ChickenKiller Ransomware
Protecting personal and business systems from malware is essential, especially as modern threats grow more sophisticated and destructive. One of the most disruptive families of malicious software is ransomware, which prevents access to vital information and pressures victims into paying criminals for the possibility, never the guarantee, of restoring their data. ChickenKiller Ransomware exemplifies how quickly a single infection can lead to severe data loss, system downtime, and long-term damage.
Table of Contents
A Ruthless File-Locker: What ChickenKiller Does
ChickenKiller is a ransomware strain focused on encrypting files and leveraging the victim's desperation for profit. Once it infiltrates a system, it systematically scrambles user data and appends a .locked extension to every affected file. Images, documents, archives, and other important items suddenly become unusable and their names change from '1.png' to '1.png.locked,' '2.pdf' to '2.pdf.locked,' and so on.
After the encryption process completes, the threat drops a text document titled 'RECOVERY_INSTRUCTIONS.txt,' which serves as the attacker's ransom message. Victims are informed that their data is inaccessible without paying for the promised decryption tool. The note warns against deleting files, attempting manual decryption, modifying data, or even restarting the device, claiming these actions could make recovery impossible.
The Ransom Dilemma: Why Paying Is a Serious Risk
While attackers insist that purchasing their tool is the only path to recovery, there is no guarantee they will honor their promises. Many ransomware operators take the money and disappear, leaving victims without a working decryption key. Additionally, paying funds the continued development of criminal operations.
Even if ChickenKiller is removed from the system, already-encrypted files remain locked. The only reliable recovery method is restoring data from a clean, pre-infection backup.
How ChickenKiller Spreads
Ransomware operators use a wide array of delivery mechanisms, often relying on deception to push victims into triggering the infection themselves. Common distribution channels include phishing emails, fake downloads, cracked software tools, malicious ads, and compromised websites. Some variants spread through trojans or quietly install in the background via stealthy downloads.
In certain environments, threats may even move laterally across local networks or jump between devices via removable media such as external drives or USB sticks.
Strengthening Defenses: Security Practices That Matter
Building resilience against threats like ChickenKiller requires a combination of safe habits, strong system hygiene, and layered security tools. The following measures significantly increase protection and reduce the likelihood of a damaging infection:
- Maintain dependable, isolated backups stored on multiple mediums, including offline drives and secure remote services.
- Ensure all software, especially the operating system and security applications, is consistently updated to close exploitable gaps.
Additional Defensive Steps
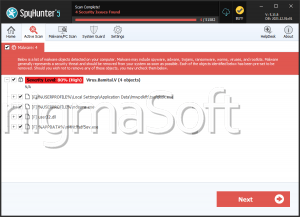
- Use reputable security tools capable of detecting ransomware behavior.
- Avoid downloading software from unverified sources or using pirated content.
- Treat unexpected attachments, links, or urgent-sounding messages with suspicion.
- Disable macros in documents unless absolutely necessary.
- Restrict administrative privileges when possible to limit the impact of malicious activity.
- Monitor networks and devices for unusual behavior, especially unexplained file changes or system performance drops.
Final Thoughts
ChickenKiller Ransomware highlights how quickly a system can fall victim to data extortion. Although removal stops further encryption, it does not reverse the damage already done. Maintaining multiple safe backups, adopting strong cybersecurity habits, and avoiding risky online actions remain the most effective strategies for staying protected.