Jeff Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 3 |
| First Seen: | August 30, 2018 |
| Last Seen: | October 24, 2025 |
| OS(es) Affected: | Windows |
The Jeff Ransomware is a ransomware Trojan that is either unfinished or part of a prank. Threats like the Jeff Ransomware are designed to take the victim's computer hostage by encrypting the victims' data and then demanding a ransom payment in exchange for the decryption key needed to restore these files. However, the Jeff Ransomware in its current form seems to be designed merely to scare computer users into believing that their files were compromised.
Table of Contents
What Threats Like the Jeff Ransomware Do Usually
Malware like the Jeff Ransomware uses a strong encryption algorithm to make the victim's files inaccessible. While there are reasons to believe the Jeff Ransomware is nothing more than a prank, there are two aspects of the Jeff Ransomware that make it likely that the Jeff Ransomware is an early version of ransomware threats meant for worldwide distribution: (1) a working ransom note message and (2) a language switcher that allows the victims to switch the language of the ransom note into one of many options. Threats like the Jeff Ransomware use the AES encryption to target the user-generated files preferably, such as the following, taking them hostage until the victim pays a ransom:
.jpg, .jpeg, .raw, .tif, .gif, .png, .bmp, .3dm, .max, .accdb, .db, .dbf, .mdb, .pdb, .sql, .dwg, .dxf, .cpp, .cs, .h, .php, .asp, .rb, .java, .jar, .class, .py, .js, .aaf, .aep, .aepx, .plb, .prel, .prproj, .aet, .ppj, .psd, .indd, .indl, .indt, .indb, .inx, .idml, .pmd, .xqx, .xqx, .ai, .eps, .ps, .svg, .swf, .fla, .as3, .as, .txt, .doc, .dot, .docx, .docm, .dotx, .dotm, .docb, .rtf, .wpd, .wps, .msg, .pdf, .xls, .xlt, .xlm, .xlsx, .xlsm, .xltx, .xltm, .xlsb, .xla, .xlam, .xll, .xlw, .ppt, .pot, .pps, .pptx, .pptm, .potx, .potm, .ppam, .ppsx, .ppsm, .sldx, .sldm, .wav, .mp3, .aif, .iff, .m3u, .m4u, .mid, .mpa, .wma, .ra, .avi, .mov, .mp4, .3gp, .mpeg, .3g2, .asf, .asx, .flv, .mpg, .wmv, .vob, .m3u8, .dat, .csv, .efx, .sdf, .vcf, .xml, .ses, .qbw, .qbb, .qbm, .qbi, .qbr , .cnt, .des, .v30, .qbo, .ini, .lgb, .qwc, .qbp, .aif, .qba, .tlg, .qbx, .qby , .1pa, .qpd, .txt, .set, .iif, .nd, .rtp, .tlg, .wav, .qsm, .qss, .qst, .fx0, .fx1, .mx0, .fpx, .fxr, .fim, .ptb, .ai, .pfb, .cgn, .vsd, .cdr, .cmx, .cpt, .csl, .cur, .des, .dsf, .ds4, , .drw, .eps, .ps, .prn, .gif, .pcd, .pct, .pcx, .plt, .rif, .svg, .swf, .tga, .tiff, .psp, .ttf, .wpd, .wpg, .wi, .raw, .wmf, .txt, .cal, .cpx, .shw, .clk, .cdx, .cdt, .fpx, .fmv, .img, .gem, .xcf, .pic, .mac, .met, .pp4, .pp5, .ppf, .nap, .pat, .ps, .prn, .sct, .vsd, .wk3, .wk4, .xpm, .zip, .rar.
What the Jeff Ransomware Does in Its Current Version
The Jeff Ransomware does not have an encryption module in its current version, meaning that the victim's files will not be encrypted. The Jeff Ransomware maps the victim's drives and then delivers a program window with the title 'JeFf thE rAnSOmwArE v1.0.' The Jeff Ransomware also will change the infected computer's desktop into a picture of an Icelandic landscape (that may be a placeholder for a ransom note, which is often used to replace the victim's desktop wallpaper image). One additional feature of the Jeff Ransomware is that a disturbing music clip will play while the Jeff Ransomware delivers its ransom note, a feature that has been associated with ransomware variants based on theJigsaw family of ransomware. The Jeff Ransomware delivers the following ransom note to the victim:
'JeFf thE rAnSOmwArE v1.0 Language : [lang switch]
WHAT YOU DO TO MY COMPUTER??!??!!!
[sample text]
[RECOVER MY FILES|BUTTON] [EXIT|BUTTON]'
It is likely that the Jeff Ransomware will be released in a full version eventually. In fact, the Jeff Ransomware is almost finished since all it would need would be the implementation of an encryption module, of which there are various open source variants that criminals could use. As with most ransomware Trojans, computer users should take precautions and protect their computers with a security program and have a back up of all their files.
template:aliases]
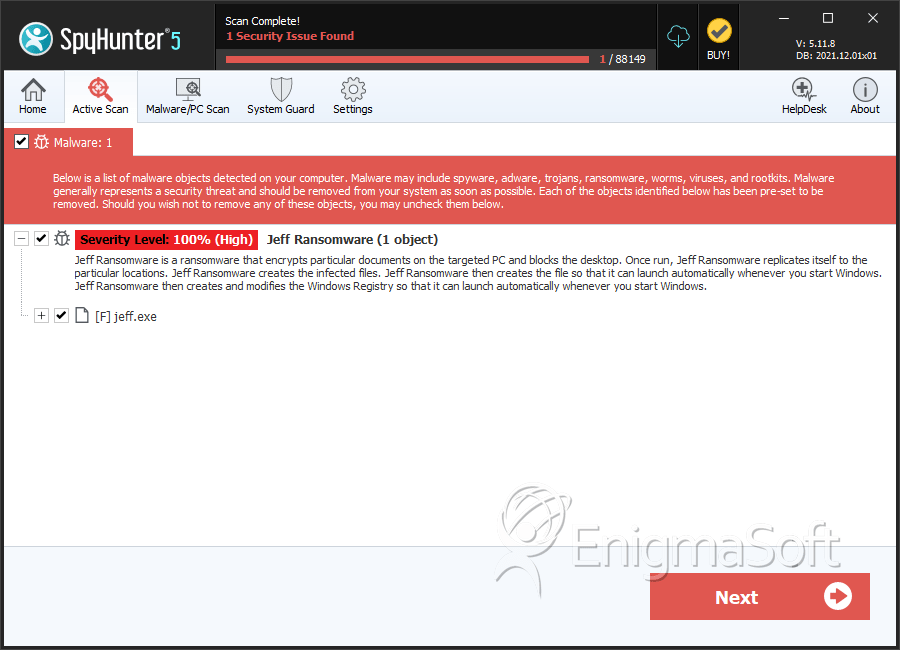
SpyHunter Detects & Remove Jeff Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | jeff.exe | 609a86e03fb8546be377b332dca753d9 | 1 |
