Worm.Brontok
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 3,385 |
| Threat Level: | 50 % (Medium) |
| Infected Computers: | 58,555 |
| First Seen: | July 24, 2009 |
| Last Seen: | May 20, 2026 |
| OS(es) Affected: | Windows |
Worm.Brontok is a mass mailing worm that is spread through an email attachment. The subject of the infected email will be either "Fotoku yg Paling Cantik" or "My Best Photo". The Worm.Brontok's email text reads:
From: "angelina_ph@[recipient’s domain]" or "jennifer_sh@[recipient’s domain]"
Subject: "Fotoku yg Paling Cantik" or "My Best Photo"
Message text:
"Hi,
Aku lg iseng aja pengen kirim foto ke kamu.
Jangan lupain aku ya !.
Thanks"
or
"Hi,
I want to share my photo with you.
Wishing you all the best.
Regards,"
Attachment name: Photo.zip
Once the Worm.Brontok file is executed it replicates itself to Windows system folder and to other folders such as:
csrss.exe
inetinfo.exe
lsass.exe
services.exe
smss.exe
norBtok.exe
cvt.exe
IDTemplate.exe
3D Animation.scr
A.kotnorB.com
Empty.pif
KANGEN.EXE
winlogon.exe
The Worm.Brontok also changes the registry run section so it may load automatically on subsequent startups. Below are the registry modifications:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run Tok-Cirrhatus = "%UserProfile%\Application Data\smss.exe"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
Bron-Spizaetus = "%Windows%\INF\norBtok.exe"
Worm.Brontok can disable the user's system registry tools and the command line (cmd.exe) in order to avoid detection and to make manual removal difficult. Worm.Brontok is a malicious worm and should be removed from the users PC immediately.
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| TrendMicro | WORM_RONTOKBRO.H |
| Sophos | W32/Brontok-DB |
| Panda | W32/Brontok.CX.worm |
| NOD32 | Win32/Brontok.G |
| Microsoft | Worm:Win32/Brontok@mm |
| Fortinet | W32/Rontokbro.H@mm |
| eTrust-Vet | Win32/Robknot.H |
| Comodo | Worm.Win32.Brontok.G |
| ClamAV | Worm.Brontok.Y |
| BitDefender | Worm.Generic.73749 |
| Avast | Win32:Rontokbr-H2 |
| Authentium | W32/Brontok.D@mm |
| AntiVir | Worm/Rontok.D |
| AhnLab-V3 | Win-Trojan/Xema.variant |
| TrendMicro | WORM_RONTKBR.AF |
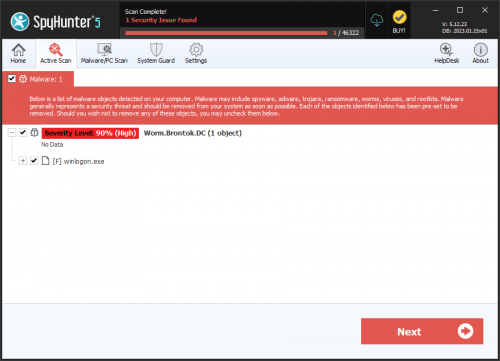
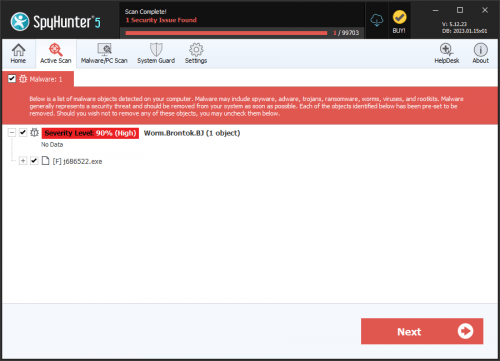
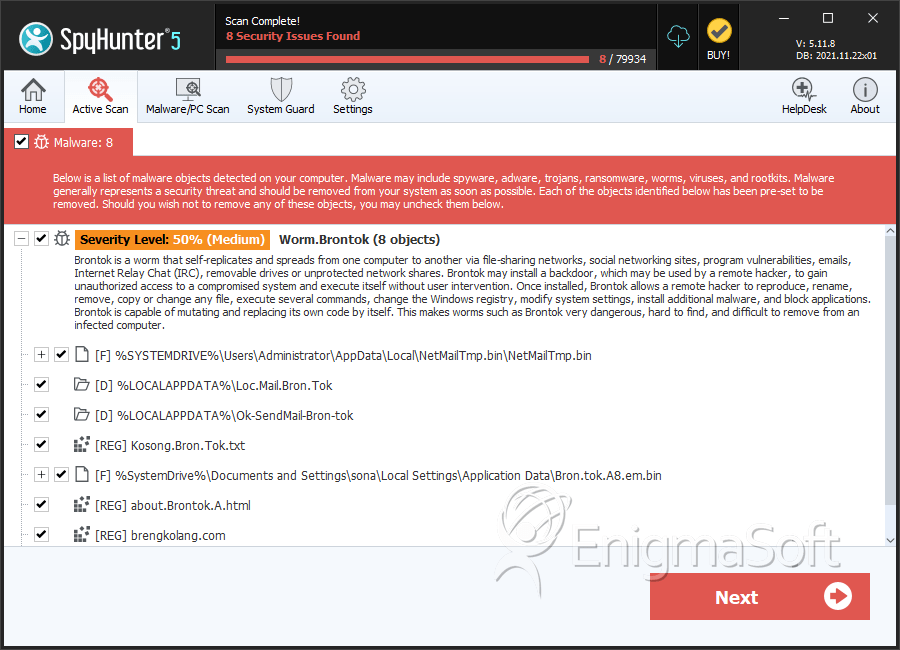
SpyHunter Detects & Remove Worm.Brontok
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | NetMailTmp.bin | c943ae4292f2ea5d3a9fea05d9af4039 | 27,021 |
| 2. | Bron.tok.A8.em.bin | 7b41ac483cfde60a7467a338d8f76175 | 6,248 |
| 3. | A.kotnorB.com | 11c8a4a807073ccf7734288293c50407 | 205 |
| 4. | bronstab.exe | 24a16f71bad9e8ae83246abea4ac4a66 | 154 |
| 5. | sempalong.exe | 4c0c85d815a2dc079bb21c7f31950f58 | 60 |
| 6. | RakyatKelaparan.exe | cddb5bd741c5e40d515ac0fd49c558fa | 34 |
| 7. | smss.exe | 0d02610d508d6db137585c40596e9b19 | 32 |
| 8. | winlogon.exe | a575dd2441173753bb7a0c058d8b1aef | 0 |
| 9. | csrss.exe | 9488b369de58ae7abb9d2a37c8d67745 | 0 |
| 10. | SERVICES.exe | d32e51ada4d466ae9ff7fbf70962913c | 0 |
| 11. | lsass.exe | 08f906036eba5d81efad7b1a932b5d56 | 0 |
| 12. | file.exe | b9a894d0f76966512e5472a37777eb8c | 0 |
| 13. | j6235022.exe | 3fc2a99453a99947672585715c815032 | 0 |
Registry Details
Directories
Worm.Brontok may create the following directory or directories:
| %LOCALAPPDATA%\Loc.Mail.Bron.Tok |
| %LOCALAPPDATA%\Ok-SendMail-Bron-tok |
| %USERPROFILE%\Local Settings\Application Data\Loc.Mail.Bron.Tok |
| %USERPROFILE%\Local Settings\Application Data\Ok-SendMail-Bron-tok |
| %WINDIR%\SysWOW64\n4431 |