BAGAJAI Ransomware
Ransomware programs are malicious software that target individuals and organizations by encrypting (making inaccessible) critical data and demanding payment for its release. To protect their information, users must remain vigilant, practice strong security habits, and utilize effective protection tools to detect and remove these emerging threats.
Table of Contents
Understanding the BAGAJAI Ransomware
BAGAJAI is a ransomware variant in the notorious MedusaLocker family, known for aggressive file-encrypting attacks. Transitioning from general ransomware threats to this specific family, BAGAJAI infiltrates systems, encrypts data, and extorts victims for payment to decrypt their data. BAGAJAI adds a '.BAGAJAI' extension to files, changing '1.jpg' to '1.jpg.BAGAJAI' and '2.png' to '2.png.BAGAJAI'. It leaves a ransom note titled 'read_to_decrypt_files.html' as the main communication.
Inside the BAGAJAI Ransom Note
The ransom note informs victims that their network has been breached and their data is encrypted using RSA-4096 and AES-256. Attackers claim to have stolen sensitive data—financial records, personal files, and business documents—which they threaten to leak if unpaid. Victims must respond within 72 hours or face additional fees.
Criminals offer to decrypt up to three small files for free. The note warns that modifying encrypted files or using recovery tools may cause permanent data loss. These tactics pressure victims into compliance rather than encourage them to seek help.
Decryption, Risks, and Recovery
Decryption without attackers is usually impossible, except when encryption is flawed. Paying the ransom is risky—many victims never receive a decryptor. Paying also funds cybercrime.
After BAGAJAI is removed, files stay locked. Secure, up-to-date backups are the best recovery method. Store backups on separate devices or servers to ensure access after an attack.
How BAGAJAI and Other Ransomware Infect Systems
Ransomware spreads through social engineering and deception. Attackers trick users with misleading messages or bundled content. Malicious files often appear as executables, archives, or infected documents.
Common infection vectors include:
- Spam campaigns and phishing emails containing malicious attachments or links.
- Drive-by downloads and deceptive websites posing as legitimate platforms.
- Freeware or pirated software hosted on untrustworthy sources.
- Malvertising, trojans, fake system updates, and software cracks.
Ransomware can spread through local networks and devices, making containment difficult after infection.
Strengthening Cybersecurity Defenses
Preventing ransomware requires disciplined, layered security. Users should follow these practices to reduce risk:
- Exercise caution with communications: Avoid opening attachments or clicking on links in unsolicited or suspicious emails, text messages, or social media posts.
- Rely on trusted sources: Only download software and files from official websites or verified app stores, and avoid pirated content or third-party activation tools.
- Keep systems updated: Install security fixes for your operating system, browser, and other programs to patch weaknesses that ransomware can exploit.
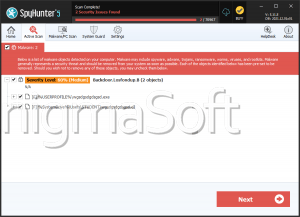
- Use reputable security software: Run regular scans with trusted antivirus or anti-malware tools capable of detecting threats.
- Maintain secure backups: Store copies on external devices or servers not connected to your main system; this allows quick recovery after an attack.
- Avoid unsafe browsing: Don’t interact with suspicious ads or pop-ups and disable browser permissions for untrusted sites.
By following these steps and staying vigilant, users can reduce the risk and impact of ransomware.