SuperB Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
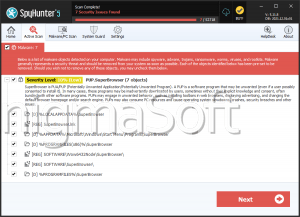
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 6 |
| First Seen: | September 13, 2017 |
| Last Seen: | October 21, 2020 |
| OS(es) Affected: | Windows |
The SuperB Ransomware is a new encryption ransomware Trojan. The SuperB Ransomware is designed to infect a computer and encrypt the victim's files, with the aim of demanding a ransom payment in exchange for a decryption key or software. The SuperB Ransomware is a recent newcomer, so there is very little information about how the SuperB Ransomware works. However, it is likely that the SuperB Ransomware is nearly identical to the many encryption ransomware Trojans that are active currently. The SuperB Ransomware has its own payment website, which includes options for payment and various other pages. The SuperB Ransomware demands a ransom of 300 USD in Bitcoins approximately to be paid to a specific Bitcoin wallet. The SuperB Ransomware infections can be identified easily because the files encrypted by the SuperB Ransomware attack will be marked with the file extension '.superB,' added to the file's name. The SuperB Ransomware website even includes a support page to help victims through the payment process. The SuperB Ransomware includes a captcha code when victims enter their ID to pay the ransom amount (this ID is displayed in the SuperB Ransomware's ransom note). The victims of the SuperB Ransomware attack must provide their email address when making the ransom payment. It is likely that the SuperB Ransomware is linked to other known online tactics.
What is the Work of Hoaxes Like the SuperB Ransomware
Ransomware Trojans like the SuperB Ransomware all use similar attacks. The main purpose of the SuperB Ransomware is to encrypt the victim's files using a strong encryption algorithm. Once the victim's files are encrypted, they become inaccessible. The SuperB Ransomware then demands the payment of a ransom in exchange for the decryption key or software needed to recover the files. The most common way of delivering ransomware Trojans like the SuperB Ransomware to victims is through the use of spam emails. The victims will receive spam email messages disguised as legitimate emails from a social media platform, a shipping company, or some other legitimate source. The message may mislead the victims to convince them to open an attached file. For example, the email may claim that the attached file is an invoice from a shipping company or a picture sent from social media. If the victim opens the attached file, the SuperB Ransomware will be downloaded and installed on the victim's computer. As soon as the SuperB Ransomware is installed, it begins carrying out its attack. Because of this delivery method, learning to recognize and avoid these misleading emails is a fundamental part of preventing attacks such as the SuperB Ransomware.
Recovering from a SuperB Ransomware Infection
The people responsible for the SuperB Ransomware claim to contact the victims within 24 hours after the payment. Supposedly, if the victims pay the ransom amount, then the victim's files will be decrypted. However, computer users should avoid paying the SuperB Ransomware ransom, since in these attacks there is no guarantee that the data will be recovered. PC security researchers instead advise computer users to remove the SuperB Ransomware immediately with the help of a reliable security program. Since the SuperB Ransomware uses a combination of the RSA 2048 and the AES 256 encryptions to make the victim's files inaccessible, the data encrypted in the SuperB Ransomware cannot be restored, and victims will have to rely on file backups to replace the files lost in the SuperB Ransomware attack. The SuperB Ransomware may still be unfinished. This is because the SuperB Ransomware's ransom note offers a YouTube link supposedly to provide more instructions. However, this YouTube video is not online currently. Since it seems that some aspects of the SuperB Ransomware are still changing, it is possible that different versions of the SuperB Ransomware may appear in the near future.


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.