Dorkbot
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 16,796 |
| Threat Level: | 50 % (Medium) |
| Infected Computers: | 2,319 |
| First Seen: | June 1, 2011 |
| Last Seen: | October 24, 2025 |
| OS(es) Affected: | Windows |
First detected in 2011, the Dorkbot family of Trojans and worms is associated with a vast botnet by the same name. ESG security researchers consider that all malware associated with Dorkbot poses a severe threat to a computer's integrity and should be removed immediately with the help of a reliable anti-malware program. Dorkbot uses IRC in order to relay orders to infected computers. The Dorkbot malware is often distributed using social engineering scams, including malicious social media spam messages and email spam. Variants of Dorkbot can be used to steal personal information and online banking credentials. There are many variants of malware associated with Dorkbot, with many different file names due to the many social engineering scams associated with this threat. One recent scam used to distribute Dorkbot malware involves fake Skype messages sent out by a Dorkbot worm variant. These link computer users to a backdoor Trojan which then allows criminals to install the Dorkbot worm on the victim's computer.
Most Dorkbot variants are installed through social media or instant messaging scams. These are often poorly written messages sent out on Skype, Facebook or Twitter containing a link that supposedly allows a computer user to access an image file. However, these image files will usually be ZIP or EXE files that contain executable files for either the Dorkbot worm itself or for a backdoor Trojan designed to allow criminals to install a Dorkbot variant on the victim's computer. Once installed, the Dorkbot variant will typically use a randomly generated file name and will make changes to the Windows Registry that ensure that Dorkbot is executed each time the victim starts up Windows.
Dorkbot malware can spread using removable drives. Whenever Dorkbot infects a computer, Dorkbot will copy itself to all drives detected on the victim's computer. It also creates an AutoRun file which allows the Dorkbot worm to start up automatically as soon as the drive is accessed. Dorkbot is also distributed using instant messaging and, in particular, IRC (Instant Relay Chat). Social networks such as Facebook and Vkontakte (a large social network in Russia) are also used to distribute the Dorkbot. IRC is also a big part of Dorkbot's payload since the main purpose of this malware threat is integrating the victim's computer into a botnet that receives its commands through IRC.
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| AVG | Generic30.RWE |
| Fortinet | W32/ZeroAccess.B!tr |
| AntiVir | TR/Spamlink.B |
| F-Secure | Gen:Variant.Symmi.4572 |
| Comodo | TrojWare.Win32.Kryptik.AOCS |
| Kaspersky | Trojan-Ransom.Win32.PornoAsset.azfv |
| Symantec | Trojan.Ransomlock!g28 |
| F-Prot | W32/Zbot.GR.gen!Eldorado |
| CAT-QuickHeal | TrojanRansom.PornoAsset.azfv |
| AVG | Generic30.AIAS |
| Fortinet | W32/PornoAsset.BHJW!tr |
| McAfee-GW-Edition | Artemis!76B93EEF84E1 |
| AntiVir | TR/Ransom.Blocker.bhjw |
| Comodo | TrojWare.Win32.Kryptik.AOZW |
| Kaspersky | Trojan-Ransom.Win32.PornoAsset.bhjw |
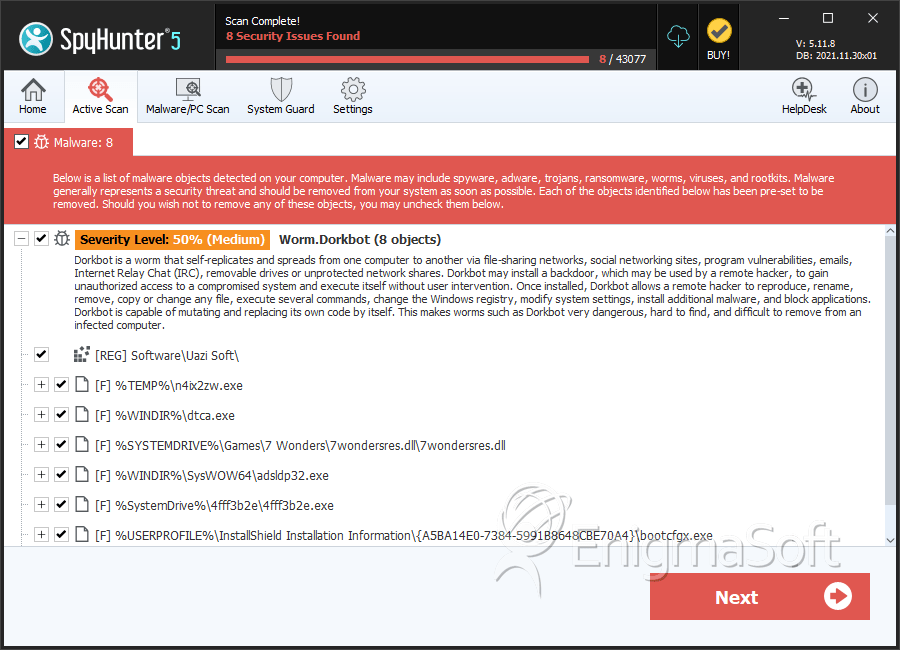
SpyHunter Detects & Remove Dorkbot
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | n4ix2zw.exe | 089d0751a27a042df2db0ca555dbec3b | 16 |
| 2. | dtca.exe | fccee40edc06bfcaf3b5174c77f80c28 | 14 |
| 3. | 4fff3b2e.exe | 9eabfe6453e2510c6c63269ab96516b3 | 8 |
| 4. | 7wondersres.dll | 9ed9fc8a0b5662be9abb011f011a1d30 | 7 |
| 5. | adsldp32.exe | e9820eb60f4561f72a16aee89aa7e4b8 | 7 |
| 6. | bootcfgx.exe | 391610bc234dc8ed034db97552b3360c | 5 |
| 7. | nmtd.exe | 30761af5190c4952438535a40d9d879f | 4 |
| 8. | Leugur.exe | f172d879a389210d50f03362ebf6c67b | 2 |
| 9. | msado320.tlb | ea09e6441858e978424a3532ea646326 | 2 |
| 10. | 4C24.exe | c3b779e35e655ba094c2428c1f27e13c | 2 |
| 11. | 11.exe | dc5804aee172e6e01d435985320d3a42 | 2 |
| 12. | 44.exe | 9b140329f1430b9d6a28eef7a3849df0 | 2 |
| 13. | A738.exe | 834857e8f61b50b1f411a5c2f7788208 | 2 |
| 14. | lsass.exe | 7499c11cf0f5f8e39204ce0243b450db | 1 |
| 15. | winlog.exe | e988660ac3a01115e42077644d935466 | 1 |
| 16. | mswdat1032.exe | be3a6ee5b1f3e6aff1a02905752a2a2c | 1 |
| 17. | Wbnmni.exe | daff13b10ad87d9f578555b641758fa1 | 1 |
| 18. | Ucpkpe.exe | b12d51d5577de2a62a7f6d0c1f5c3cdd | 1 |
| 19. | 8673.exe | 315184d67a7a18d6b02b8d4a1b9f5cfa | 1 |
| 20. | D661.exe | 1d43d43d728f01159931f0cf89dfa94d | 1 |
| 21. | 7369.exe | 76b93eef84e1774c1104ac5418acc1e1 | 1 |
| 22. | 120D.exe | aef539acf35cab6e8d2a3cff06a42cc7 | 1 |
| 23. | file.exe | 42c7c3bbf232fbb86dca01c6f75d2cf7 | 0 |
