Ledger - Critical Security Vulnerability Scam
Scammers continue to exploit the growing popularity of digital currencies, and the Ledger – Critical Security Vulnerability Scam is a prime example of how cybercriminals craft convincing messages to mislead users. These emails mimic urgent security alerts to create panic, prompting recipients to rush into harmful actions. It is important to stress that these messages are not associated with any legitimate companies, organizations, or service providers.
Table of Contents
A Fraudulent Email Disguised as a Security Notice
The scam begins with an email that appears to come from the reputable hardware wallet manufacturer Ledger. The message typically warns users about a supposedly critical vulnerability affecting devices running outdated firmware. To reinforce the sense of urgency, the email instructs recipients to complete a verification procedure immediately to 'protect' their crypto assets.
This verification claim is part of the deception. Although the email lists several technical-sounding checks, such as device connection validation, firmware inspection, entropy confirmation, and security protocol verification, the true purpose is to direct the user to a fraudulent website. Recipients are advised to ignore these emails entirely.
The Malicious Website and the Push for Recovery Phrases
Once victims follow the embedded link, they land on a counterfeit Ledger-related page designed to appear authentic. The site then demands that users perform an 'Entropy verification,' a fabricated procedure used to justify requesting their 12-, 18-, or 24-word recovery phrase.
Entering this phrase hands full control of a crypto wallet to the attackers. They use it to access the victim's holdings and transfer the funds to their own accounts. Because blockchain transactions are irreversible, the stolen cryptocurrency is almost always lost permanently.
Warning Signs and Tactics Used in the Scam
Cybercriminals use the authority of a well-known brand, combined with fear-based messaging, to entice victims into compromising their accounts. These emails also share traits common to phishing campaigns, including attempts to harvest sensitive information and redirect users to dangerous websites.
Common elements seen in this scam include:
- Urgent claims about device vulnerabilities and supposedly required immediate action.
- Technical terms used to appear authentic and authoritative.
- Links leading to imitation websites.
- Requests for highly sensitive data such as recovery phrases or private keys.
The Malware Risk Behind Suspicious Emails
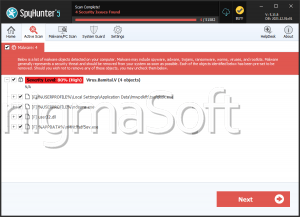
Beyond stealing recovery phrases, these fraudulent emails may also deliver malware. Criminals often attach infected files or embed malicious links designed to download harmful software. These payloads might include malicious documents, executables, scripts, compressed files, or other formats that activate once opened or when features like macros are enabled.
Links in these emails may lead to pages that automatically trigger a download or prompt the user to install malware manually. The infection occurs when recipients interact with the malicious content.
Malware delivery methods often involve:
- Attached files containing hidden malicious code.
- Links pointing to compromised or fraudulent pages.
- Social engineering designed to persuade users to open harmful content.
Staying Safe from Cryptocurrency-Related Scams
Users should remain vigilant when handling unsolicited emails, especially those involving financial accounts or digital assets. Never enter recovery phrases, private keys, or other sensitive details on unfamiliar or suspicious websites. If a message feels urgent, threatening, or out of place, treat it with skepticism.
Maintaining strong cybersecurity hygiene is essential. Keep your operating system, browsers, and applications updated. Use reliable security software to scan devices regularly. Avoid pirated programs, cracks, and key generators, as they frequently carry malware. Finally, steer clear of untrustworthy ads, pop-ups, and notification prompts that may lead to compromising situations.
Conclusion
The Ledger – Critical Security Vulnerability Scam is a deceptive phishing scheme designed to steal cryptocurrency by manipulating users into revealing their recovery phrases. By understanding how such schemes operate and maintaining cautious online habits, users significantly reduce their risk of falling victim to irreversible financial theft.