CommonMethod
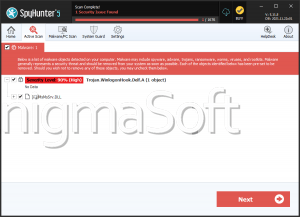
Mac users must remain cautious when downloading and installing software, as intrusive applications often disguise themselves as practical tools. These programs, classified as Potentially Unwanted Programs (PUPs), may exhibit intrusive behavior, including excessive advertising, data tracking, and system modifications that disrupt user experience. One such intrusive application recently identified is CommonMethod, an adware-type program associated with the AdLoad family.
Table of Contents
What is CommonMethod?
CommonMethod is a form of adware designed to generate revenue by displaying intrusive advertisements on infected devices. Users may notice pop-ups, banners, in-text ads, and even full-screen overlays disrupting their browsing sessions. While some advertisements may appear harmless, many promote unreliable websites, deceptive software, and scams. Some may even trigger downloads or installations when interacted with, further exposing users to security risks.
Beyond its advertising function, CommonMethod may also engage in data collection. This could include browsing history, search queries, IP addresses, and even login credentials or financial details if stored in the browser. Such data might be monetized by being shared with third parties, leading to privacy risks and potential financial harm.
Why CommonMethod may Go Unnoticed
Adware like CommonMethod often masquerades as a legitimate application, tricking users into believing it provides valuable functionalities. In many cases, PUPs claim to optimize system performance, enhance security, or improve browsing speed. However, their actual purpose is often far from what is advertised. Even when they appear to work as described, their primary function remains to serve advertisements and collect user data.
Users may not immediately recognize the presence of adware on their device, as it could operate in the background. While some symptoms include frequent pop-ups, browser redirects, or sluggish performance, others may only become apparent when users notice unauthorized changes in their browsing experience or find unfamiliar software installed.
How PUPs Like CommonMethod Infiltrate Devices
PUPs rarely rely on direct downloads from users. Instead, they employ various deceptive distribution techniques to infiltrate devices. One common method is software bundling, where adware is packaged alongside legitimate applications. Users who rush through installation processes—especially when using default or 'Quick' installation settings—may unknowingly permit additional programs to be installed.
Fraudulent advertising is another tactic. Rogue advertisements, pop-ups, and deceptive banners may trick users into downloading intrusive software. Clicking on these ads could lead to forced installations, redirecting users to misleading pages that urge them to install unnecessary applications under the guise of system updates or security tools.
Fraud-related websites also play a role in spreading PUPs. Many users land on these sites through redirects caused by intrusive ads, mistyped URLs, or browser notifications pushed by previously installed adware. These fraudulent pages may prompt users to install 'required' updates or click on misleading download links, further facilitating the spread of unwanted software.
Mac users should remain vigilant against intrusive applications like CommonMethod. While PUPs may appear legitimate, their true purpose often revolves around advertising revenue and data collection. Avoiding questionable download sources, carefully reviewing installation settings, and being skeptical of unsolicited pop-ups are crucial steps in preventing unwanted programs from infiltrating a system. By keeping up-to-date and practicing safe browsing habits, users can shield their devices and personal information from intrusive software.