Windows Premium Defender
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 15,846 |
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 6 |
| First Seen: | July 13, 2012 |
| Last Seen: | May 6, 2024 |
| OS(es) Affected: | Windows |
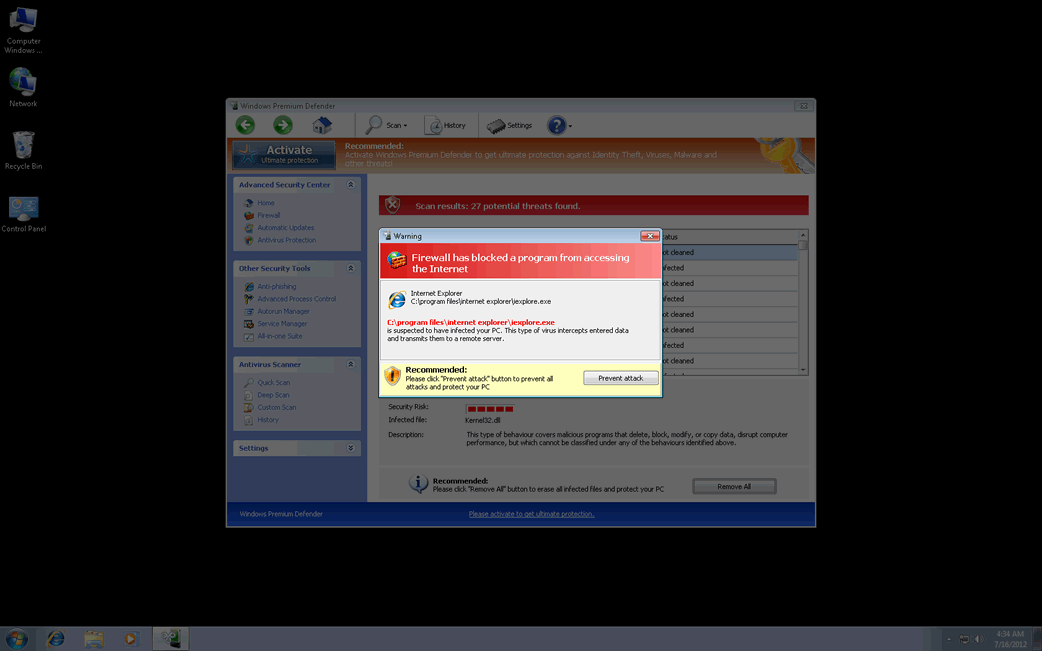
Windows Premium Defender Image
Windows Premium Defender is one of the many existing fake security applications in the infamous FakeVimes family. This family of malware, active since 2009, has been especially active in 2012 due to the addition of a dangerous rootkit component to WinPC Defender bogus security applications. This rootkit is a variant in the Sirefef family of rootkits. While malware in the FakeVimes family were released before 2012 was not particularly difficult to remove, the addition of this rootkit component makes Windows Premium Defender and its many clones considerably more difficult to remove than before. Dealing with a Windows Premium Defender infection will typically require the use of a reliable anti-malware application with anti-rootkit capabilities, or the use of a specialized anti-rootkit tool.
Examples of clones of Windows Premium Defender include WinPC Defender, SystemDefender, IE Defender, IE Defender, XPdefender, WinDefender2008, PC Privacy Defender, Malware Defender 2009, Smart Defender Pro, Ultimate Defender, Advanced XP Defender, Security Defender Pro 2015.
Most Windows Premium Defender infections will be the result of a social engineering attack – that is, criminals will use deception to convince victims to download either Windows Premium Defender or a downloader or dropper Trojan. Some ways in which this can happen include the following:
- Windows Premium Defender may be advertised on unsafe websites, often offering a free scan of your computer system in order to protect it from malware. However, these kinds of advertisements will actually use exploits to install Windows Premium Defender directly or they will claim that your computer system is severely infected so that you will download Windows Premium Defender yourself.
- Another common way criminals deliver Windows Premium Defender and similar fake security programs is through spam email campaigns. Typically, criminals will send out a misleading email message containing an email attachment disguised as a harmless text or image file. However, this attachment will usually contain a Trojan dropper or downloader that can then be utilized to set up Windows Premium Defender.
- The kind of Trojans mentioned above are also commonly disguised as fake video codecs required to view pornographic videos on unsafe websites. After opening the fake video, the victim will receive an error message claiming that it is necessary to download a video codec. However, this supposed codec will actually be a Trojan that can then download and install Windows Premium Defender on the infected computer system.
The main purpose of Windows Premium Defender is to talk its victims into believing that their machines are badly infected with malware. ESG security researchers advise ignoring all notifications that Windows Premium Defender displays and instead using a strong anti-malware program to take care of this pest.
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Panda | Generic Malware |
| AVG | FakeAV_s.EG |
| Fortinet | W32/Kryptik.AIK!tr |
| Ikarus | Trojan-Dropper.Win32.Dapato |
| Microsoft | Rogue:Win32/FakePAV |
| Comodo | ApplicUnwnt.Win32.AdWare.WintionalityChecker.AK |
| Sophos | Troj/FakeAV-FVC |
| K7AntiVirus | Trojan |
| CAT-QuickHeal | Trojan.FakeAV.nncj |
| Panda | Trj/CI.A |
| Fortinet | W32/FakeAV.NNCJ!tr |
| Ikarus | Trojan.Win32.Tibs |
| AhnLab-V3 | Trojan/Win32.FakeAV |
| Microsoft | Trojan:Win32/Tibs |
| McAfee-GW-Edition | Artemis!5599B8B756F8 |
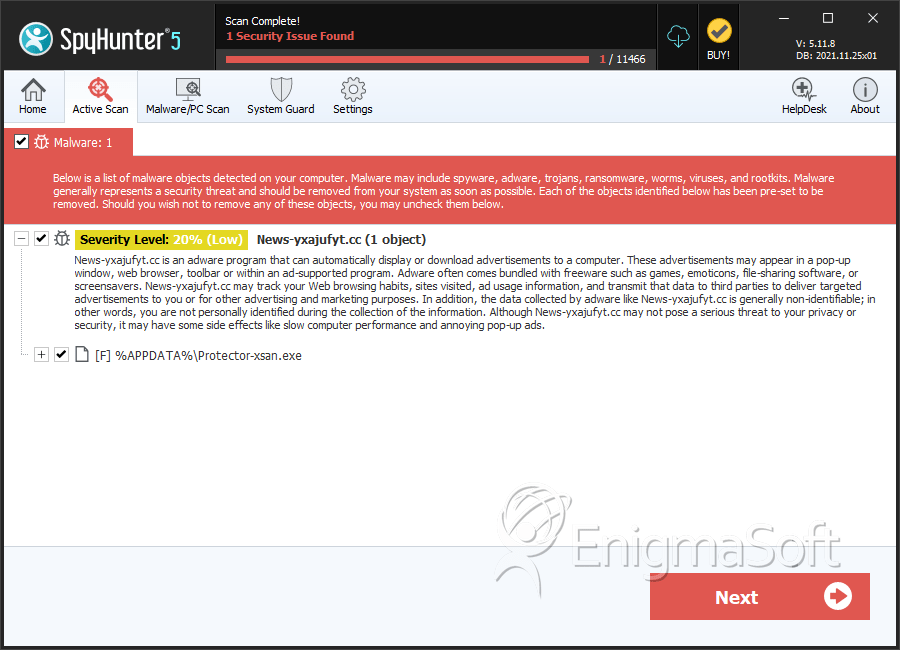
SpyHunter Detects & Remove Windows Premium Defender
Windows Premium Defender Video
Tip: Turn your sound ON and watch the video in Full Screen mode.
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | Windows Premium Defender.exe | 5599b8b756f8ec3a6cc0f6d94bd3be44 | 3 |
| 2. | %AppData%\Protector-[RANDOM 4 CHARACTERS].exe | ||
| 3. | %AppData%\Protector-[RANDOM 3 CHARACTERS].exe | ||
| 4. | %AppData%\NPSWF32.dll | ||
| 5. | %AppData%\1st$0l3th1s.cnf | ||
| 6. | %AppData%\result.db |
