Dangerous Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
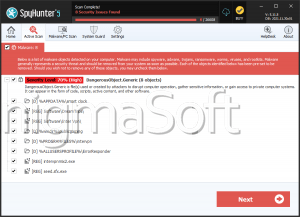
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 16,650 |
| Threat Level: | 50 % (Medium) |
| Infected Computers: | 64 |
| First Seen: | March 14, 2017 |
| Last Seen: | January 5, 2025 |
| OS(es) Affected: | Windows |
The Dangerous Ransomware is a ransomware Trojan that encrypts the victims' files as part of its attack. The Dangerous Ransomware uses a similar approach as countless encryption ransomware Trojans, which involves encrypting the victim's files to take them hostage so that it can demand the payment of a ransom in exchange for the decryption key. These threats have increased in number and popularity since 2015 and pose a significant threat to the computer users' data.
Table of Contents
Looks Like the Dangerous Ransomware Belongs to a Small Family
The Dangerous Ransomware was first observed in Russia on March 9, 2017. The Dangerous Ransomware is being distributed through the use of corrupted spam email attachments, which abuse macros to execute compromised code on victims' computer. This is a distribution tactic that is quite common, and that has been linked to various encryption ransomware Trojans. These corrupted documents, often Microsoft Word documents or PDF files, will drop the executable file 'DANGEROUS_RANSOMW.exe,' which carries out the Dangerous Ransomware attack on the victim's computer. PC security researchers do not suspect that the Dangerous Ransomware is part of a larger family of ransomware. Rather, it seems that con artists have taken an open source ransomware engine and made some modifications to it to convert it into the Dangerous Ransomware Trojan. However, despite its unsophisticated origins, the Dangerous Ransomware still carries out a highly effective ransomware attack capable of making the victims' files inaccessible completely.
How the Dangerous Ransomware Attack Works
Encryption ransomware Trojans can carry out a very effective attack, and it is basic to be protected against these threats. The best protection against threats like the Dangerous Ransomware is to have backup copies of all files. The Dangerous Ransomware uses a combination of the RSA and AES encryption to make the victims' data inaccessible completely. The Dangerous Ransomware will encrypt the files located on all local hard drives, as well as on network shared drives and external memory devices connected to the infected computer. If the file synchronization is enabled, it is even possible that the Dangerous Ransomware will manage to affect files stored on cloud storage services linked to the infected computer. The Dangerous Ransomware will target a wide variety of files in its attack, using the AES-256 and RSA-2048 encryption algorithms (resulting in data that, when encrypted, is impossible to access without the decryption key). The Dangerous Ransomware uses 'myscrypt.vbs' to display a ransom note on the victims' computer. This appears in a window that contains the text 'YOUR PERSONAL FILES HAS BEEN ENCRYPTED' and then opens the file 'troll.txt' using the default application. This ransom note is quite short and reads as follows:
'DANGEROUS_RANSOM
Hacked. Please contact hackermail@someting.com'
Dealing with a Dangerous Ransomware Infection
The Dangerous Ransomware's ransom amount is related to the amount of data encrypted by the Dangerous Ransomware. The con artists instruct victims to contact them via email to receive payment instructions. This is a tactic observed in other ransomware attacks. The con artists demand a ransom to be paid using TOR, often ranging between $400 and $1300 USD in BitCoins. PC security researchers advise computer users to refrain from paying the Dangerous Ransomware ransom. In many cases, these people will not deliver the decryption key and, regardless of whether they decrypt the files or not, paying the Dangerous Ransomware ransom allows them to continue creating and financing these threats. Instead, PC security researchers strongly advise computer users to take preventive measures. Having file backups on an external memory device or the cloud allows quick recovery. Simple remove the Dangerous Ransomware threat itself with the help of a reliable security program and then replace the files affected by the Dangerous Ransomware with backup copies. Handling email messages and attachments with caution and making sure that all content is scanned with a reliable anti-malware scanner that is fully up-to-date also can prevent the Dangerous Ransomware.
URLs
Dangerous Ransomware may call the following URLs:
| ibrowsersearch.com |