Razy Ransomware
Discovered in July of 2016, the Razy Ransomware infection is a ransomware Trojan. The Razy Ransomware will encrypt the victims' data using AES encryption. After the Razy Ransomware encrypts a file, it adds the extension '.the Razy' to the file's name. The Razy Ransomware does not target files with specific extensions (like most ransomware Trojans). Rather, the Razy Ransomware will target all files it finds in certain directories, regardless of their extensions. At the time this report was made, the Razy Ransomware targets files in the Music, Pictures, Videos and Documents folders, and on the victim's Desktop.
Table of Contents
The Razy Ransomware Destroys Your Files!
The Razy Ransomware does not save the decryption key, meaning that it is a purely destructive attack. Once the victim's files are encrypted, they cannot be decrypted… they may as well have been deleted. According to a Twitter account associated with the Razy Ransomware's developers, the Razy Ransomware was created for educational purposes, supposedly to 'educate' computer users on the dangers of ransomware. However, other 'educational' ransomware Trojans may provide a simple way for victims to recover their files. In the case of the Razy Ransomware, the victim's files will simply become useless after they have been encrypted. Strangely enough, the Razy Ransomware's 'PAY HERE' link in the ransom note leads nowhere. The Razy Ransomware simply does not ask for ransom or provide any way to recover the encrypted files. The Razy Ransomware uses an encryption method that is quite strong, with a 16-byte key.
Ransomware For Fun? Is the Razy Ransomware an 'Educational Threat'?
The creation of ransomware as a simple recreational or educational exercise has been a worrying trend in recent times. Unfortunately, even if the people responsible for these attacks have good intentions, in the end letting these threats loose simply result in innocent computer users losing their data. It is entirely possible that the original intent of the Razy Ransomware was good, but these publicly available threats have a way of becoming more threatening once con artists with less altruistic intentions take the threat's code and retool it for their own purposes. The Razy Ransomware is similar to thousands of other encryption ransomware Trojans and will make your data completely useless if the Razy Ransomware enters your computer. Even worse, computer users that have become infected with the Razy Ransomware will lose any chance of recovering their files. In the case of a 'non-educational' threat, at least the victim has a small chance of obtaining a decryption key if they are desperate enough to pay the ransom amount.
Dealing with and Preventing the Razy Ransomware Infections
The most common way in which ransomware threats like the Razy Ransomware are distributed is through the use of corrupted email messages and attack websites. Because of this, the best protection against these threats is to use caution when browsing the Web and especially when opening unsolicited email messages. A security program that is fully up-to shouldn't be underestimated. Since most of these threats are spread through emails, having a spam filter that can intercept these corrupted email messages before they even arrive is a good measure to ensure that your computer does not become infected.
If the Razy Ransomware has already encrypted your data, then it will be necessary to use a threat remover program that is fully up-to-date to remove the Razy Ransomware infection itself. Unfortunately, once the Razy Ransomware has been removed, the files that it affects will remain encrypted. In the case of the Razy Ransomware, computer users will have to restore their files using backup versions. In fact, having backups of all your files is the best protection against threats like the Razy Ransomware since they rely on the computer users' need to recover their files as leverage.
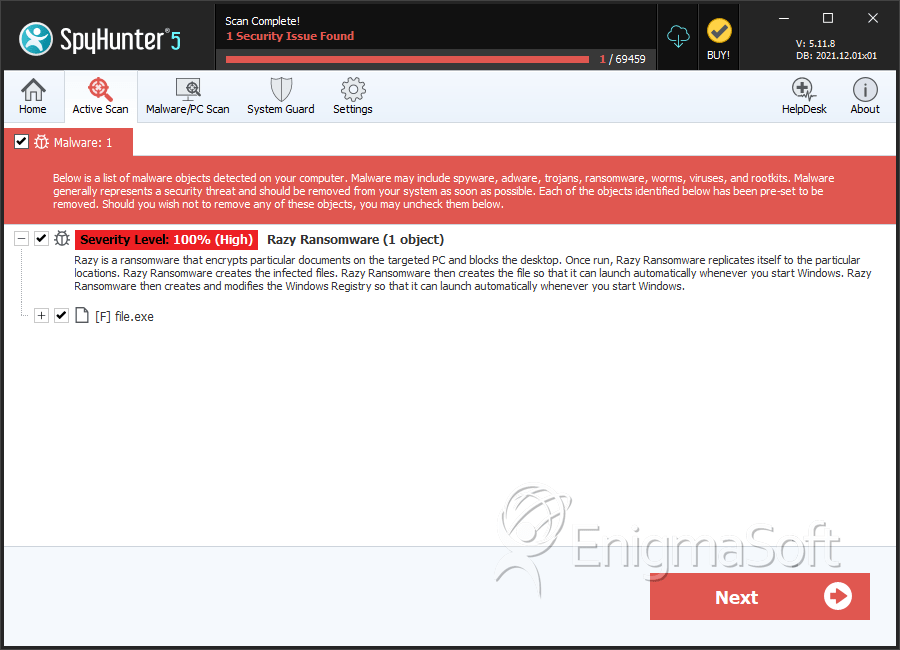
SpyHunter Detects & Remove Razy Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 93e551a1f52faea0d90ab9cd3d524ae9 | 0 |
| 2. | file.exe | ec9c3efe831aaa203058927df7de6138 | 0 |