Purge Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 321,805 |
| First Seen: | August 18, 2016 |
| Last Seen: | October 24, 2025 |
| OS(es) Affected: | Windows |
The Purge Ransomware is an encryption ransomware Trojan that uses the RSA encryption to encrypt its victims' files. The Purge Ransomware identifies files that have been encrypted by adding the extension '.the Purge' to each file's name. After encrypting the victim's files, the Purge Ransomware displays its ransom note, contained in the file 'How to restore files.hta'. Unfortunately, it is not possible to decrypt the files encrypted by the Purge Ransomware without access to the decryption key, which the con artists responsible for the Purge Ransomware hold hostage until the victim pays the ransom.
Table of Contents
Infected Computer Users should Abstain from Paying the Purge Ransomware Ransom
The Purge Ransomware ransom note claims that its victims have to contact the con artists at a specific email address (powerbase@tutanota.com) to receive instructions for payment. The Purge Ransomware demands ransoms that are between 1 and 3 BitCoins (between $600 and $1800 USD at the average exchange rate), making it particularly expensive to recover from a Purge Ransomware attack. It isn't a smart choice pay the Purge Ransomware's ransom. There is no guarantee that the con artists responsible for the Purge Ransomware will keep their word and deliver the decryption key; it is equally possible that they will turn around and ask for more money. Unfortunately, since it is not possible to restore the files without the decryption key, the best method computer users can use is to recover their files from a backup. This is, in fact, the best prevention method for dealing with the Purge Ransomware, having adequate backups of all files on an external memory device.
How Threats Like the Purge Ransomware Work
Threats like the Purge Ransomware are becoming very popular online. Most ransomware Trojans are very similar to each other, particularly because they may recycle code from one threat to the other. Virtually, the only practical differences are the size of the ransom demanded from the victims. The most common distribution methods for threats like the Purge Ransomware are corrupted email attachments, fake software updates, programs distributed through P2P networks, and hacking of victim's computers directly. Making sure that your computer is protected adequately with a reliable security program and that you exercise caution when dealing with possible infection sources can help prevent the Purge Ransomware attacks and other, similar infections. The ransom note displayed by the Purge Ransomware says:
YOUR FILES HAVE BEEN ENCRYPTED!
Your files have been been encrypted with a powerfull strain of a virus called ransomware. Your files are encrytped using rsa encryption, the same standard used by the military and banks. It is currently impossible to decrypt files encrypted with rsa encryption.
Lucky for you, we can help. We are willing to sell you a decryptor UNIQUELY made for your computer (meaning someone else's decryptor will not work for you). Once you pay a small fee, we will instantly send you the software/info neccessary to decrypt all your files, quickly and easilly.
In order to get in touch with us email us at powerbase@tutanota.com.In your email write your personal ID (its located at the up of the page, it is a string of random characters). Once we receive your personal ID, we will send you payment instructions.
As proff we can decrypt you files we may decrypt 1 small file for test.
If you dont get answer from powerbase@tutanota.com in 10 hours
Register here: hxxp://bitmsg.me
Write to adress BM-2cUrKsazEKiamN9cZ17xQq9c5JpRpokca5 with you email and personal ID
When you payment will bee confirmed, You will get decrypter of files on you computer. After you run decrypter software all you files will be decryped and restored. Do not try restore files without our help, this is useless and you may lose data permanetly. Decrypters of others clients are unique and work only on PC with they personal ID. We can not keep your decryption keys forever, meaning after 1 week after you have been infected, if you have not paid, we will not be able to decrypt your files. Email us as soon as you see this message, we know exactly when everyone has been encrypted and the longer you wait, the higher the payment gets.
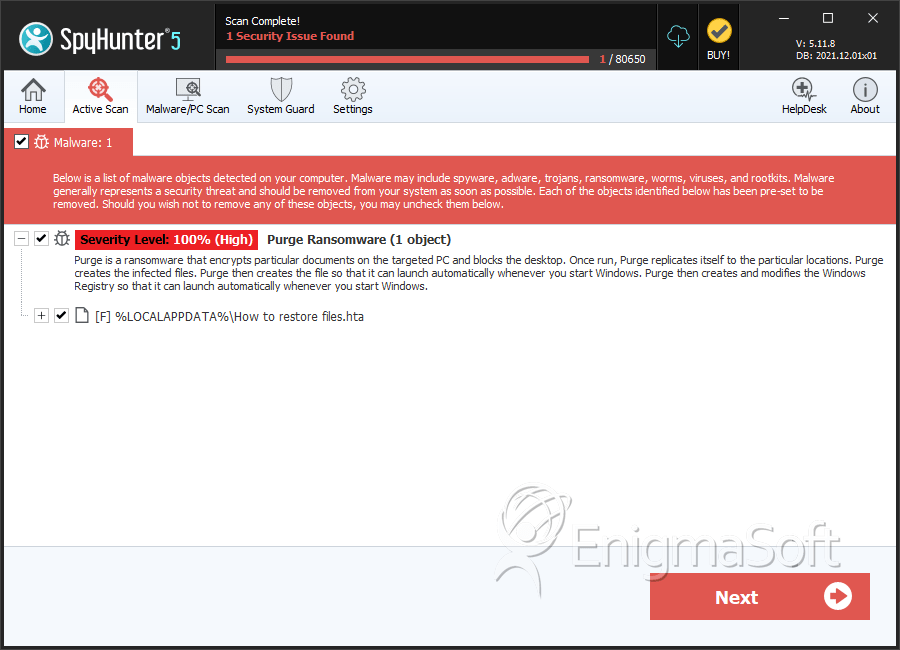
SpyHunter Detects & Remove Purge Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | How to restore files.hta | e949180e002c6bcb4206e6b23f8172de | 8 |
