB199324247B422CA1E34E69A50EA3E7045B47D270DAF2930EC9E1
File Size:
51.71 KB, 51712 bytes
|
|
MD5:
2e92af650f5626711646d4f965a048c7
SHA1:
6a01ab72da58f347ed10161838c16bfb77d6c288
SHA256:
4485DDB6D7E982E424D42C3EA2AEF41990BF2D265087FE8412DE90A40DDD4F31
File Size:
138.30 KB, 138301 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File has exports table
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
Show More
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Comments | Simple Program Skeleton. |
| Company Name | PowerBASIC, Inc. |
| File Description | Application |
| File Version |
|
| Internal Name |
|
| Legal Copyright | Copyright (c) 1997-2002 PowerBASIC, Inc. |
| Legal Trademarks | PowerBASIC is a trademark of PowerBASIC, Inc. |
| Original Filename |
|
| Product Name |
|
| Product Version |
|
File Traits
- 2+ executable sections
- SusSec
- vb6
- x86
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Other Suspicious |
|
