Meldonii@india.com Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 79 |
| First Seen: | August 23, 2016 |
| Last Seen: | October 24, 2025 |
| OS(es) Affected: | Windows |
The 'Meldonii@india.com' Ransomware is a ransomware Trojan that is designed to encrypt the victims' files, taking them hostage in the process, and then demanding the payment of a ransom from the victims. Computer users should avoid paying the 'Meldonii@india.com' Ransomware's ransom. Victims of the 'Meldonii@india.com' Ransomware that have contacted the people responsible for the 'Meldonii@india.com' Ransomware have received unhelpful responses after paying close to $1000 USD in BitCoins. According to reports from victims of the 'Meldonii@india.com' Ransomware, the con artists responsible for this attack may ask for even more money from its victims instead of providing a way to decrypt the affected files. For example, a charity that was affected by the 'Meldonii@india.com' Ransomware has reported that they were asked to pay an additional $800 USD ransom after the initial $1000 USD payment and the supposed decryption key to remove the 'Meldonii@india.com' Ransomware never worked.
The Main Targets of the 'Meldonii@india.com' Ransomware are Enterprise Networks
The 'Meldonii@india.com' Ransomware is part of a large family of ransomware Trojans that use the extension '.XBTL' to identify infected files and use email addresses belonging to the @india.com domain. One of the worrying aspects of the 'Meldonii@india.com' Ransomware is that this threat family tends to target enterprise networks and servers rather than focusing on individual users. Because of this, the 'Meldonii@india.com' Ransomware infections and variants in this family have a lot of potential for causing significant monetary losses and damage. The 'Meldonii@india.com' Ransomware attack is simple to understand. The 'Meldonii@india.com' Ransomware may be delivered attached to compromised email messages. These email messages will use social engineering techniques to trick inexperienced computer users into opening the attached file. Once the file is opened, it will change the victim's computer settings to ensure that the 'Meldonii@india.com' Ransomware runs automatically each time Windows starts up. The 'Meldonii@india.com' Ransomware then connects to its Command and Control server to receive instructions and send information about the infected computer. The 'Meldonii@india.com' Ransomware corrupted executable file is dropped into one of the following directories on the infected computer:
%AppData%
%Roaming%
%Local%
%LocalRow%
%Windows%
%System%
%System32%
%Temp%
This executable file will often be named to make it appear as a legitimate Microsoft Windows system file. When the 'Meldonii@india.com' Ransomware carries its attack, it uses a strong encryption algorithm to encrypt the following file types on the infected PC:
PNG .PSD .PSPIMAGE .TGA .THM .TIF .TIFF .YUV .AI .EPS .PS .SVG .INDD .PCT .PDF .XLR .XLS .XLSX .ACCDB .DB .DBF .MDB .PDB .SQL .APK .APP .BAT .CGI .COM .EXE .GADGET .JAR .PIF .WSF .DEM .GAM .NES .ROM .SAV CAD Files .DWG .DXF GIS Files .GPX .KML .KMZ .ASP .ASPX .CER .CFM .CSR .CSS .HTM .HTML .JS .JSP .PHP .RSS .XHTML. DOC .DOCX .LOG .MSG .ODT .PAGES .RTF .TEX .TXT .WPD .WPS .CSV .DAT .GED .KEY .KEYCHAIN .PPS .PPT .PPTX ..INI .PRF Encoded Files .HQX .MIM .UUE .7Z .CBR .DEB .GZ .PKG .RAR .RPM .SITX .TAR.GZ .ZIP .ZIPX .BIN .CUE .DMG .ISO .MDF .TOAST .VCD SDF .TAR .TAX2014 .TAX2015 .VCF .XML Audio Files .AIF .IFF .M3U .M4A .MID .MP3 .MPA .WAV .WMA Video Files .3G2 .3GP .ASF .AVI .FLV .M4V .MOV .MP4 .MPG .RM .SRT .SWF .VOB .WMV 3D .3DM .3DS .MAX .OBJ R.BMP .DDS .GIF .JPG ..CRX .PLUGIN .FNT .FON .OTF .TTF .CAB .CPL .CUR .DESKTHEMEPACK .DLL .DMP .DRV .ICNS .ICO .LNK .SYS .CFG.
The 'Meldonii@india.com' Ransomware changes the encrypted files' extensions to .XBTL, making it easy to know which files have been encrypted by this threat.
Protecting Your Computer from Threats Like the 'Meldonii@india.com' Ransomware
The best protection against encryption ransomware threats like the 'Meldonii@india.com' Ransomware is to ensure that you have offsite backups of all files. In many cases, backups are stored on the same server or network as the infected computer, making it likely that the backups will become corrupted too. Because of this, ensure that your backed up files are not connected physically to the computer. If the backups exist, then the con artists no longer have any way of threatening or demanding money from victims.
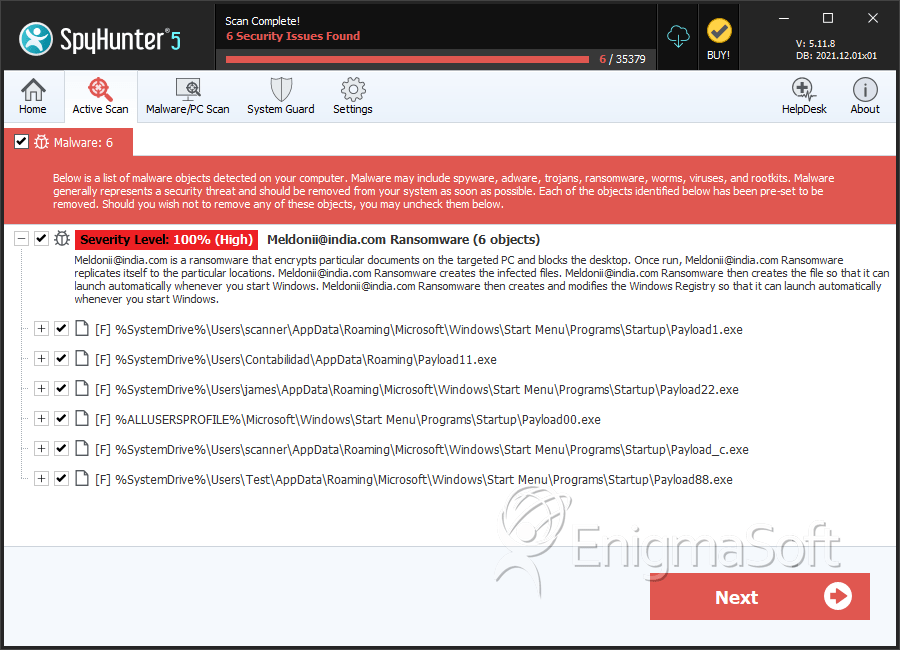
SpyHunter Detects & Remove Meldonii@india.com Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | Payload1.exe | b5bfe922d5fca45b6ad2d0d2a9dab520 | 30 |
| 2. | Payload11.exe | 19e58ac43d38237db5d803a724fe06a7 | 8 |
| 3. | Payload22.exe | f44356480e91acef8f437440928030b4 | 7 |
| 4. | Payload00.exe | 2fc8df6492276f287cdb916277fb0914 | 6 |
| 5. | Payload_c.exe | 98f0855d4021747730bec172c633a56b | 6 |
| 6. | Payload88.exe | bf7b15cb398ab411cb2e2201bfe20055 | 3 |
