vSkimmer
Vskimmer is a dangerous Trojan and botnet that is specifically designed to target credit card terminals and point of sale devices, making its attack particularly effective at stealing credit card and banking credentials. ESG security researchers have observed that Vskimmer has been sold on Russian hacking forums and that its makers claim that Vskimmer can be utilized to rob credit card details from point of sale machines using the Windows operating system. Vskimmer detects credit card readers connected to the victim's computer, steals information associated with these readers and then sends this data to a third party at a remote location. These kinds of attacks have been seen before, particularly in the dangerous Dexter Trojan. In fact, Vskimmer seems to be a continuation of Dexter. However, criminals have now integrated even more sophisticated functions into this malware attack.
Table of Contents
How Vskimmer Differs from Known Banking Trojans
Highly effective banking Trojans like Zeus or Zbot have existed for years and have been developed to use very advanced techniques to steal credit card and online banking information. However, Vskimmer uses a different approach. While traditional banking Trojans launch as bigger a net as it can, hoping to target computer users that regularly use credit cards to make online payments and that access their bank accounts online, malware like Vskimmer are designed to infect fewer computers. However, since the computers targeted by Vskimmer are point of sale machines that are attached to credit card readers, this means that a single Vskimmer infection can result in dozens, if not hundreds of compromised credit cards or bank accounts in a single day.
Vskimmer was first observed in February of 2013. However, similar Trojans have been tormenting PC users for at least twosome years. To install itself, Vskimmer uses standard Worm and Trojan techniques, often installed on the victim's computer through an infected USB device. Basically, Vskimmer scans memory processes on the victim's computer in order to extract credit card information being processed through a credit card reader. Vskimmer then encodes this information using B64 encryption and, using standard HTTP protocol, connects to its Command and Control server. Since Vskimmer is designed to steal Track 2 data from credit cards (including full credit card number, confirmation code and expiration date), all stolen credit cards can then be used to make fraudulent purchases almost immediately, making Vskimmer a severe threat.
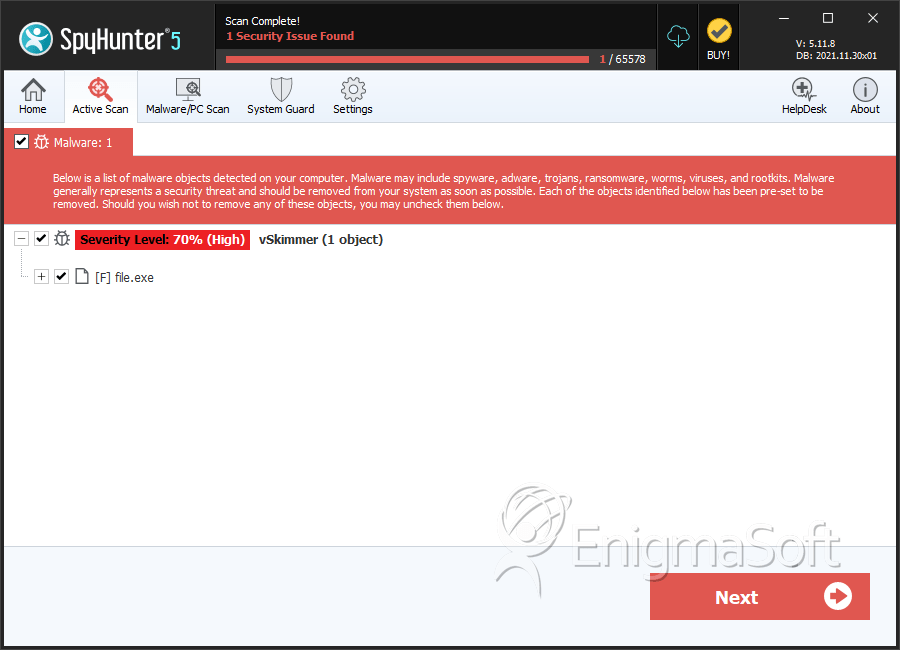
SpyHunter Detects & Remove vSkimmer
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | dumz.log | ||
| 2. | file.exe | 1075322594dd96e10d28bd5ec502f271 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.