Taro Ransomware
The rise of sophisticated ransomware families highlights the need for strong digital security practices. Malicious software such as Taro Ransomware can compromise systems, steal sensitive data, and deny victims access to their files. Once executed, ransomware quickly locks up critical data, and criminals use fear and urgency to extort money. Users and organizations must be aware of such threats and know how they operate in order to adopt preventative measures and avoid devastating consequences.
Table of Contents
Taro Ransomware in Focus
Taro is a recently identified ransomware strain belonging to the MedusaLocker family. Like its counterparts, it encrypts files on infected machines and then demands payment for their recovery. During testing, researchers observed that Taro appended the '.taro' extension to encrypted files, making them instantly recognizable. For example, '1.jpg' was renamed to '1.jpg.taro'.
Once the encryption phase is complete, Taro drops a ransom note named '!!!HOW_TO_DECRYPT!!!.mht'. This note outlines the attackers' demands, specifying that files were encrypted using AES-256, RSA-2048, and CHACHA algorithms. Victims are told to contact the criminals for decryption and are offered a 'proof-of-concept' in which three non-sensitive files can be decrypted for free. In addition to file encryption, the note clarifies that data exfiltration has occurred, meaning stolen files may be leaked if the ransom is not paid.
The Danger of Paying the Ransom
While Taro's operators promise decryption after payment, history shows that victims cannot rely on cybercriminals to keep their word. Paying the ransom not only funds criminal operations but leaves victims with no data recovery guarantee. Some ransomware campaigns never provide keys, and even if decryption is offered, sensitive data may still be leaked on the darknet.
The most reliable way to restore affected files is through secure, offline backups created prior to infection. Unfortunately, removal of the ransomware itself will not reverse the damage already done to encrypted files.
Infection Vectors Behind Ransomware
Taro ransomware, like many similar threats, spreads primarily through phishing campaigns, trojans, and malicious downloads. Criminals disguise infected files as legitimate documents, installers, or compressed archives, tricking users into executing them. Spam emails often include malicious attachments or links that start the infection chain when clicked.
Other infection methods include drive-by downloads, compromised peer-to-peer file-sharing platforms, cracked software tools, and fake software updaters. Some ransomware variants can also spread laterally across networks or via removable drives, expanding the scope of the compromise beyond the initially infected device.
Best Practices to Boost Device Security
Defending against ransomware like Taro requires a proactive and layered security strategy. While no single measure guarantees complete safety, implementing the following practices significantly reduces the risk of infection:
- Maintain Secure Backups – Store backups on disconnected external devices or in trusted cloud services. Multiple copies should be kept in separate locations to ensure recovery options, even if one backup is compromised.
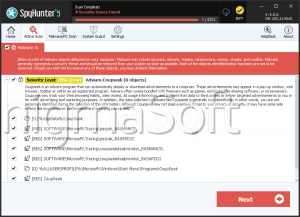
- Use Reliable Security Software – Keep anti-malware tools active and updated to detect and block real-time threats.
In addition to these critical steps, users must remain vigilant when handling online content. Avoid downloading from unverified sources and only install applications from official developer websites. Email attachments and links from unknown or suspicious senders should never be opened, as they are common vehicles for ransomware. Regular updates and patches for the operating system and software close vulnerabilities that attackers often exploit.
Practicing the principle of 'least privilege' by limiting administrative access to only when absolutely necessary also helps minimize potential damage. For organizations, network segmentation and strong access control can prevent ransomware from spreading laterally within a corporate environment.
Final Thoughts
Taro Ransomware illustrates the evolving and destructive nature of modern cyber threats. Its strong encryption, data theft component, and extortion tactics make it particularly dangerous for individuals and organizations. While the temptation to pay the ransom may be strong, it is rarely a viable solution and often results in further losses.