Tunca Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 3 |
| First Seen: | January 4, 2019 |
| Last Seen: | October 24, 2025 |
| OS(es) Affected: | Windows |
The Tunca Ransomware is an encryption ransomware Trojan that carries out a typical version of this attack, encrypting the victim's files to take them hostage and then demanding a ransom payment from the victim. These attacks are becoming more common increasingly, and it is important that computer users take steps to protect their data preemptively by establishing file backups and installing a security program that is fully up to date.
Table of Contents
How the Tunca Ransomware Carries Out Its Attack
The Tunca Ransomware seems to be in development and is deployed using the Microsoft .NET framework. The Tunca Ransomware uses a strong encryption algorithm to make the victim's files inaccessible, adding the file extension '.tunca' to each file encrypted by the attack. The Tunca Ransomware targets the following file types in these attacks:
.jpg, .jpeg, .raw, .tif, .gif, .png, .bmp, .3dm, .max, .accdb, .db, .dbf, .mdb, .pdb, .sql, .dwg, .dxf, .cpp, .cs, .h, .php, .asp, .rb, .java, .jar, .class, .py, .js, .aaf, .aep, .aepx, .plb, .prel, .prproj, .aet, .ppj, .psd, .indd, .indl, .indt, .indb, .inx, .idml, .pmd, .xqx, .xqx, .ai, .eps, .ps, .svg, .swf, .fla, .as3, .as, .txt, .doc, .dot, .docx, .docm, .dotx, .dotm, .docb, .rtf, .wpd, .wps, .msg, .pdf, .xls, .xlt, .xlm, .xlsx, .xlsm, .xltx, .xltm, .xlsb, .xla, .xlam, .xll, .xlw, .ppt, .pot, .pps, .pptx, .pptm, .potx, .potm, .ppam, .ppsx, .ppsm, .sldx, .sldm, .wav, .mp3, .aif, .iff, .m3u, .m4u, .mid, .mpa, .wma, .ra, .avi, .mov, .mp4, .3gp, .mpeg, .3g2, .asf, .asx, .flv, .mpg, .wmv, .vob, .m3u8, .dat, .csv, .efx, .sdf, .vcf, .xml, .ses, .qbw, .qbb, .qbm, .qbi, .qbr , .cnt, .des, .v30, .qbo, .ini, .lgb, .qwc, .qbp, .aif, .qba, .tlg, .qbx, .qby , .1pa, .qpd, .txt, .set, .iif, .nd, .rtp, .tlg, .wav, .qsm, .qss, .qst, .fx0, .fx1, .mx0, .fpx, .fxr, .fim, .ptb, .ai, .pfb, .cgn, .vsd, .cdr, .cmx, .cpt, .csl, .cur, .des, .dsf, .ds4, , .drw, .eps, .ps, .prn, .gif, .pcd, .pct, .pcx, .plt, .rif, .svg, .swf, .tga, .tiff, .psp, .ttf, .wpd, .wpg, .wi, .raw, .wmf, .txt, .cal, .cpx, .shw, .clk, .cdx, .cdt, .fpx, .fmv, .img, .gem, .xcf, .pic, .mac, .met, .pp4, .pp5, .ppf, .nap, .pat, .ps, .prn, .sct, .vsd, .wk3, .wk4, .xpm, .zip, .rar.
The purpose of these attacks is to take the victim's files hostage, making them inaccessible so that there's no option but to make a ransom payment to access the files.
The Tunca Ransomware Ransom Demand
The Tunca Ransomware displays a pop-up window as a ransom note, which when clicked on displays an error message, making it apparent that the Tunca Ransomware Trojan may still be in development since its ransom note contains several bugs. The Tunca Ransomware ransom note's content, which appears in the Tunca Ransomware's pop-up window, reads:
'Ooops, it seems like all of your files have been encrypted with AESencryption algorithm.
Can I get my files back?
-Yes, you can. But you need this following software :
KGDecrypt
- Without the software, no one can decrypt your files
How do I pay?
-Simply buy a 100€ Paysafecard
-Send message with the Paysafecard PIN to this account :
Lockify@protonmail.com
-Wait for us to confirm your payment
-Get the decryptor
However, there is a way to get a free decryptor!
How to get the free decryptor?
-Create a link on grabify that will download your victim the ransomware
-With this, infect at least 10 people
-Send proof to : Lockify@protonmail.com
-Get your decryptor'
The Tunca Ransomware demands its ransom payment in the form of PaySafe cards, a somewhat outdated sort of payment that predates the rise of the cryptocurrency. Today, the preferred anonymous payment method by these threats is Bitcoin. The use of outdated payment methods and buggy software makes it apparent that the criminals behind the Tunca Ransomware attack do not have many resources or this is not a high-profile operation.
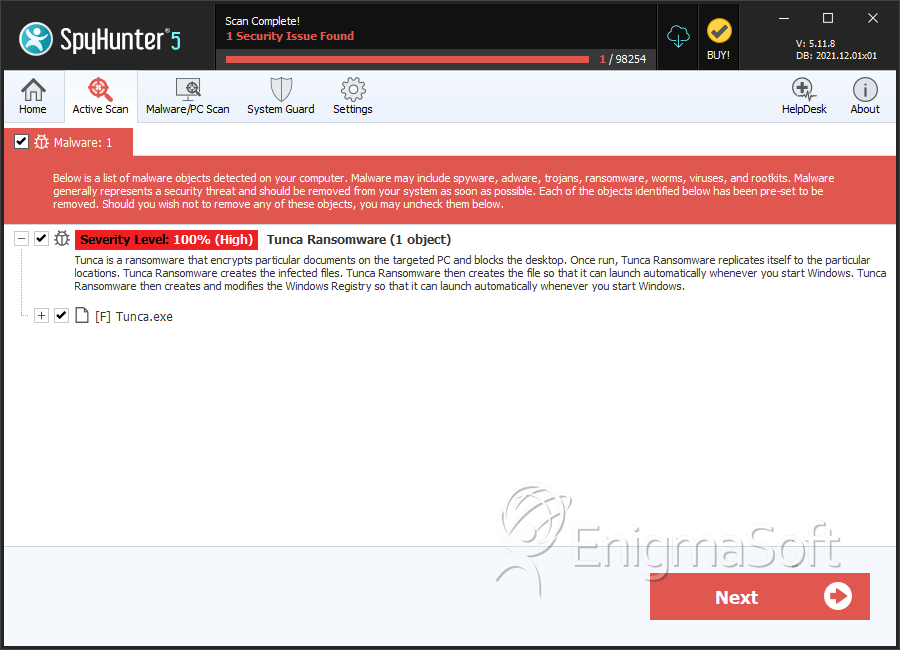
SpyHunter Detects & Remove Tunca Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | Tunca.exe | 84b23f8b1b69b63e1b9346e04497db18 | 1 |
