HCK Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
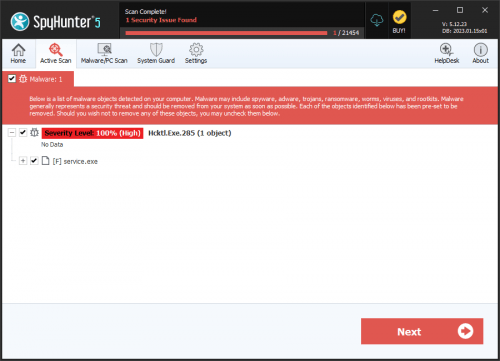
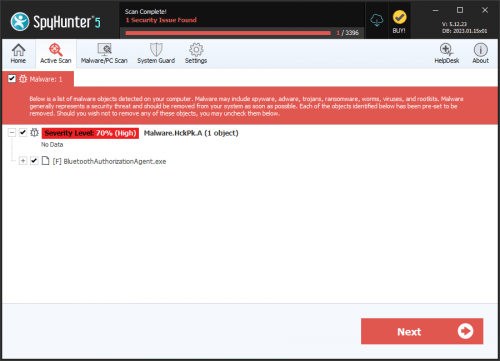
| Threat Level: | 100 % (High) |
| Infected Computers: | 2 |
| First Seen: | January 19, 2011 |
| Last Seen: | August 31, 2020 |
| OS(es) Affected: | Windows |
There are several ransomware families that have grown in 2019 and 2020 rapidly. Among the most active ransomware families is the Dharma Ransomware. Security researchers have spotted a new copy of the Dharma Ransomware, which has been dubbed the HCK Ransomware.
Propagation and Encryption
It is not acknowledged what the exact propagation method involved in the spreading of the HCK Ransomware is. There are several infection vectors that appear to be preferred by most threat actors distributing data-lockers:
- Mass spam email campaigns – Users are targeted at random and receive fraudulent emails that contain corrupted attachments or misleading links.
- Fake social media pages – Bogus posts that aim to spread threats target users via convincing social media pages and profiles.
Other popular methods include malvertising campaigns, torrent trackers, bogus software updates/downloads, etc. When the HCK Ransomware breaches your system successfully, it will begin locking the data present on it. Threats like the HCK Ransomware are known to target a wide range of filetypes including .pdf, .doc, .docx, .txt, .jpeg, .jpg, .svg, .png, .gif, .ai, .psd, .tif, .mov, .mp4, .mkv, .avi, .mpg, .mpeg, .db, .xml, .rar, .zip, .pkg, .mp3, .mpa, .wma, .mid, .midi and many others. When the targeted files get locked by the HCK Ransomware, they will have their names altered. This ransomware threat adds a '.id-<VICTIM ID>.[cavefat@tuta.io].HCK' extension to the names of the encrypted files.
The Ransom Note
Once the HCK Ransomware is done encrypting all the data that matched its criteria, it will take the next step – the dropping of the ransom note. The file containing the note written by the attackers is called ‘FILES ENCRYPTED.txt.’ There is barely any useful information in the ransom message of the attackers. In the note, they state that users should contact them via email and offer two email addresses for this purpose – ‘cavefat@tuta.io’ and ‘ripntfs@protonmail.com.’
If you fall victim to the HCK Ransomware, it is not recommended to contact the attackers or pay the ransom fee. There is no assurance that the attackers will provide the decryptor you need to recover your data, even if you give in and pay up. Make sure you remove the HCK Ransomware from your PC with the help of a reliable, up-to-date anti-malware solution.