KillRabbit Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 13 |
| First Seen: | August 12, 2018 |
| Last Seen: | September 10, 2021 |
| OS(es) Affected: | Windows |
The KillRabbit Ransomware is an encryption ransomware Trojan, which was first detected on August 8, 2018. The KillRabbit Ransomware is used to carry out a typical version of the encryption ransomware tactic. These attacks function by taking over the victim's computer by encrypting the victim's files using a strong encryption algorithm and then demanding the payment of a ransom from the victim in exchange for the decryption needed to restore the affected files. The KillRabbit Ransomware takes the victim's data hostage and then demands a ransom payment to restore access to the compromised files. The prevention of attacks such as the KillRabbit Ransomware and the protection of the integrity of the data can be accomplished by having anti-malware programs and file backups stored in a secure location.
Table of Contents
How You will Know that You Have Been Attacked by the KillRabbit Ransomware
Although the KillRabbit Ransomware operates like most encryption ransomware Trojans, the intended victims of the KillRabbit Ransomware attack have a higher profile than individual users, such as business networks and servers. The KillRabbit Ransomware is effective at encrypting large databases and the content that is associated with high-scale attacks particularly. The KillRabbit Ransomware demands a ransom payment using digital currency to restore the victim's files. The files encrypted by the KillRabbit Ransomware are marked with the file extension '.killrabbit,' added to the file's name. The files the KillRabbit Ransomware will target in these types of attacks include:
.ebd, .jbc, .pst, .ost, .tib, .tbk, .bak, .bac, .abk, .as4, .asd, .ashbak, .backup, .bck, .bdb, .bk1, .bkc, .bkf, .bkp, .boe, .bpa, .bpd, .bup, .cmb, .fbf, .fbw, .fh, .ful, .gho, .ipd, .nb7, .nba, .nbd, .nbf, .nbi, .nbu, .nco, .oeb, .old, .qic, .sn1, .sn2, .sna, .spi, .stg, .uci, .win, .xbk, .iso, .htm, .html, .mht, .p7, .p7c, .pem, .sgn, .sec, .cer, .csr, .djvu, .der, .stl, .crt, .p7b, .pfx, .fb, .fb2, .tif, .tiff, .pdf, .doc, .docx, .docm, .rtf, .xls, .xlsx, .xlsm, .ppt, .pptx, .ppsx, .txt, .cdr, .jpe, .jpg, .jpeg, .png, .bmp, .jiff, .jpf, .ply, .pov, .raw, .cf, .cfn, .tbn, .xcf, .xof, .key, .eml, .tbb, .dwf, .egg, .fc2, .fcz, .fg, .fp3, .pab, .oab, .psd, .psb, .pcx, .dwg, .dws, .dxe, .zip, .zipx, .7z, .rar, .rev, .afp, .bfa, .bpk, .bsk, .enc, .rzk, .rzx, .sef, .shy, .snk, .accdb, .ldf, .accdc, .adp, .dbc, .dbx, .dbf, .dbt, .dxl, .edb, .eql, .mdb, .mxl, .mdf, .sql, .sqlite, .sqlite3, .sqlitedb, .kdb, .kdbx, .1cd, .dt, .erf, .lgp, .md, .epf, .efb, .eis, .efn, .emd, .emr, .end, .eog, .erb, .ebn, .ebb, .prefab, .jif, .wor, .csv, .msg, .msf, .kwm, .pwm, .ai, .eps, .abd, .repx, .oxps, .do.
The KillRabbit Ransomware delivers a ransom note. The KillRabbit Ransomware's ransom note is fairly unique in that it is in PHP format, while most encryption ransomware Trojans use text files or HTA program windows. The KillRabbit Ransomware ransom note exhibits the content below:
'KillRabbit V2 – User Area
[Unique Key|TEXT BOX]
[Authorization|BUTTON]
Problems with authorization? Contact us> killrabbit@retwyware.pro
What Happened?
Oops, it seems the rabbit encrypted all of your files and requires a ransom for their decryption.
Do not worry, all your files will be decrypted after payment of the repayment.'
Protecting Your Data from Threats Like the KillRabbit Ransomware
The best protection against threats like the KillRabbit Ransomware is to have file backups stored on portable devices. Having file backups allows computer users and server administrators to bypass the KillRabbit Ransomware tactic and avoid having to contact the criminals responsible for the attack. Since the KillRabbit Ransomware's intended targets are high-profile victims such as servers and business networks, it is more likely that backup images of the content exist. Apart from file backups, a security program that is fully up-to-date can prevent the KillRabbit Ransomware attacks.
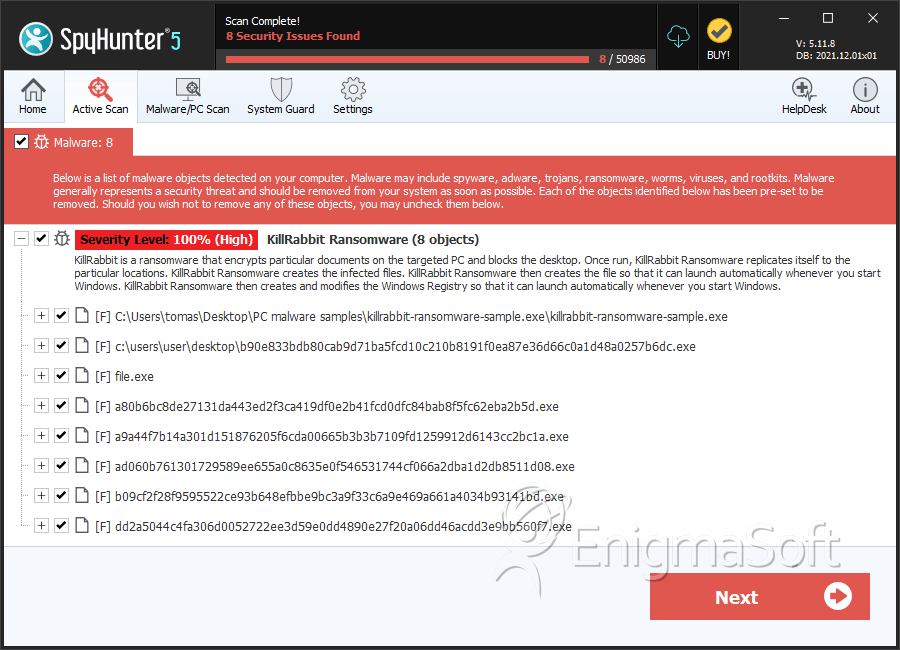
SpyHunter Detects & Remove KillRabbit Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | killrabbit-ransomware-sample.exe | f69cb073623d1cd054c140fc231fbeea | 6 |
| 2. | file.exe | 7b793a4247b701bd24c86920b237acd0 | 1 |
| 3. | b90e833bdb80cab9d71ba5fcd10c210b8191f0ea87e36d66c0a1d48a0257b6dc.exe | 93b0dba640906532bc2b2e848c28a743 | 1 |
| 4. | file.exe | 446575fbcef8f8febe96ffd8af0586b3 | 0 |
| 5. | file.exe | 72644c4f421917d61d9ce162843b7179 | 0 |
| 6. | a80b6bc8de27131da443ed2f3ca419df0e2b41fcd0dfc84bab8f5fc62eba2b5d.exe | 3169182b9a79f28210c70d931eade3dc | 0 |
| 7. | a9a44f7b14a301d151876205f6cda00665b3b3b7109fd1259912d6143cc2bc1a.exe | 5ba399bc866ca693b9376e1ec1858abb | 0 |
| 8. | ad060b761301729589ee655a0c8635e0f546531744cf066a2dba1d2db8511d08.exe | e16f1883caa6100590ddad506040d890 | 0 |
| 9. | b09cf2f28f9595522ce93b648efbbe9bc3a9f33c6a9e469a661a4034b93141bd.exe | 9b31f45253115c4e1ada74d06f867f01 | 0 |
| 10. | dd2a5044c4fa306d0052722ee3d59e0dd4890e27f20a06dd46acdd3e9bb560f7.exe | ccbf32ec653ced83d1f21b7e5eafd11f | 0 |
| 11. | fb211d128f24a92641d3950e6cb853f1b105b4d9b0840a512abafac86d0d805c.exe | f0da86d5cdff0025593dffa02df58f6c | 0 |

