WinSec Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
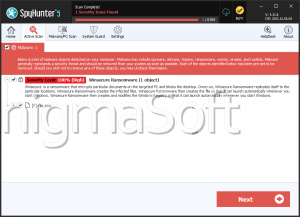
| Threat Level: | 100 % (High) |
| Infected Computers: | 18 |
| First Seen: | April 13, 2017 |
| Last Seen: | October 18, 2020 |
| OS(es) Affected: | Windows |
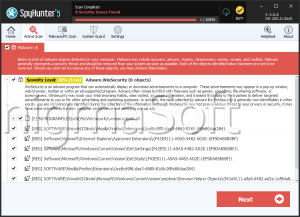
The WinSec Ransomware is a ransomware Trojan that is based on the HiddenTear open source ransomware engine that was made available publicly in October of 2015. Since the release of the HiddenTear engine, countless ransomware variants have appeared, causing damage to numerous computer users around the world. The WinSec Ransomware is just one of many variants in this family of ransomware. The WinSec Ransomware was first observed on April 10, 2017, and seems to target computer users located in Brazil. The WinSec Ransomware supports a version in Portuguese and is delivered to the victim's computers through spam email messages that seem to come from companies that computer users in Brazil would recognize. The WinSec Ransomware may be delivered by attaching a document with corrupted macros to these emails. When computer users open the document, the macros connect to a remote server and download and install the WinSec Ransomware on the victim's computer.
Table of Contents
How the WinSec Ransomware Attack Works
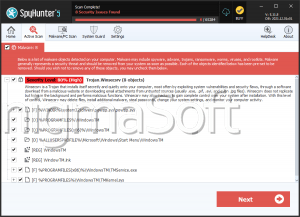
The WinSec Ransomware carries out an attack that is typical of these infections. The WinSec Ransomware encrypts the victim's files, targeting a wide variety of files that can include photos, videos, and other documents. The WinSec Ransomware targets computer users that speak Portuguese and delivers a ransom message in this language. The WinSec Ransomware scans the drives of the affected computer, including removable memory devices and network storage in its attack. The WinSec Ransomware searches for certain file types, such as those associated with popular file extensions, and then encodes the victim's files using a combination of the RSA 2048 and AES 256 encryptions. The files encrypted by the WinSec Ransomware become inaccessible completely since they will be locked away from the victim unless the decryption key is used. When the WinSec Ransomware encrypts the files, they can be identified easily because they will have the file extension '.locked' and show up as blank icons on Windows Explorer since their contents will no longer be recognized.
The Ransom Message Displayed by the WinSec Ransomware
The WinSec Ransomware receives its name because it runs as 'winsec.exe,' a file located in the AppData directory. The WinSec Ransomware includes a decryption panel or pop-up that seems to match the theme that is used in the Windows 8 operating system. The WinSec Ransomware message is delivered in this panel, and contains the following text (each delivered in a different slide or step):
'DATA ON THIS DEVICE WAS LOCKED
Follow the instructions to unlock your data
• Step 1 • Step 2 • Step 3
Enter your email address to get your unlock key:
Next step'
The victim is asked to pay a large ransom to recover the affected files. Different variants of the WinSec Ransomware will demand different BitCoin amounts, asking for the money to be delivered to a specific BitCoin wallet. The amount that the WinSec Ransomware demands will vary, but should be between 0.5 and 1.5 BitCoin ($600 and $1800 USD at the current exchange rate).
Dealing with the WinSec Ransomware Infection
Computer users shouldn't pay the WinSec Ransomware ransom. In many cases, the con artists will simply ignore the payment or ask for more money from the victim. More importantly, paying these ransoms allows fraudsters to continue creating threats and claiming new victims. Instead of paying the WinSec Ransomware ransom, take preventive measures to limit the damage caused by threats like the WinSec Ransomware, especially as these threats become more common. The best protection against the WinSec Ransomware and other ransomware Trojans is to have backup copies of all files. Backups allow computer users to ignore the ransom demands entirely, simply restoring the compromised files from the backup. Apart from file backups, computer users should have a security program that can help computer users intercept the WinSec Ransomware infection before it carries out its attack.