ChinaYunLong Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 16 |
| First Seen: | July 20, 2017 |
| Last Seen: | July 23, 2019 |
| OS(es) Affected: | Windows |
PC security analysts have observed countless ransomware Trojans in the wild in the last few years. Along with ransomware Trojans, such as Petya or WannaCry, PC security analysts have also observed countless ransomware Trojans that simply don't work, are half-finished or poorly designed. The ChinaYunLong Ransomware belongs to this second category. Although the ChinaYunLong Ransomware is capable of carrying out an encryption ransomware attack, there are issues with the ChinaYunLong Ransomware's ransom demand that prevent it from carrying out an effective ransomware attack. It is likely that a fixed version of the ChinaYunLong Ransomware will be released to carry out these attacks.
Table of Contents
Some Details about the ChinaYunLong Ransomware Attack
Ransomware Trojans like the ChinaYunLong Ransomware have a simple attack. They will first encrypt the victim's files with a strong encryption algorithm. After encrypting the victim's data, these Trojans will then demand a ransom payment from the victim. They may do this by displaying a pop-up message, a ransom note of some sort, or notifying the victim of the attack in some other way. Although the ChinaYunLong Ransomware is capable of performing the first part of the attack by encrypting the victim's files with a strong encryption algorithm, the ChinaYunLong Ransomware fails when it comes to demanding a ransom payment from the victim.
Pay the Ransom Demanded by the ChinaYunLong Ransomware is not Recommended
PC security analysts suspect that the programmers responsible for the ChinaYunLong Ransomware based in China did not use the correct character set or text encoding in their ransom notification message. Because of this, the ransom message associated with the ChinaYunLong Ransomware is not readable, and the victim is left stranded with no way of contacting the people responsible for the ChinaYunLong Ransomware attack. The ChinaYunLong Ransomware is capable of encrypting the victim's data, and this ransomware Trojan is being delivered through spam email campaigns to unsuspecting computer users currently.
In its attack, the ChinaYunLong Ransomware will encrypt the victim's data. The ChinaYunLong Ransomware will add the file extension '.yl' to the end of each affected file's name. Using the AES 256 encryption, the ChinaYunLong Ransomware will target the user-generated files, ranging from media and image files to work-related files such as databases and Microsoft Office files. Unfortunately, since the ChinaYunLong Ransomware uses a strong encryption method in its attack, there may be no method to decrypt files that have been encrypted in the ChinaYunLong Ransomware attack. A decryption key is necessary, and the people responsible for the ChinaYunLong Ransomware attack hold this key until the victim pays a ransom. However, since no means for paying the ransom are provided to the victim of the attack, there is simply no way to contact the ChinaYunLong Ransomware's operators and pay the ransom.
Dealing with a ChinaYunLong Ransomware Infection
In its ongoing state, there is no way for computer users to pay a ransom, which may be problematic for the ChinaYunLong Ransomware's operators, who may have gone to great lengths to develop and distribute the ChinaYunLong Ransomware. The ChinaYunLong Ransomware, in the place of a ransom note, displays a pop-up window with two sentences that are barely recognizable. The ChinaYunLong Ransomware also will include a cartoon version of the well-known Anonymous logo in its 'ransom note.' However, there is no link between the ChinaYunLong Ransomware and Anonymous. The use of this logo has been observed in various other ransomware Trojans and seems to be common among con artists and threat developers. Since the ChinaYunLong Ransomware uses a strong encryption algorithm to make the victim's files inaccessible, the best protection against the ChinaYunLong Ransomware is the use of file backups to recover the affected files. The ChinaYunLong Ransomware itself can be removed from an infected computer with the help of a reliable, fully updated anti-malware application. Since the ChinaYunLong Ransomware also is being delivered using spam email messages, learning to spot these tactics and handle spam email attachments carefully is an essential part of protecting your data from threats like the ChinaYunLong Ransomware.
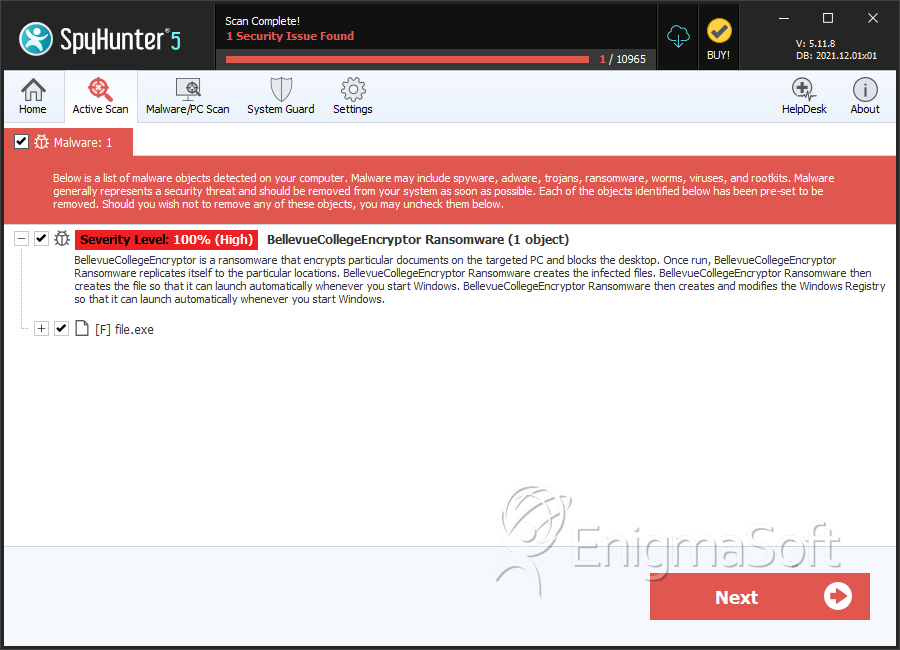
SpyHunter Detects & Remove ChinaYunLong Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | a11828339f07c41bdf234317c6418b7f | 9 |

