BabbleLoader Malware
Cybersecurity experts have identified a new, highly covert threat known as BabbleLoader, which has been observed deploying information-stealing tools like WhiteSnake and Meduza.
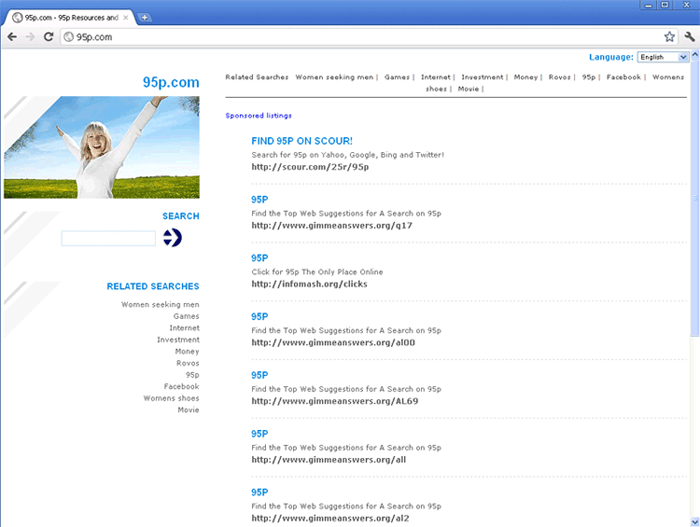
BabbleLoader employs advanced evasion tactics, featuring robust defense mechanisms to bypass antivirus programs and sandbox environments. Its purpose is to load stealers directly into memory. Reports indicate that BabbleLoader has been utilized in multiple campaigns targeting English- and Russian-speaking audiences. These operations primarily focus on users searching for cracked software and business professionals in finance and administrative roles, disguising themselves as accounting software.
Table of Contents
The Role of Loaders in Malware Attacks
Loaders have become a widely utilized method for deploying threats such as stealers and ransomware, often serving as the initial phase of an attack. They are designed to evade traditional antivirus detection by integrating extensive anti-analysis and anti-sandboxing techniques.
This trend is evident in the continuous emergence of new loader families over recent years. Examples include the Dolphin Loader, Emmental, FakeBat, and Hijack Loader, which have been leveraged to distribute various payloads, including CryptBot, Lumma Stealer, SectopRAT, SmokeLoader, and Ursnif.
BabbleLoader Is Equipped with Numerous Evasion Techniques
BabbleLoader stands out due to its sophisticated evasion techniques, which can deceive both traditional and AI-driven detection systems. These methods include the use of junk code and metamorphic transformations, which alter the loader's structure and execution flow to bypass signature-based and behavioral analyses.
The loader avoids static analysis by resolving critical functions only at runtime and employs measures to thwart sandbox-based examinations. Additionally, it incorporates excessive amounts of meaningless code, designed to overwhelm and crash disassembly or decompilation tools like IDA, Ghidra, and Binary Ninja, necessitating manual analysis.
Each iteration of BabbleLoader is uniquely crafted, featuring distinct strings, metadata, code, hashes, encryption methods, and control flows. While individual samples share minimal code snippets, their structures are mainly unique. Even file metadata is randomized to further obscure patterns.
This continuous variation forces AI detection models to constantly adapt, often resulting in missed detections or false positives due to the rapid and unpredictable changes in the loader's design.
BabbleLoader Paves the Way for Further Compromise of Systems
At its core, BabbleLoader is designed to load a shellcode that subsequently decrypts and delivers a Donut loader, which then unpacks and activates the stealer malware.
The more effectively loaders can safeguard the final payloads, the fewer resources attackers need to invest in rotating compromised infrastructure. BabbleLoader employs various techniques to shield itself from detection, allowing it to remain competitive in the crowded loader and crypter landscape.
BabbleLoader Malware Video
Tip: Turn your sound ON and watch the video in Full Screen mode.