ShadyPanda Malicious Browser Extensions
In a striking example of long-term cyber exploitation, a threat actor known as ShadyPanda has conducted a seven-year campaign targeting browser extensions, accumulating over 4.3 million installations. This operation demonstrates how even legitimate software can be weaponized when proper oversight is absent.
Table of Contents
From Legitimate Tools to Malicious Updates
Five of the compromised extensions began as legitimate applications but were modified with malicious functionality in mid-2024. These updates attracted roughly 300,000 installs before the extensions were eventually removed. The malicious updates enabled hourly remote code execution, allowing attackers to download and run arbitrary JavaScript with full browser access. Once active, these extensions:
- Monitor every website visited.
- Exfiltrate encrypted browsing history.
- Collect complete browser fingerprints.
A notable example is Clean Master, which was previously verified by Google. Its official status helped ShadyPanda expand its user base, enabling malicious updates without raising suspicion.
Mass Surveillance Through Popular Add-Ons
Another set of five extensions, including WeTab, monitored users on a massive scale. These add-ons tracked URLs, search engine queries, mouse clicks, and other browser interactions, transmitting the data to servers based in China. Collectively, these extensions were installed approximately four million times, with WeTab alone accounting for three million installs.
Early indications of malicious behavior appeared in 2023, involving developers' nuggetsno15' and 'rocket Zhang,' who published 20 Chrome extensions and 125 Edge extensions disguised as wallpaper or productivity tools.
Exploiting Affiliate Fraud and Browser Hijacking
ShadyPanda's extensions initially engaged in affiliate fraud, injecting tracking codes into sites such as eBay, Amazon, and Booking.com to generate illicit commissions. By early 2024, the tactics escalated to active browser control, including:
- Search query harvesting.
- Redirecting searches through trovi.com, a known hijacker.
- Exfiltrating cookies from targeted domains.
By mid-2024, three extensions with long-standing legitimate use were modified to fetch hourly JavaScript payloads from 'api.extensionplay(dot)com,' executing them to monitor every site visit and transmit encrypted data to 'api.cleanmasters(dot)store.' The payloads were heavily obfuscated and entered benign mode if developer tools were detected, helping the malware evade detection.
Advanced Attack Capabilities
Beyond tracking, these extensions could stage adversary-in-the-middle (AitM) attacks, facilitating:
- Credential theft.
- Session hijacking.
- Arbitrary code injection on any site.
The surveillance intensified with Microsoft Edge add-ons like WeTab, which captured extensive user interactions, including scrolling behavior, time spent on pages, and all browser fingerprints. These extensions are no longer available for download from their respective marketplaces.
Recommended Actions for Users
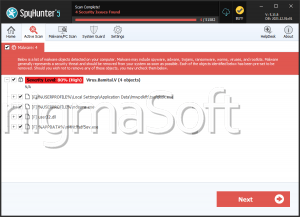
This campaign progressed through four distinct phases, evolving from legitimate tools to sophisticated spyware. While it's unclear if download counts were artificially inflated to appear legitimate, the risk to users remains severe. Users who installed any of these extensions should remove the extensions immediately and rotate passwords for all online accounts.
Examples of affected extensions:
- Clean Master: the best Chrome Cache Cleaner
- Speedtest Pro-Free Online Internet Speed Test
- BlockSite
- Address bar search engine switcher
- SafeSwift New Tab
- Infinity V+ New Tab
- OneTab Plus: Tab Manage & Productivity
- WeTab 新标签页
- Infinity New Tab for Mobile
- Infinity New Tab (Pro)
- Infinity New Tab
- Dream Afar New Tab
- Download Manager Pro
- Galaxy Theme Wallpaper HD 4k HomePage
- Halo 4K Wallpaper HD HomePage
- Lessons from ShadyPanda
ShadyPanda's success underscores that technical sophistication alone isn't necessary, the campaign thrived by exploiting a systemic vulnerability in browser extension marketplaces. Extensions are reviewed upon submission, but post-approval behavior is largely unmonitored. This long-term oversight gap allowed trusted tools to quietly evolve into surveillance platforms, highlighting the need for constant vigilance, even with verified software.