Ripper Ransomware
Protecting personal and organizational devices from malware is no longer optional, it is essential. Modern threats are engineered to disrupt operations, steal sensitive information, and extort victims with alarming efficiency. Among these threats, ransomware stands out for its ability to instantly deny access to critical data while applying intense psychological pressure on victims to pay.
Table of Contents
Ripper Ransomware: An Emerging and Calculated Threat
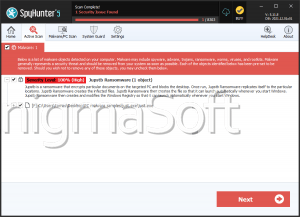
During recent malware investigations, cybersecurity analysts identified a sophisticated ransomware strain tracked as Ripper Ransomware. This threat is purpose-built to encrypt user files and make recovery difficult without attacker involvement. Once executed, Ripper systematically locks data and appends the '.ripper12' extension to affected files, transforming items like '1.png' into '1.png.ripper12' and '2.pdf' into '2.pdf.ripper12.' This clear marker signals that the encryption process has completed and the data is no longer accessible through normal means.
Visual Intimidation and Ransom Messaging
Beyond file encryption, Ripper employs intimidation techniques designed to reinforce the seriousness of the attack. It alters the desktop wallpaper and drops a ransom message titled 'READ_NOTE.html.' The note informs victims that their files are encrypted and explicitly warns against using third-party recovery tools or attempting manual file modification. According to the attackers, only they possess the means to restore access.
The message further escalates the pressure by claiming that confidential and personal data has been exfiltrated and stored on a remote server. Victims are told that this data will be destroyed only after payment, while failure to comply could result in public exposure or the sale of the stolen information. Communication is directed through specific email addresses or a Tor-based chat, with an added ultimatum that the ransom amount will increase if contact is not made within 72 hours.
The Reality of File Recovery and Ransom Payments
In most ransomware incidents, recovering encrypted data without a valid decryption key is extremely difficult. Unless victims have reliable backups or security researchers develop a free decryption utility, restoration options are limited. Even so, paying the ransom is strongly discouraged. There is no guarantee that cybercriminals will provide a working decryption tool, and payment only fuels further criminal activity. Compounding the issue, ransomware like Ripper may continue to cause damage while active, including spreading across local networks or triggering additional data loss, which makes rapid removal from infected systems critical.
How Ripper and Similar Ransomware Spread
Ripper follows well-established distribution patterns common to modern ransomware campaigns. Attackers often exploit outdated or unpatched software vulnerabilities and lure users through pirated applications, key generators, cracking tools, and unverified third-party downloaders. Infections may also originate from peer-to-peer networks, compromised USB devices, or malicious online advertisements.
Email-based attacks remain especially effective. Victims are frequently deceived into opening seemingly legitimate attachments, such as Word documents, PDFs, scripts, executables, ISO images, or compressed archives, which silently execute the ransomware once opened. Fraudulent support scams and compromised websites further expand the attack surface.
Strengthening Defenses: Best Security Practices That Matter
Building resilience against ransomware like Ripper requires a layered and disciplined security approach. Users should prioritize proactive defense rather than reactive recovery. Effective protection comes from maintaining regular offline or cloud-based backups, ensuring operating systems and applications are consistently patched, and relying on reputable security software with real-time protection.
Equally important is user awareness. Recognizing phishing attempts, avoiding pirated software, and exercising caution with email attachments and downloads significantly reduces infection risk. Network segmentation and restricted user privileges can also limit the spread of ransomware if an initial compromise occurs. When combined, these practices create a robust defensive posture that makes successful ransomware attacks far less likely.
Final Thoughts
Ripper Ransomware exemplifies how modern cyber threats blend technical sophistication with psychological coercion. By encrypting files, threatening data exposure, and imposing strict deadlines, it aims to force victims into rushed decisions. The most effective countermeasure remains prevention, through strong security hygiene, informed users, and reliable backups, ensuring that even if ransomware strikes, its impact is contained rather than catastrophic.