C0hen Locker Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
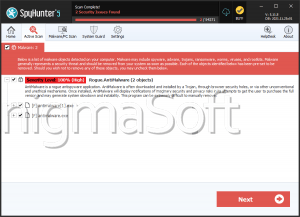
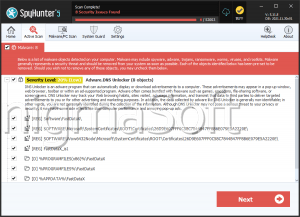
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 1 |
| First Seen: | November 14, 2016 |
| Last Seen: | January 8, 2020 |
| OS(es) Affected: | Windows |
The C0hen Locker Ransomware is a file-locker that was first seen in action in December 2019. This threat is able to encrypt a wide variety of file formats, and, as expected, its purpose is to extort its victims for money. Whenever the C0hen Locker Ransomware infiltrates a computer, it will display a ransom message, which urges the victims to follow certain instructions if they want to get their files back. According to the message that the C0hen Locker Ransomware spawns, the victims have to pay a ransom amount of 0.15 Bitcoin, and then contact the discord user 'c0hen#7722' to receive the decryption tool. The usage of a Discord profile for communication shows that the C0hen Locker Ransomware is a low-quality project, and it would not be a surprise if the authors have no idea how to recover the files of their victims. Victims of the C0hen Locker Ransomware should not agree to cooperate with the cybercriminal behind the attack.
The symptoms of the C0hen Locker Ransomware's attack are easy to recognize – the locked files are marked with the '.c0hen' extension. Furthermore, the threat will spawn a new window, which contains a message from the perpetrators. The window is titled 'c0hen@admin', and it contains the instructions mentioned above.
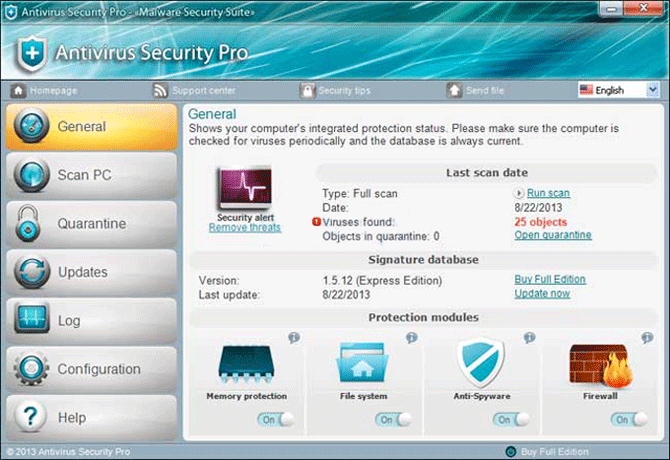
Currently, the only reliable way to counter the C0hen Locker Ransomware's attack is to remove the threat with the use of an up-to-date PC security product, and then restore the damaged files from a backup. If you are not in possession of a backup copy of your files, then you may need to use alternative file recovery options.