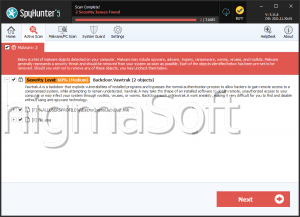
Vawtrak
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 10 % (Normal) |
| Infected Computers: | 2 |
| First Seen: | September 11, 2014 |
| Last Seen: | November 5, 2020 |
| OS(es) Affected: | Windows |
A modified version of the banking malware Vawtrak was discovered and considered to be among the most advanced threats. Vawtrak was first detected in June 2014, targeting users in the USA. Vawtrak is also known as Neverquest and part of the Gozi family of malware, classified as one of the most dangerous computer threats - Trojans. This malware is specially designed to target bank accounts of several people. The threat may gain unauthorized access to a number of platforms and systems and let cybercriminals perform their malicious goals. Vawtrak may expose your computer to a serious risk - including your personal information, e-mail credentials and usernames and passwords for online accounts.
Table of Contents
What is New in this Modified Version of the Vawtrak Banking Malware?
The initial version of Vawtrak was used to target financial institutions and people primarily in Japan. The modified version, however, extends its range to computers in the USA, Canada, the UK, Australia, Turkey and Slovakia. Besides financial institutions, the Vawtrak menace spreads to social networks, e-commerce sites, game portals among other sites. At the moment, security experts warn that the danger of Vawtrak is expected to increase in the future. This is based on the fact that recently some of the largest botnets as Shylock and Gameover Zeus were taken down, and this makes it easy for Vawtrak to step in.
How does It Spread?
In most cases, users cannot provide information about the way their PC has been infected. The Trojan doesn't need your permission to install but counts on Internet vulnerabilities. You can unintentionally download this threat by visiting malicious links, suspicious sites (including porn sites), opening the attachment of a spam e-mail and other dangerous activities. Computer security analysts report that in its latest action Vawtrak relied on Cutwail, the largest spam botnet at the moment. The Trojan used the brand names of AT&T and DocuSign in order to mislead the users and transfer them to an exploit kit. Vawtrak was also spread through fake e-mails from payroll services such as ADP. These e-mails contained a malicious attached file they claimed to be an invoice. Other methods of misleading users involve ‘important’ e-mail notifications for tax payments. The cybercriminals were even able to add the Google's URL Shortener to their kit of tools by sending seemingly innocent links to Dropbox, that, in fact, lead to compromised sites.
What Makes the Threat so Great?
Once Vawtrak has been successfully installed on your machine, it will be very difficult to detect this Trojan. Vawtrak is very good at avoiding interception by anti-spyware programs because Vawtrak uses a range of stealth methods. One of the features of this Trojan is the ability to overspread its vicious codes in the Kernel of your OS that in turn will provide the Vawtrak operators with full control over your PC.
To make the danger even greater, Vawtrak has used sophisticated Web injects which let it Vawtrak alter the Internet traffic information. As a result of this, the malware is able not only to obtain user names and passwords but also perform transactions automatically from your bank accounts. If you are aware that your PC is contaminated with Vawtrak, you shouldn't perform any actions associated with sensitive information.
Vawtrak represents a severe threat, and the experts anticipate in the future this Trojan's field of action to cover more industries so the necessary measures should be taken seriously. These actions include not performing any personal business - like using your bank account - on open networks. It is also highly recommended to have a powerful anti-spyware software and keep it up-to-date.


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.