Cerber2 Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 10,199 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 71,962 |
| First Seen: | March 4, 2016 |
| Last Seen: | November 17, 2025 |
| OS(es) Affected: | Windows |
The Cerber2 Ransomware is the second version of the Cerber Ransomware, an infamous ransomware Trojan responsible for numerous attacks on computers. While files encrypted by the Cerber Ransomware were identified by the '.CERBER' extension, the Cerber2 Ransomware appends the extension '.the Cerber2' to the files it encrypts. There are also various changes to the Cerber2 Ransomware's programming and mode of attack that make it particularly more threatening than its previous version.
Table of Contents
The Cerber2 Ransomware may be the First Version of Other Variants
The Cerber2 Ransomware uses a typical encryption ransomware Trojan approach to attacking its victims, encrypting the victims' files and then demanding the payment of a ransom. PC security analysts have associated the Cerber2 Ransomware with a fake icon for a children's computer game known as Anka. While this may be a characteristic particular to one variant of the Cerber2 Ransomware, it is likely that various other variants that use different icons or stop using this particular deception will appear. During its attack, the Cerber2 Ransomware changes the victim's Desktop image into a ransom note. This ransom note, which resembles a pixelated screen, warns the victim that 'Your documents, photos, databases, and other important files have been encrypted!'
The Differences Between the Cerber2 Ransomware and Its Previous Version
There are several particular characteristics that make the Cerber2 Ransomware more threatening than its predecessor. In particular, the Cerber2 Ransomware's developers have removed a vulnerability that had allowed malware researchers to decrypt the files after the Cerber2 Ransomware carried out its encryption attack. The Cerber2 Ransomware also is packed differently and obfuscated in a different way to make it difficult for security software to detect the attack and PC security analysts study how the Cerber2 Ransomware works. The Cerber2 Ransomware now uses CryptGenRandom, a Microsoft API, to generate the encryption. The Cerber2 Ransomware now also generates a 32-byte key instead of a 16-byte key, as in its predecessor, making the previously developed decryption utility useless against the Cerber2 Ransomware.
Analyzing the Cerber2 Ransomware
PC security analysts have studied the Cerber2 Ransomware's configuration files, making it apparent that the Cerber2 Ransomware is designed to avoid sandbox environments by using a variety of methods. The Cerber2 Ransomware is designed to target the following file types:
1cd, .3dm, .3ds, .3fr, .3g2, .3gp, .3pr, .7z, .7zip, .aac, .ab4, .abd, .acc, .accdb, .accde, .accdr, .accdt, .ach, .acr, .act, .adb, .adp, .ads, .agdl, .ai, .aiff, .ait, .al, .aoi, .apj, .apk, .arw, .ascx, .asf, .asm, .asp, .aspx, .asset, .asx, .atb, .avi, .awg, .back, .backup, .backupdb, .bak, .bank, .bay, .bdb, .bgt, .bik, .bin, .bkp, .blend, .bmp, .bpw, .bsa, .c, .cash, .cdb, .cdf, .cdr, .cdr3, .cdr4, .cdr5, .cdr6, .cdrw, .cdx, .ce1, .ce2, .cer, .cfg, .cfn, .cgm, .cib, .class, .cls, .cmt, .config, .contact, .cpi, .cpp, .cr2, .craw, .crt, .crw, .cry, .cs, .csh, .csl, .css, .csv, .d3dbsp, .dac, .das, .dat, .db, .db_journal, .db3, .dbf, .dbx, .dc2, .dcr, .dcs, .ddd, .ddoc, .ddrw, .dds, .def, .der, .des, .design, .dgc, .dgn, .dit, .djvu, .dng, .doc, .docm, .docx, .dot, .dotm, .dotx, .drf, .drw, .dtd, .dwg, .dxb, .dxf, .dxg, .edb, .eml, .eps, .erbsql, .erf, .exf, .fdb, .ffd, .fff, .fh, .fhd, .fla, .flac, .flb, .flf, .flv, .flvv, .forge, .fpx, .fxg, .gbr, .gho, .gif, .gray, .grey, .groups, .gry, .h, .hbk, .hdd, .hpp, .html, .ibank, .ibd, .ibz, .idx, .iif, .iiq, .incpas, .indd, .info, .info_, .ini, .iwi, .jar, .java, .jnt, .jpe, .jpeg, .jpg, .js, .json, .k2p, .kc2, .kdbx, .kdc, .key, .kpdx, .kwm, .laccdb, .lbf, .lck, .ldf, .lit, .litemod, .litesql, .lock, .log, .ltx, .lua, .m, .m2ts, .m3u, .m4a, .m4p, .m4v, .ma, .mab, .mapimail, .max, .mbx, .md, .mdb, .mdc, .mdf, .mef, .mfw, .mid, .mkv, .mlb, .mmw, .mny, .money, .moneywell, .mos, .mov, .mp3, .mp4, .mpeg, .mpg, .mrw, .msf, .msg, .myd, .nd, .ndd, .ndf, .nef, .nk2, .nop, .nrw, .ns2, .ns3, .ns4, .nsd, .nsf, .nsg, .nsh, .nvram, .nwb, .nx2, .nxl, .nyf, .oab, .obj, .odb, .odc, .odf, .odg, .odm, .odp, .ods, .odt, .ogg, .oil, .omg, .one, .orf, .ost, .otg, .oth, .otp, .ots, .ott, .p12, .p7b, .p7c, .pab, .pages, .pas, .pat, .pbf, .pcd, .pct, .pdb, .pdd, .pdf, .pef, .pem, .pfx, .php, .pif, .pl, .plc, .plus_muhd, .pm!, .pm, .pmi, .pmj, .pml, .pmm, .pmo, .pmr, .pnc, .pnd, .png, .pnx, .pot, .potm, .potx, .ppam, .pps, .ppsm, .ppsx,.ppt, .pptm, .pptx, .prf, .private, .ps, .psafe3, .psd, .pspimage, .pst, .ptx, .pub, .pwm, .py, .qba, .qbb, .qbm, .qbr, .qbw, .qbx, .qby, .qcow, .qcow2, .qed, .qtb, .r3d, .raf, .rar, .rat, .raw, .rdb, .re4, .rm, .rtf, .rvt, .rw2, .rwl, .rwz, .s3db, .safe, .sas7bdat, .sav, .save, .say, .sd0, .sda, .sdb, .sdf, .sh, .sldm, .sldx, .slm, .sql, .sqlite, .sqlite3, .sqlitedb, .sqlite-shm, .sqlite-wal, .sr2, .srb, .srf, .srs, .srt, .srw, .st4, .st5, .st6, .st7, .st8, .stc, .std, .sti, .stl, .stm, .stw, .stx, .svg, .swf, .sxc, .sxd, .sxg, .sxi, .sxm, .sxw, .tax, .tbb, .tbk, .tbn, .tex, .tga, .thm, .tif, .tiff, .tlg, .tlx, .txt, .upk, .usr, .vbox, .vdi, .vhd, .vhdx, .vmdk, .vmsd, .vmx, .vmxf, .vob, .vpd, .vsd, .wab, .wad, .wallet, .war, .wav, .wb2, .wma, .wmf, .wmv, .wpd, .wps, .x11, .x3f, .xis, .xla, .xlam, .xlk, .xlm, .xlr, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xps, .xxx, .ycbcra, .yuv, .zip.
As with most ransomware threats, the best protection against these infections is to ensure that a good backup of all files exists. If computer users can recover their files from a backup, then the con artists responsible for ransomware Trojans will lose any hold they have over their victims.
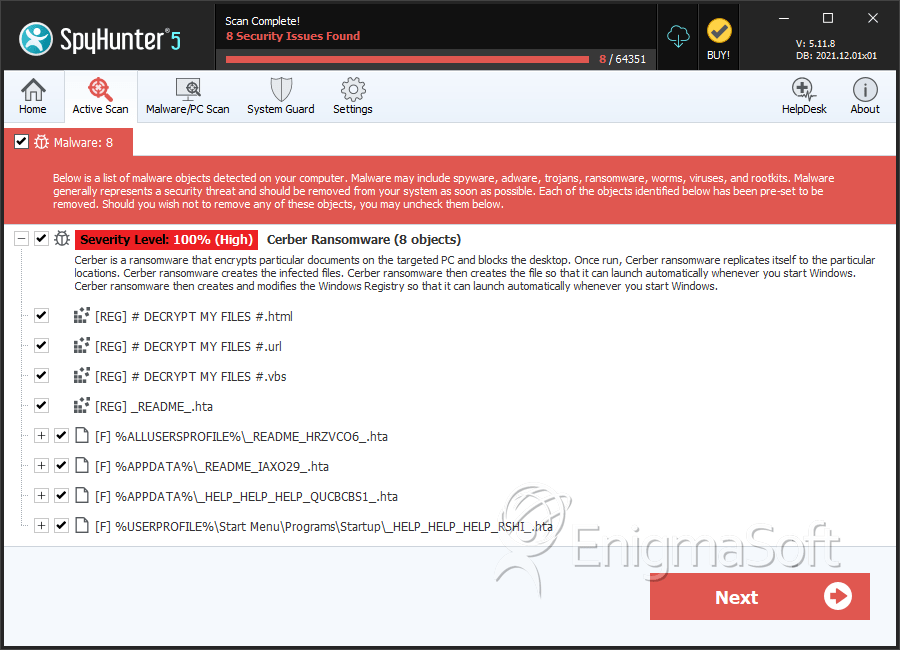
SpyHunter Detects & Remove Cerber2 Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | README.hta | 777e13c9a5cad4e1d2134d5104188ff6 | 43 |
| 2. | _HELP_HELP_HELP_QUCBCBS1_.hta | c042f1d91619e9b4f91bf1e1b78fee85 | 14 |
| 3. | _HELP_HELP_HELP_RSHI_.hta | a46e5f2ce8a20bbb8548959debb9ac0c | 10 |
| 4. | _HELP_HELP_HELP_STOV8H1_.hta | 1632ca0953d5499bf251455159a80ea0 | 6 |
| 5. | _HELP_HELP_HELP_ND8FZ.hta | 041ef4b6a12e0b3165172884301b0d1e | 5 |
| 6. | _HELP_HELP_HELP_Z49XU_.hta | 243d0fd4f4bee5f11698c20d43b958ff | 4 |
| 7. | _HELP_HELP_HELP_XJ7UC8.hta | 4ab1a256a5115d00fa7a3222936ddc03 | 3 |
| 8. | _HELP_HELP_HELP_WMB7F1L.hta | 9befacccf34d60ad1f141e531ddbba52 | 3 |
| 9. | _HELP_HELP_HELP_XFCV_.hta | 01ec9e50d17de043a23997d6562293ad | 3 |
| 10. | _HELP_HELP_HELP_2AK4U21_.hta | 55790c64ce1ff75647d5cadcadf3876e | 3 |
| 11. | _HELP_HELP_HELP_3NNARI.hta | 0ef13a9213c456db231825061eec294c | 2 |
| 12. | _HELP_HELP_HELP_L41VV_.hta | c63b4a524713e4c5f3802463cb46dab8 | 2 |
| 13. | _READ_THI$_FILE_L81EB65A_.hta | 2a6828d2ba37bb97efb4773619b80715 | 2 |
| 14. | _HELP_HELP_HELP_KJ2P.hta | 6689ad9f43ab19a1ccfad9db6a16b772 | 1 |
| 15. | _HELP_HELP_HELP_IGTRU.hta | c1ea46e1877d089983a4d9060997b04f | 1 |
| 16. | _HELP_HELP_HELP_5B3HEZ6.hta | b10e6f69d0c16008410b5c8cfaae0138 | 1 |
| 17. | _HELP_HELP_HELP_8EWN8.hta | 6f59455817d32c34ae35aac63043f285 | 1 |
| 18. | _HELP_HELP_HELP_2R9I63OS.hta | a2daec078c54bb6bc5e96038a1506f2c | 1 |
| 19. | _HELP_HELP_HELP_UYUR4YE.hta | bc0c75128b9cbc02c8c053c1155fb6d9 | 1 |
| 20. | _HELP_HELP_HELP_CKJ4GL.hta | 99d3fc208d3623107cfb18a9069e23bd | 1 |
| 21. | _HELP_HELP_HELP_SUXEZY_.hta | 5190e890725bf431ba44001e190c70f5 | 1 |
| 22. | _HELP_HELP_HELP_GLP9_.hta | 5f7533c663ddb4c0ae4dbbaafb50d491 | 1 |
| 23. | _HELP_HELP_HELP_HUUKTW_.hta | 0224da72bc3638b351cf509cdfc443c2 | 1 |
| 24. | _READ_THI$_FILE_DB3DT9_.hta | 7476a75b0680d99f5338b886bc7def62 | 1 |
| 25. | wP6fT.exe | 731279e3c09f8e52a849c0a9c1043bb5 | 1 |
| 26. | cmdkey.exe | 27cf39d205567505d840391e4761a7a0 | 1 |
| 27. | u.exe | 3dabcb3463ab266e734c83285c977106 | 0 |
