SocGholish
SocGholish Image
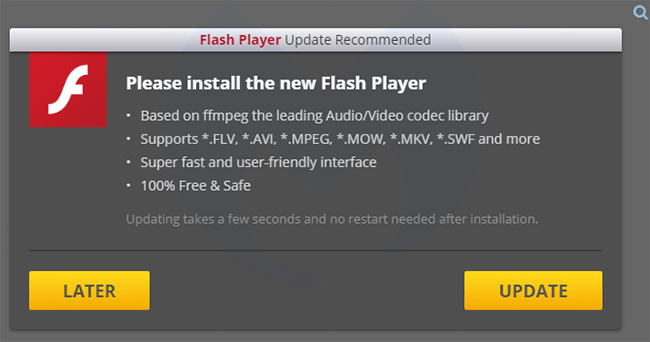
SocGholish is the name given by infosec researchers to an infrastructure set up by cybercriminals to perform drive-by download attacks. The framework makes liberal use of various social engineering and manipulative tactics that lead users to the infected staging website. SocGholish attempts to trick its targets into executing the corrupted ZIP files it delivers by pretending that they are legitimate updates for browser, Flash, or Microsoft Teams. The primary delivery method is through iFrames that overlay a legitimate website with a corrupted version without the user's knowledge. By leveraging iFrames, the hackers can bypass Web filtering because the website categories are delivered from legitimate ones.
Unlike some of the previously detected drive-by infrastructures, SocGholish doesn't rely on browser vulnerabilities or exploit kits to infect its targets. Instead, it is capable of performing three different techniques. The first one sees the cybercriminals establish a watering hole attack. They target websites with high amounts of traffic and inject iFrames into them. Users who visit the already tampered sites will be taken through several redirects until landing on site delivering a corrupted ZIP file. The second technique involves the injection of iFrames into content management systems. The drive-by download of the corrupted files is triggered through JavaScript blobs. The third method sees SocGholish leverage JavaScript again alongside sites.google.com to generate download links leading to the corrupted file dynamically. The ZIP archive, in this case, is hosted on a legitimate Google Drive while the download is initiated through a simulated mouse click.
Researchers note that the file delivered by the drive-by attack usually acts as a first-stage payload. It is tasked with scanning the infected system, fetching the intermediate payload, or the final malware threat and executing it. SocGholish has been reported to ultimately deploy the Dridex banking Trojan or a variant of the WastedLocker Ransomware on the compromised computer.

