Charmant Ransomware
File-encryption Trojans continue to be a major problem because they are among the most profitable hacking tools found in the arsenal of cybercriminals. Often, ransomware authors make thousands of dollars of profit from releasing their threat in the wild, and it does not come as something new that more and more cybercriminals are experimenting in this field. One of the recent threats to be identified by cybersecurity experts is the Charmant Ransomware – a file-locker based on the GarrantyDecrypt Ransomware family.
Unfortunately, recovering from this ransomware attack can be a very challenging task because there is no free decryption tool available. This means that users might need to resort to using alternative data recovery tools whose chances of success may often be very slim.
The Charmant Ransomware's attack will leave the victim with a large number of encrypted files whose file names will be changed to include the '.charmant' extension. Of course, the attackers need to tell their victim what to do, and this is why the ransomware will create the text file '#RECOVERY#.txt' and place it on the user's desktop. This file tells the victim to message chartmant@firemail.cc for further details or contact the Jabber account charmant@jabb.im if their email message does not get a response.
The attackers do not specify the ransom fee, but you can rest assured that the authors of the Charmant Ransomware will not agree to help unless they receive at least a few hundred dollars. We advise you not to try to purchase a decryptor from the attackers since they may end up taking your money and ceasing all contact.
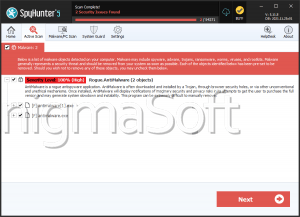
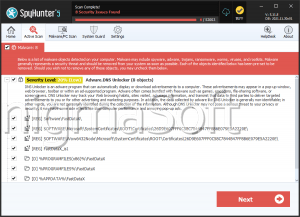
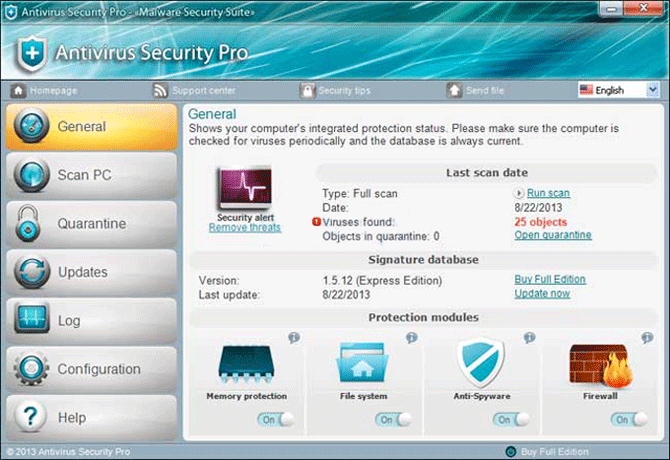
The best thing to do if your computer security has been compromised by the Charmant Ransomware is to run an anti-virus tool that disposes of the threatening program, and then look into the recommended file recovery options for victims of ransomware.