Zepto Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 35 |
| First Seen: | June 29, 2016 |
| Last Seen: | October 24, 2025 |
| OS(es) Affected: | Windows |
Zepto Ransomware Image
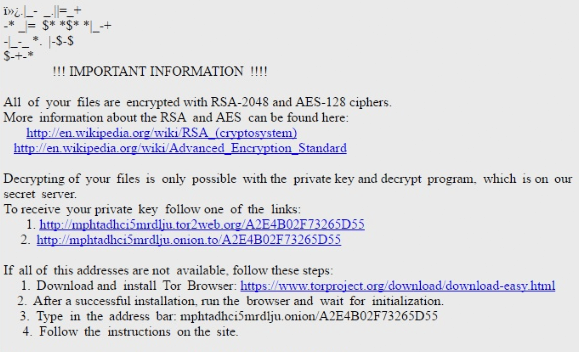
The Zepto Ransomware is a variant of the Trojan Locky Ransomware. The Zepto Ransomware is designed to infect all versions of the Windows operating system, from Windows XP all the way to Windows 10. Ransomware Trojans like the Zepto Ransomware are especially threatening because, even if removed, the victim's files will still be inaccessible. Essentially, the Zepto Ransomware takes the victim's files hostage, encrypting them and demanding the payment of a ransom to decrypt them. Since the files encrypted by the Zepto Ransomware are impossible to recover without access to the decryption key, PC security analysts advise that computer users take immediate preventive measures to avoid becoming victims of this and similar ransomware Trojan attacks.
Table of Contents
The Files Encrypted by the Zepto Ransomware may be Lost Forever
When the Zepto Ransomware is installed on the victim's computer, it scans the victim's files and encrypts them using a strong encryption algorithm. The Zepto Ransomware changes the files' extensions to '.the Zepto' to identify the files that have been encrypted. Once a file is encrypted by the Zepto Ransomware it becomes inaccessible. After encrypting the victim's files, the Zepto Ransomware delivers a ransom note instructing the victim on what to do next. Unfortunately, computer users will have little choices left after the Zepto Ransomware has encrypted the files on the affected computer. The following are examples of files that are targeted by the Zepto Ransomware and similar threats:
.123 | .3dm | .3ds | .3g2 | .3gp | .602 | .aes | .ARC | .asc | .asf | .asm | .asp | .avi | .bak | .bat | .bmp | .brd | .cgm | .cmd | .cpp | .crt | .csr | .CSV | .dbf | .dch | .dif | .dip | .djv | .djvu | .DOC | .docb | .docm | .docx | .DOT | .dotm | .dotx | .fla | .flv | .frm | .gif | .gpg | .hwp | .ibd | .jar | .java | .jpeg | .jpg | .key | .lay | .lay6 | .ldf | .m3u | .m4u | .max | .mdb | .mdf | .mid | .mkv | .mov | .mp3 | .mp4 | .mpeg | .mpg | .ms11 | .MYD | .MYI | .NEF | .odb | .odg | .odp | .ods | .odt | .otg | .otp | .ots | .ott | .p12 | .PAQ | .pas | .pdf | .pem | .php | .png | .pot | .potm | .potx | .ppam | .pps | .ppsm | .ppsx | .PPT | .pptm | .pptx | .psd | .rar | .raw | .RTF | .sch | .sldm | .sldx | .slk | .stc | .std | .sti | .stw | .svg | .swf | .sxc | .sxd | .sxi | .sxm | .sxw | .tar | .tbk | .tgz | .tif | .tiff | .txt | .uop | .uot | .vbs | .vdi | .vmdk | .vmx | .vob | .wav | .wb2 | .wk1 | .wks | .wma | .wmv | .xlc | .xlm | .XLS | .xlsb | .xlsm | .xlsx | .xlt | .xltm | .xltx | .xlw | .zip.
Dealing with the Zepto Ransomware and Similar Threats
As mentioned before, the best method is prevention. The following are steps computer users can take to avoid becoming victims of the Zepto Ransomware attack and similar ransomware Trojans:
- Back up all files regularly on an off-site location. The Zepto Ransomware and similar attacks rely on taking the computer users' files hostage, making them inaccessible until the victim pays for the decryption key. If the victim is able to recover the files from a back-up, then the Zepto Ransomware attack becomes completely ineffective.
- Use a strong anti-malware program that is fully up-to-date to detect the Zepto Ransomware before it is installed on your computer. If your anti-malware software is running at all times and is appropriately reliable, it will be able to intercept the Zepto Ransomware and similar threats before they can carry out their attacks on your computer.
- Avoid opening unsolicited email attachments and embedded links. Threats like the Zepto Ransomware may be distributed using corrupted email attachments and links. If computer users learn to spot and prevent these tactics, it will reduce the chances of becoming infected with one of these threats greatly.
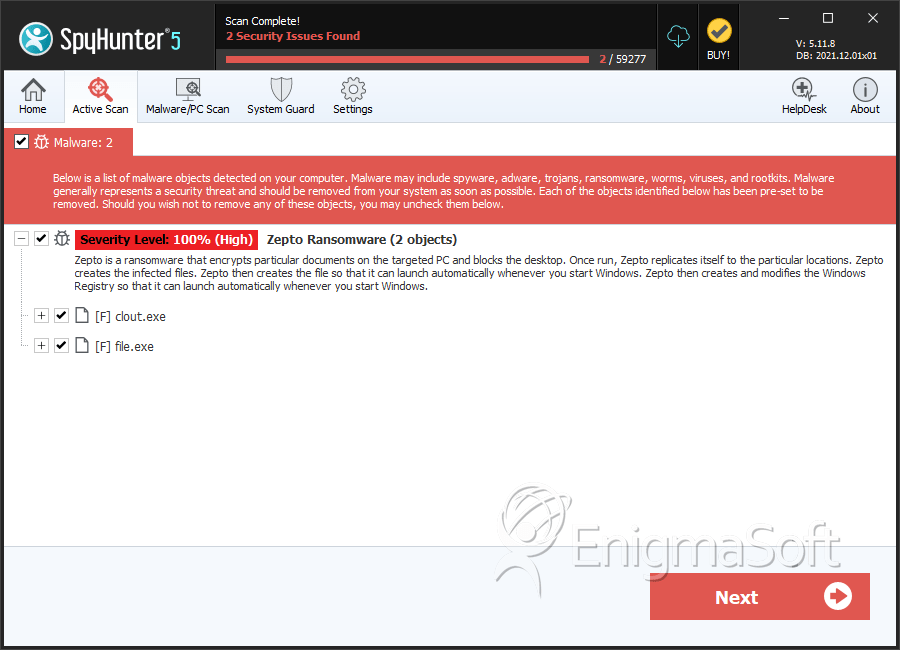
SpyHunter Detects & Remove Zepto Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 65b84d4e47406489c3ad7e48defa09e8 | 2 |
| 2. | clout.exe | 31e125faf22ae2ab6c91ece657808c60 | 0 |
