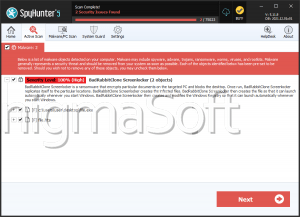
Rabbit Ransomware
The Rabbit Ransomware is a ransomware Trojan that functions by blocking access to the victim's computer. Threats like the Rabbit Ransomware are known as screen lockers because they are designed to block the victim's screen, and display a ransom note or error message to trick the victim into paying a ransom to regain access to the infected computer. There are many ransomware Trojans types, ranging in the extent and severity of the attack. The worst ransomware Trojans are designed to restrict access to the victim's computer entirely and encrypt the victim's files with an effectual encryption algorithm. Screen lockers like the Rabbit Ransomware are benign relatively since they do not harm the victim's files directly and can generally be bypassed, especially in the case of the Rabbit Ransomware where the password is coded into the Rabbit Ransomware itself, allowing PC security researchers to determine the unlock password easily. In the case of all ransomware Trojans, malware analysts strongly advise computer users to refrain from paying any ransom, which allows the criminals to continue developing and distributing threats like the Rabbit Ransomware, claiming new victims and carrying out more attacks.
How the Rabbit Ransomware and Similar Threats Carry Out These Attacks
The Rabbit Ransomware was first observed carrying out attacks on March 21, 2019. The Rabbit Ransomware can be distributed in several ways. The victims' computers, probably, were infected with the Rabbit Ransomware via bad spam email attachments, through bogus online downloads, and fake software or Web browser updates downloaded from shady websites. Once the Rabbit Ransomware is installed, it creates a lock screen, a full-screen message that prevents the victim from bypassing it or using the infected computer as normal. The Rabbit Ransomware will create a process in the Task Manager disguised as a Windows Update process. The Rabbit Ransomware also will make changes to the infected computer's Start-up software, allowing the Rabbit Ransomware to start up automatically whenever Windows is initialized.
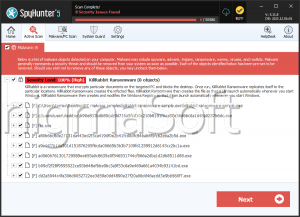
The Rabbit Ransomware's Ransom Note and Lock Screen
Once the Rabbit Ransomware has been installed, it carries out its attack every time Windows starts up. The Rabbit Ransomware displays a blue screen that is titled 'Your Windows has been infected by the Rabbit Ransomware!' The Rabbit Ransomware lock screen claims that Windows was locked and demands a ransom to be paid using digital currencies such as Bitcoin and Etherium. The Rabbit Ransomware provides the victim with a payment address. The Rabbit Ransomware displays a countdown timer apart from this message, claiming that the victim's files will be deleted when the countdown timer reaches zero. This allows the criminals to create an artificial sense of urgency, increasing the likelihood that the victims of the Rabbit Ransomware attack will pay the ransom. The Rabbit Ransomware ransom note includes a text box where the victim can enter an unlock password. Fortunately, the criminals have included this unlock password in the Rabbit Ransomware's code, allowing PC security researchers to uncover it to help the victims of the Rabbit Ransomware attack recover easily. The following is the lock screen message that the Rabbit Ransomware displays as part of its attack:
'Your Windows has been locked! IF you want to unlock it you must pay 0.005BTC or 0.15 ETH.
BTC Address: [QR code]
ETH Address: [QR code]
Time left: [24h countdown timer]
After time expired all files will be deleted!
When you send money on my address you need to send transaction id to prove transaction.
Unlock password: [text box] [Submit|BUTTON]'
The Rabbit Ransomware's unlock password is 'RabbCompany66', although it is possible that this may change for subsequent versions. Once the Rabbit Ransomware lock screen has been bypassed, malware diggers advise that computer users use a strong security program to remove the threat presented by the Rabbit Ransomware completely and prevent similar threats from infecting their PCs