‘Help recover files.txt’ Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 9 |
| First Seen: | October 16, 2015 |
| Last Seen: | June 11, 2020 |
| OS(es) Affected: | Windows |
The 'Help recover files.txt' Ransomware is a ransomware infection that has been used to attack computers mainly located in Greece and the Balkans. The 'Help recover files.txt' Ransomware infection can be recognized by its text message that contains the following data:
"Hi,
What happened to your files?
All your files were protected by a strong encryption with RSA-2048
More information about the encryption keys using RSA-2048 can be found heres https://en.wikipedia.org/RSA
What does this mean?
This mean that the structure and data within your files have been irrevocably change and only we can help you to restore it.
How did this happen?
Especially for you, on our server was generated the secret key pair RSA-2048 - public and private
All your files were encrypted with the public key, which has been transferred to your computer via internet.
Decrypting of your files is only possible with the help of the private key and decrypt program which is on our server
You can buy our tool with private key that will recover all your files. It cost's 4 bitcoins and you need send it to bitcoin address 14mf7A1oCZ7bjpkqaoXCHp2VLRhuv***** . 1 bitcoin ~= 240 US $.
You can make bitcoin payment without any bitcoin software. For this you can use one of this bitcoin exchanger from this exchange list to send us bitcoins
https://www.btcgreece.com
https://btctrader.com
www.plus500.gr/Bitcoins-CFD
https://localbitcoins.com/country/GR
coinmill.com/BTC_GRD.html
btcdirect.eu
localbitcoins.com
Coincafe.com
coinrnr.com
bitquick.co
anxpro.com
bittylicious.com
Our contact mail entry122717@gmail.com . Additional contact mail entry123488@india.com (email us here if we don't answer from gmail.com).
Your own personal key: JeO9K092mm**** . Send us your own personal key after payment and we will send you decryption tool.
You can send one small file (not bigger than 1 megobyte) before payment and we will recover it. It will be proof that we have decryption tool."
The 'Help recover files.txt' Ransomware displays this message both in English and in Greek, noting that the 'Help recover files.txt' Ransomware probably originates in this country or has been specifically designed to target computer users in this part of the world. The 'Help recover files.txt' Ransomware asks a ransom that is quite elevated. While other ransomware infections tend to ask for one Bitcoin (about $250 USD), the 'Help recover files.txt' Ransomware asks for four!
How Ransomware Attacks Like the 'Help recover files.txt' Ransomware Work
Ransomware attacks such as the 'Help recover files.txt' Ransomware have increased in frequency in recent years. These kinds of attacks may be devastating since computer users may not have a way of recovering their files if they become compromised. The following are the general steps that the 'Help recover files.txt' Ransomware takes when carrying out its attack (these steps may be followed by most encryption ransomware infections similar to the 'Help recover files.txt' Ransomware):
- The 'Help recover files.txt' Ransomware may be distributed using threat delivery techniques. Typically, computer users may pick up the 'Help recover files.txt' Ransomware infection after opening a corrupted email attachment or clicking on a compromised, embedded link.
- Once the 'Help recover files.txt' Ransomware enters a computer, the 'Help recover files.txt' Ransomware searches the affected hard drive systematically for files matching a list of file extensions associated with media files or different types of documents.
- The 'Help recover files.txt' Ransomware encrypts all files it finds using RSA-2048 encryption. After encrypting a file, the 'Help recover files.txt' Ransomware drops a text file in each folder containing information on obtaining the decryption key.
Recovering from a 'Help recover files.txt' Ransomware Attack
Unfortunately, it is nearly impossible to recover files that have been encrypted by the 'Help recover files.txt' Ransomware if one does not have access to the decryption key. Because of this, the best way to protect a computer against the 'Help recover files.txt' Ransomware attacks is by prevention. PC security researchers recommend the use of a reliable, fully updated anti-malware application to prevent threats like the 'Help recover files.txt' Ransomware from entering the targeted computer in the first place. All files should be backed up in an external memory device or on the cloud. The most effective response to a 'Help recover files.txt' Ransomware attack is to wipe the affected hard drive and reinstall the files from a backup.
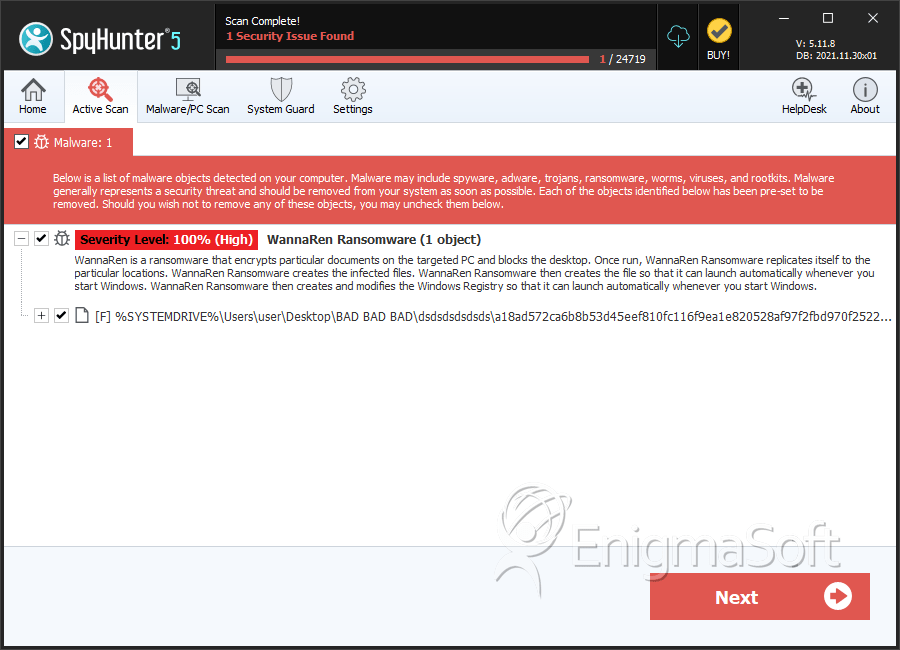
SpyHunter Detects & Remove ‘Help recover files.txt’ Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | a18ad572ca6b8b53d45eef810fc116f9ea1e820528af97f2fbd970f252296fe5 | 1de73f49db23cf5cc6e06f47767f7fda | 5 |
