Zen Ransomware
The importance of safeguarding devices against malicious threats cannot be overstated. Cybercriminals are continuously devising new ways to exploit vulnerabilities, with ransomware being one of the most formidable adversaries. Among these, Zen Ransomware stands out as a potent threat that underscores the need for robust cybersecurity practices.
Table of Contents
Zen Ransomware: A Silent Predator
Discovered during the analysis of advanced malware threats, Zen Ransomware has quickly made a name for itself. It belongs to the notorious Dharma ransomware family and employs sophisticated techniques to compromise devices. Once Zen gains access to a system, it encrypts files, changing their names to include a unique ID, the attackers' email, and the '.zen' extension. For instance, a file like '1.png' becomes '1.png.id-9ECFA84E.[zen_crypt@tuta.io].zen.'
The ransomware leaves behind an ominous note in a text file ('info.txt') and a pop-up window, both of which instruct victims to pay a ransom in Bitcoin. In a manipulative tactic, Zen offers to decrypt up to three files as a demonstration, urging victims to trust them. However, victims are warned not to rename encrypted files or use third-party recovery tools, as this could lead to permanent data loss.
Elusive and Persistent: The Stealth of Dharma Family
Zen shares key traits with other Dharma ransomware variants. It disables processes associated with open files to ensure it can encrypt them, targeting both local and network-shared files while avoiding critical system files to keep the infected system operational. Deleting Volume Shadow Copies removes built-in recovery options, tightening its grip on compromised data.
Persistence is achieved through strategic placement and auto-start mechanisms, ensuring Zen runs each time the system boots. Zen also gathers geolocation data to determine whether to proceed with encryption, an unsettling reminder of the targeted nature of these attacks.
The Human Factor: Attack Vectors and Social Engineering
Zen Ransomware typically infiltrates systems via exposed RDP services, exploiting weak or poorly managed credentials through brute-force attacks. However, it's not limited to this method alone. Cybercriminals frequently turn to phishing and social engineering, sending infected attachments or links through spam emails, instant messages, or deceptive pop-ups. Moreover, the use of malicious downloads from dubious websites, pirated software, or fake updates continues to be a prevalent entry point for this ransomware.
Zen, like many malware variants, can also propagate through local networks and removable media, making it a significant risk for businesses and individuals alike.
Best Practices: Strengthening Your Digital Fortress
Given the advanced capabilities of Zen Ransomware, prevention is key. Here are crucial best practices every user should implement:
- Regular Backups: Maintain secure, offline backups of important data. These backups should be stored separately from your main system to prevent them from being targeted by ransomware.
- Update and Patch: Ensure your operating system, software, and firmware are always updated with the latest security patches. Many ransomware attacks exploit outdated software vulnerabilities.
- Strong Authentication: Use complex, unique passwords for all accounts, especially for remote access tools like RDP. Where possible, enable multi-factor authentication to add an extra layer of security.
- Network Segmentation: Isolate critical systems and sensitive data from general network access. This limits the damage ransomware can inflict if it does breach your network.
- Restrict Privileges: Apply the principle of least privilege, ensuring users only have access to the data and systems essential for their work.
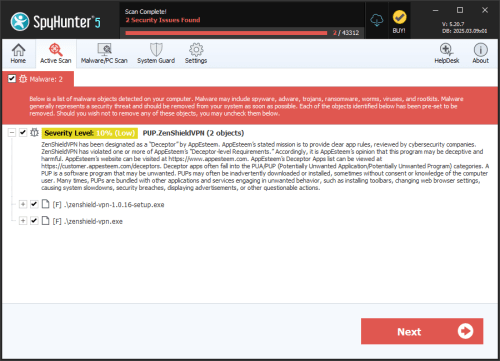
- Antivirus and Firewall: Deploy reputable antivirus software and ensure firewalls are properly configured. Keep these defenses updated and scan your system regularly.
- Educate and Train: Cybersecurity awareness is crucial. Train employees and family members to recognize suspicious emails, links, and attachments. Promote cautious online behavior.
- Disable Unnecessary Features: Deactivate services like RDP if not in use, and limit the number of users with remote access.
Conclusion: Staying Vigilant
Zen Ransomware is a potent reminder of the evolving and persistent threat posed by ransomware. With its roots in the Dharma family, Zen's capabilities highlight the need for constant vigilance and proactive security measures. While removal of the malware is essential, restoring encrypted files without backups remains improbable. Therefore, focusing on prevention through a combination of technical defenses and informed digital practices is the most effective way to safeguard your data and digital life against the devastating impact of ransomware.