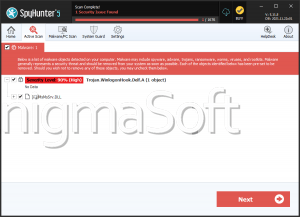
Cloak Ransomware
The ever-evolving landscape of cybersecurity threats demands vigilance from users and organizations alike. Ransomware remains one of the most destructive forms of digital extortion, with the Cloak Ransomware emerging as a particularly troubling example. Understanding its attack methods, potential consequences, and best security practices is essential for minimizing risk and preventing data loss.
Table of Contents
The Cloak Ransomware: A Silent Digital Threat
The Cloak ransomware is designed to encrypt files on an infected system, rendering them inaccessible until a ransom is paid. Once deployed, this threatening program appends a '.crYpt' extension to encrypted files, altering their names. For instance, a file originally named 'document.pdf' would appear as 'document.pdf.crYpt,' signaling that it is no longer usable.
After encryption, Cloak leaves behind a ransom note titled 'readme_for_unlock.txt.' In this message, the attackers assert that the only way to recover affected files is to purchase decryption tools from them using Bitcoin. While the specific ransom amount is undisclosed, the note discourages victims from seeking assistance from law enforcement or cybersecurity professionals, threatening permanent data loss if they do so.
A particularly concerning aspect of the Cloak Ransomware is its connection to a data-leaking website, suggesting that collected data may be exposed online if the victim does not comply with the ransom demands. However, there's no guarantee that the ransom payment will result in file recovery, as cybercriminals are notorious for failing to provide the promised decryption tools even after payment is made.
How the Cloak Ransomware Spreads
Cloak, like many ransomware threats, relies on deceptive distribution techniques to infiltrate systems. Attackers often employ phishing campaigns and social engineering methods to trick users into executing malicious files. These files may be embedded in email attachments, disguised as legitimate documents, or delivered via fraudulent links.
Other standard infection methods include:
- Trojan-based delivery – Malware hidden within seemingly legitimate software that executes once installed.
- Malvertising and drive-by downloads – Malicious advertisements or compromised websites that silently trigger malware downloads.
- Fake software updates – Fraudulent prompts urging users to download and install updates for widely used applications.
- Pirated software and cracking tools – Unauthorized software activators often contain hidden ransomware payloads.
- Removable media and network propagation – Some ransomware strains spread through local networks or external drives, compromising multiple connected devices.
Even opening a single compromised file can be enough to launch the infection chain, emphasizing the importance of cautious online behavior.
The Devastating Impact of a Ransomware Attack
The consequences of a Cloak Ransomware attack extend far beyond file encryption. Victims may experience:
- Data loss – Without a viable decryption method, personal and professional files could be permanently inaccessible.
- Financial damages—While discouraged, Paying the ransom results in monetary loss, and there is no guarantee of data restoration.
- Operational disruption – Businesses, institutions, and individuals may face downtime, affecting productivity and workflow.
- Privacy risks – Confidential information could be leaked or sold on illicit marketplaces if linked to data theft.
For these reasons, prioritizing preventive security measures is far more efficacious than dealing with the aftermath of an attack.
Best Security Practices to Prevent Ransomware Infections
Protecting against threats like the Cloak Ransomware requires a multi-layered security approach. Implementing the practices described below can significantly reduce the risk of infection:
- Exercise caution with emails and links – Avoid opening unexpected email attachments or clicking on unfamiliar links, even if they appear legitimate. Cybercriminals often impersonate trusted organizations to trick users.
- Verify downloads and sources – Stick to official websites and trusted vendors when downloading software. Avoid Peer-to-Peer sharing platforms and unauthorized freeware sources.
- Enable automatic software updates – Keeping operating systems, applications, and security tools up to date helps patch vulnerabilities that attackers could exploit.
- Use strong and unique passwords – Secure accounts with intricate passwords and enable multi-factor authentication (MFA) whenever possible to prevent unauthorized access.
- Regularly back up important data – Maintain offline or cloud-based backups of critical data. Contingent upon a ransomware attack, backups can facilitate recovery without paying the ransom.
- Restrict administrative privileges – Limit user permissions to prevent unauthorized installations and system modifications. Running a device with standard user rights reduces potential attack surfaces.
- Disconnect infected devices immediately – If ransomware is detected, disconnect affected devices from networks and external storage to contain the spread.
Final Thoughts
The Cloak Ransomware is a stark reminder of how cybercriminals continue to refine their tactics to exploit unsuspecting users. While no security strategy guarantees absolute immunity, adopting dynamic cybersecurity measures can help mitigate risks and safeguard digital assets. Users and organizations must remain vigilant, stay informed about emerging threats, and implement strong defensive measures to prevent falling victim to ransomware attacks.