C0hen Locker勒索軟件
威脅評分卡
EnigmaSoft 威胁记分卡
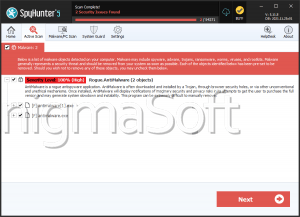
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| 威胁级别: | 100 % (高的) |
| 受感染的计算机: | 1 |
| 初见: | November 14, 2016 |
| 最后一次露面: | January 8, 2020 |
| 受影响的操作系统: | Windows |
C0hen Locker Ransomware是一種文件櫃,於2019年12月首次投入使用。這種威脅能夠加密多種文件格式,並且正如預期的那樣,其目的是為了勒索受害者。每當C0hen Locker勒索軟件侵入計算機時,它將顯示勒索信息,敦促受害者如果要取回文件,請遵循某些指示。根據產生C0hen Locker Ransomware的消息,受害者必須支付0.15比特幣的贖金,然後與不和諧的用戶'c0hen#7722'聯繫,以獲取解密工具。使用Discord配置文件進行通信表明,C0hen Locker Ransomware是一個低質量的項目,如果作者不知道如何恢復受害者的文件,也就不足為奇了。 C0hen Locker Ransomware的受害者不應同意與攻擊背後的網絡犯罪分子合作。
C0hen Locker Ransomware攻擊的症狀很容易識別-鎖定的文件以'.c0hen'擴展名標記。此外,威脅將產生一個新窗口,其中包含來自肇事者的消息。該窗口的標題為“ c0hen @ admin”,其中包含上述說明。
當前,抵抗C0hen Locker Ransomware攻擊的唯一可靠方法是使用最新的PC安全產品消除威脅,然後從備份中恢復損壞的文件。如果您沒有文件的備份副本,則可能需要使用其他文件恢復選項。