Web App Security Email Scam
In today's threat landscape, email remains one of the most common entry points for cyberattacks. Users must stay vigilant when dealing with unexpected messages, especially those urging immediate action. Many of these emails are carefully crafted scams, and it is important to understand that they are not associated with any legitimate companies, organizations, or entities, despite how convincing they may appear.
The 'Web App Security' Email Scam Explained
Security researchers have identified the so-called 'Web App Security' emails as a classic phishing campaign. These messages are designed to impersonate notifications from email service providers, creating a false sense of urgency and legitimacy.
Typically, the email claims that the recipient's account has been disconnected from sending and receiving messages. To resolve the issue, users are instructed to confirm whether their account is still active. A prominent link, often labeled 'Re-confirm account', is included, supposedly to restore normal functionality.
In reality, this link redirects users to a fraudulent website that closely imitates well-known email platforms such as Gmail or Yahoo Mail. The primary objective is to trick recipients into entering their login credentials.
How the Scam Compromises Users
Once a victim submits their email credentials on the fake site, attackers gain full access to the account. This access can be exploited in several dangerous ways:
- Sending scam emails to contacts to expand the attack
- Harvesting sensitive data stored in emails
- Attempting to reset passwords for other linked accounts
- Distributing malware or malicious links
- Gaining access to services like banking, social media, or gaming platforms
This chain reaction can quickly escalate beyond a single compromised account, affecting multiple aspects of a victim's digital life.
The Real Risks Behind the Attack
Falling victim to this phishing scam can lead to serious consequences. Cybercriminals leverage stolen information for identity theft, financial fraud, and reputational damage. In some cases, compromised accounts are used as launchpads for broader attacks, increasing the overall impact.
Beyond credential theft, these emails may also serve as malware delivery mechanisms. Attachments or links included in such messages can install harmful software on a device without the user realizing it.
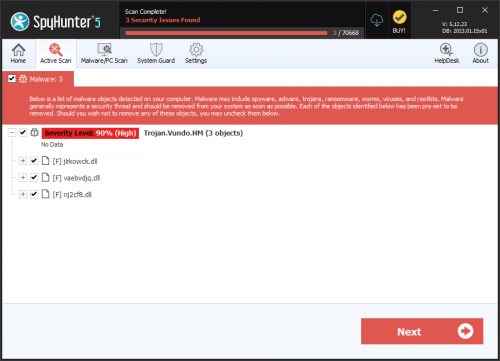
Malware Delivery Through Deceptive Emails
Phishing emails often go beyond simple credential theft. They may include attachments or links that install malicious software when opened or clicked. Common delivery methods include:
- Executable files that run harmful programs
- Office documents or PDFs embedded with malicious code
- Compressed archives such as ZIP or RAR files
- Scripts that trigger unauthorized actions on the system
In some cases, visiting a malicious website alone can initiate a silent download, infecting the device without any visible warning.
Final Thoughts: Recognizing and Avoiding the Trap
The 'Web App Security' email scam is a textbook example of how attackers exploit trust and urgency. By mimicking legitimate services and prompting quick action, these emails aim to bypass user caution.
Recognizing the signs of phishing, unexpected alerts, urgent requests, and suspicious links, is essential. Maintaining a cautious approach to unsolicited emails is one of the most effective defenses against such threats.