Destroy Ransomware
Users need to protect their devices from sophisticated malware threats. Among these threats, ransomware has emerged as one of the most dangerous, targeting files, networks, and sensitive data. One such newly discovered ransomware variant, known as the Destroy Ransomware, is causing significant concern for both individuals and businesses. Its ability to encrypt files and exfiltrate data makes it a formidable cyber weapon.
Table of Contents
What Is the Destroy Ransomware?
The Destroy Ransomware is part of a notorious ransomware family derived from the MedusaLocker strain. Once executed on a target device, it encrypts the files, appending a unique extension to each one. For instance, a file initially named '1.png' will appear as '1.png.destry30' after the attack. The number in the extension may differ depending on the specific variant of the ransomware. The attackers not only lock the victim's files but also claim to have stolen confidential data, which they threaten to leak or sell unless a ransom is paid.
After encryption is complete, the Destroy Ransomware delivers a ransom note titled 'How_to_back_files.html.' This note states that the victim's network has been compromised, critical files have been encoded, and sensitive data has been harvested. The ransom demand is left ambiguous, with a warning to avoid using third-party decryption tools or modifying the locked files, as it could lead to permanent data loss. The attackers offer a limited "test decryption" of up to three files to build trust with the victim, but compliance with the ransom demand is strongly discouraged by cybersecurity experts.
Ransom Demands and Risks
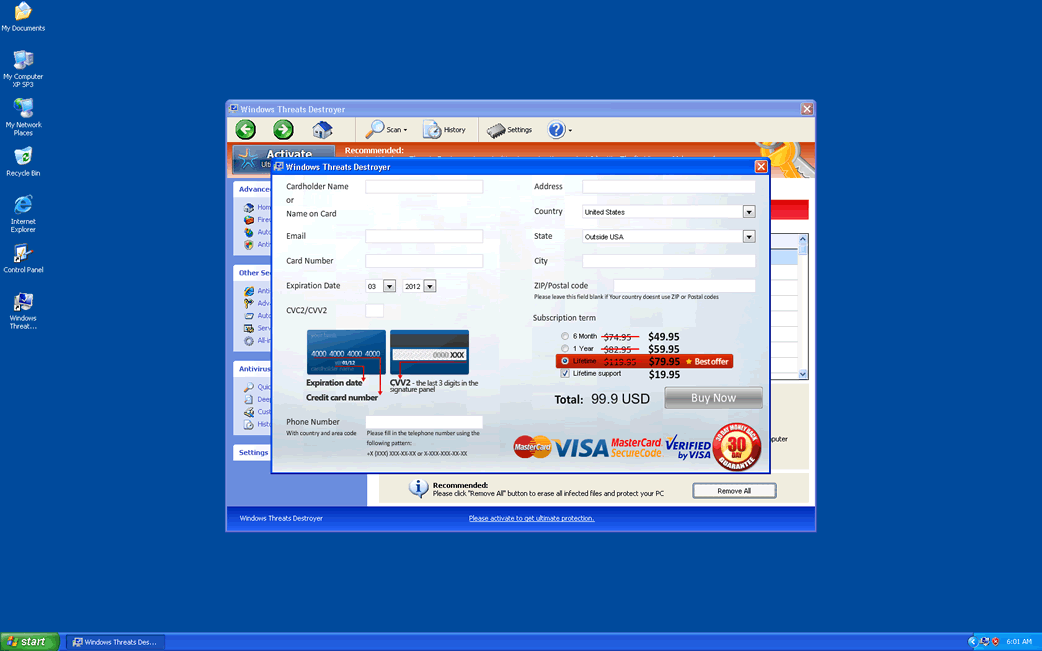
Like many ransomware variants, the Destroy Ransomware aims to prompt victims to pay a ransom, typically in cryptocurrency, to regain access to their encrypted files. However, the risks associated with complying are considerable. Paying the ransom does not guarantee the return of your data—cybercriminals often withhold the decryption key even after receiving payment. In many cases, victims are left without any means of recovering their files, and their stolen data may still be sold or leaked.
Beyond the financial impact, paying the ransom supports criminal enterprises. By transferring money to attackers, victims inadvertently fund the development of more advanced ransomware variants, which perpetuates the cycle of cybercrime.
The Spread of the Destroy Ransomware: How Does It Infect?
The Destroy Ransomware, like other forms of malicious software, typically spreads through phishing and social engineering techniques. Attackers use deceptive emails or messages to trick victims into downloading fraudulent files disguised as legitimate content. These files can take various forms, including ZIP archives, executable files, Office documents, PDFs, and JavaScript files.
In some cases, merely opening the infected file is enough to trigger the ransomware infection. Drive-by downloads, malicious attachments, and links in spam messages are also common methods of delivering ransomware. Additionally, the Destroy Ransomware may be distributed through untrustworthy download sources, such as third-party websites, peer-to-peer networks, fake software updates, and illegal software cracks. Some versions of ransomware can also spread across local networks or through infected removable storage devices like USB drives.
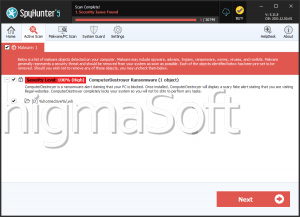
Removing the Destroy Ransomware: What You Need to Know
If your device becomes infected with the Destroy Ransomware, removal of the malware is essential to prevent further encryption of files. However, it is important to note that removing the ransomware does not restore already encrypted data. This is why maintaining regular backups and implementing strong security practices are critical to minimize damage in the event of an attack.
Despite the urgent need to remove the Destroy Ransomware, victims should never attempt to decrypt files without professional assistance or use third-party decryption tools unless specifically advised by cybersecurity experts. These attempts can lead to permanent file loss.
Best Security Practices to Protect Against the Destroy Ransomware
To protect against ransomware attacks like Destroy, users must adopt a multi-layered security approach. Here are some of the best security practices to bolster your defense:
- Regular Backups of Critical Data: The most effective shelter against ransomware is to maintain regular backups of your important files. Backups should be stored in multiple locations, such as offline external storage or cloud services. Ensure that the backup is disconnected from the network after each session, as ransomware can infect connected devices.
- Use Comprehensive Security Software: Install reputable anti-ransomware software to detect and block threats. Keep your security tools updated to ensure they can recognize the latest ransomware variants. Advanced security solutions offer features like behavior-based detection, which can identify suspicious activity in real time.
- Patch and Update Software Regularly: Ransomware often exploits vulnerabilities in out-of-date programs to gain access to systems. Be assured that all your software, including your operating system, Web browsers, and security tools, are up to date according to the newest security patches.
- Be circumspect when dealing with Phishing Emails: Phishing is a common entry point for ransomware. Be cautious of unsolicited messages or emails, especially those that include attachments or links. Avoid accessing links or downloading attachments from unknown or suspicious sources. Double-check the sender's email address for discrepancies, and when in doubt, verify with the source directly.
- Disable Unnecessary Services: Disable services like Remote Desktop Protocol (RDP) if they are not essential. RDP is often targeted by attackers to gain unauthorized access to systems. If RDP must be used, ensure it is protected with strong passwords and multi-factor authentication.
- Implement Strong Passwords and MFA: Ensure all user accounts have strong, unique passwords, and enable Multi-Aactor Authentication (MFA) wherever possible. This provides an additional layer of protection by demanding more than just a password to access sensitive accounts.
- Network Segmentation: If you manage a business or organizational network, consider segmentation to limit the spread of ransomware. By dissecting the network into smaller segments, you can isolate infected devices and prevent ransomware from moving laterally across the network.
- Educate and Train Users: User education is a key defense against ransomware. Provide training on recognizing phishing attempts, avoiding suspicious downloads, and practicing safe browsing habits. Informed PC users are less likely to fall victim to social engineering tactics.
In Conclusion, Prevention Is the Best Defense
The Destroy Ransomware, much like other strains in the MedusaLocker family, presents a serious threat to users and organizations. While the consequences of an attack can be devastating, prevention remains the most effective defense. By adopting strong security practices, maintaining regular backups, and staying vigilant, users can significantly reduce their risk of falling victim to ransomware.
Remember, ransomware attacks can happen to anyone—so take proactive measures to secure your data and devices. The cost of prevention is always less than the price of recovery.
Victims of the Destroy Ransomware are left with the following ransom note:
'YOUR PERSONAL ID:
/!\ YOUR COMPANY NETWORK HAS BEEN PENETRATED /!\
All your important files have been encrypted!Your files are safe! Only modified. (RSA+AES)
ANY ATTEMPT TO RESTORE YOUR FILES WITH THIRD-PARTY SOFTWARE
WILL PERMANENTLY CORRUPT IT.
DO NOT MODIFY ENCRYPTED FILES.
DO NOT RENAME ENCRYPTED FILES.No software available on internet can help you. We are the only ones able to
solve your problem.We gathered highly confidential/personal data. These data are currently stored on
a private server. This server will be immediately destroyed after your payment.
If you decide to not pay, we will release your data to public or re-seller.
So you can expect your data to be publicly available in the near future..We only seek money and our goal is not to damage your reputation or prevent
your business from running.You will can send us 2-3 non-important files and we will decrypt it for free
to prove we are able to give your files back.Contact us for price and get decryption software.
email:
ithelp01@securitymy.name
ithelp01@yousheltered.comTo contact us, create a new free email account on the site: protonmail.com
IF YOU DON'T CONTACT US WITHIN 72 HOURS, PRICE WILL BE HIGHER.Tor-chat to always be in touch:
qd7pcafncosqfqu3ha6fcx4h6sr7tzwagzpcdcnytiw3b6varaeqv'
Destroy Ransomware Video
Tip: Turn your sound ON and watch the video in Full Screen mode.