Zpas Ransomware
Zpas is a malware threat that belongs to the ransomware category. Its primary function is to encrypt data on the victim's system, effectively blocking access to the files. In addition to encryption, Zpas also alters the names of the impacted files by appending the extension '.zpas' to them. For instance, a file named '1.doc' would be changed to '1.doc.zpas', and '2.png' would become '2.png.zpas', and so on.
To further establish its presence and communicate with the victim, Zpas drops a ransom note named '_readme.txt.' This note typically contains instructions from the attackers on how to make the ransom payment and regain access to the encrypted files.
It's worth noting that the Zpas Ransomware has been identified as a variant within the STOP/Djvu Ransomware family. This family of ransomware has been associated with various distribution methods, including being deployed on breached devices alongside information stealers like RedLine and Vidar. These additional threats can result in the theft of sensitive information from the victim's system, further exacerbating the consequences of a Zpas Ransomware attack.
The Files on the Devices Infected with the Zpas Ransomware will be Locked
The ransom note delivered by the Zpas Ransomware informs victims that in order to regain access to their encrypted files, they must pay a ransom to the attackers for the decryption software and a unique key. The note outlines two payment options based on the timeframe within which the victim contacts the threat actors.
If victims make contact with the threat actors within 72 hours, they are given the option to purchase the decryption tools for a reduced price of $490. However, if the initial 72-hour window elapses, the full payment amount of $980 is required to obtain the necessary decryption. The ransom note provides two email addresses - 'support@freshmail.top' and 'datarestorehelp@airmail.cc,' as the means of communication with the threat actors for payment instructions.
The ransom note includes a provision that allows victims to send one file that does not contain any vital or sensitive information to the attackers before making the payment. This particular file will be decrypted by the threat actors at no cost to the victim, presumably as a demonstration of their capability to unlock the encrypted files.
Remember that paying the ransom should be approached with caution, as there is no certainty that the threat actors will honor their end of the bargain and provide the necessary decryption tool. Generally, it is not recommended to comply with ransom demands, as it supports criminal activities and may not result in the recovery of the files.
Take Effective Measures against Malware Threats
In the realm of cybersecurity, protecting against ransomware attacks demands a multifaceted approach that involves a series of interconnected defense layers. Establishing a comprehensive defense strategy is critical for thwarting the infiltration and propagation of ransomware within an organization's network. By embracing a proactive mindset and implementing effective strategies, businesses can significantly decrease their susceptibility to these destructive cyberattacks.
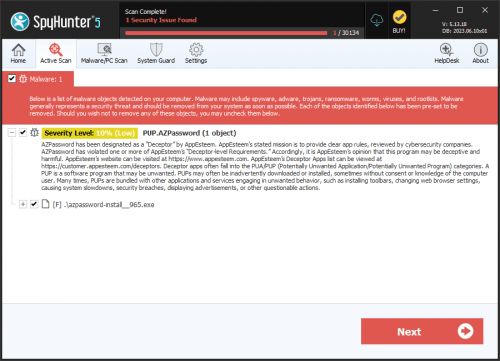
To begin, maintaining up-to-date and robust security software is of paramount importance. This encompasses the deployment of trusted anti-malware solutions designed to identify and intercept ransomware threats. Regular updates for these security tools are imperative, as they ensure that the software remains armed with the latest threat intelligence, enabling the prompt detection and neutralization of emerging ransomware variants.
Equally crucial is the focus on regular software updates and meticulous patch management. Staying current with security patches for operating systems, applications, and firmware is essential to address potential vulnerabilities that malicious actors might exploit. Applying patches to known security weaknesses effectively closes off potential entry points for ransomware, thereby bolstering the overall security of the system.
User education and awareness represent a pivotal aspect of ransomware prevention. Organizations must provide comprehensive cybersecurity training to their employees to ensure a profound understanding of the risks associated with suspicious emails, malicious websites, and unsafe downloads. By fostering a culture of security consciousness and promoting best practices, such as refraining from clicking on dubious links or opening email attachments from unknown sources, employees become integral contributors to the defense against ransomware attacks.
Additionally, the implementation of a robust backup strategy cannot be overstated. Consistently backing up critical data to offline or cloud-based storage serves as a contingency plan in the event of a ransomware incident. Reliable and rigorously tested backup systems empower organizations to restore encrypted files without resorting to ransom payments. It is essential to maintain secure and isolated backups to prevent the spread of ransomware to backup repositories.
Network segmentation and access controls also play a pivotal role in mitigating the impact of ransomware attacks. Strong network segmentation practices help contain the proliferation of malware within an organization's infrastructure. By partitioning networks and confining access privileges based on the principle of least privilege, organizations can curtail the lateral movement of ransomware and minimize potential damage.
In conclusion, preventing ransomware attacks requires a multifaceted approach that combines various security measures. By integrating advanced security software, comprehensive user education, robust backup strategies, network segmentation, vulnerability management, and an effective incident response plan, organizations can significantly reduce their vulnerability to ransomware attacks. This comprehensive approach not only protects critical data and systems but also fortifies the overall cybersecurity posture of the organization.
The full text of the ransom note left by Zpas Ransomware is:
'ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-cfHHerNTF6
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshmail.topReserve e-mail address to contact us:
datarestorehelp@airmail.ccYour personal ID:'