Vulcan Ransomware
In today's interconnected world, safeguarding devices against cyber threats has never been more fundamental. Ransomware, one of the most disruptive threats, continues to evolve, with the Vulcan Ransomware being a recent example. This threatening program preys on unsuspecting users, locking them out of their valuable files and demanding payment to restore access. Understanding its operation and implementing robust security measures can significantly decrease the chances of becoming one more victim of such schemes.
Table of Contents
What is the Vulcan Ransomware?
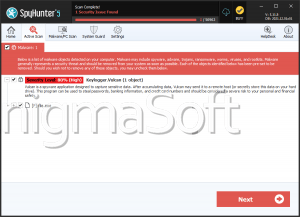
The Vulcan Ransomware belongs to a class of threats designed to encrypt users' files and demand a ransom for decryption. Upon infecting a device, it scans the system for a variety of file types, encrypting them and appending the extension ".vulcan" to each affected file. For instance, a file named document.pdf becomes document.pdf.vulcan.
Once the encryption process is complete, the ransomware delivers its demands through a pop-up window displaying a ransom note. This note instructs victims to pay 100€ in Bitcoin to regain access to their data. Victims are provided with a Bitcoin wallet address—1HX1ys21t6pybS5zT—to send the payment and an email address, kawsexpress@yahoo.com, to contact the attackers for further instructions.
How Does the Vulcan Ransomware Operate?
- Infection and Encryption: The Vulcan Ransomware infiltrates devices through common vectors like malicious email attachments, compromised websites, or bundled software downloads. Once installed, it begins scanning the device for targeted file types, encrypting them to render them inaccessible.
- Ransom Note Delivery: The ransomware then generates a pop-up window containing the ransom note. This note explains the situation, demands 100€ in Bitcoin, and provides the wallet address and email contact details for communication. The attackers use this approach to exert psychological pressure, emphasizing the urgency to push victims into complying.
- Payment and Communication: Victims are often tempted to pay the ransom to recover their files, but this action carries risks. Nothing is guaranteeing that paying the ransom will result in data recovery, as attackers may fail to provide decryption keys or demand additional payments.
The Importance of Preventing Ransomware Attacks
Ransomware attacks like Vulcan can have devastating consequences, including financial losses, data breaches, and significant disruptions. Proactive measures are paramount to prevent such incidents and mitigate their impact.
Best Security Practices to Defend against Ransomware
- Maintain Regular Backups: Regularly back up essential files to an independent device or a secure cloud service. Ensure backups are disconnected from the primary system to prevent them from being encrypted during an attack.
- Enable Multi-Layered Security: Install a reputable anti-malware solution and keep it updated. Use a firewall and ensure all security features are active to detect and block unsafe activities.
- Be Cautious when opening Emails. Avoid approaching attachments or clicking on links in unsolicited emails. Verify the sender's identity before interacting with suspicious messages. Phishing emails are a well-used delivery method for ransomware.
- Keep Software Updated: Regularly update programs and operating systems to remedy vulnerabilities that attackers could exploit. Enable automatic updates where possible.
- Use Strong Passwords: Adopt unique and complex passwords for all accounts and empower two-factor authentication (2FA) to add an extra layer of protection.
- Educate and Train Users: Organizations should train employees on recognizing phishing attempts and safe browsing habits. Personal users should educate themselves on digital hygiene practices.
What to Do if Infected by the Vulcan Ransomware
If you fall victim to the Vulcan Ransomware, resist the urge to pay the ransom. Instead, follow these steps:
- Disconnect the affected device from the net to avoid further spread.
- Report the incident to relevant authorities, such as a cybersecurity organization or local law enforcement.
- Consult cybersecurity professionals to determine whether decryption tools are available.
- Restore data from a clean backup, if available.
Paying the ransom supports criminal activities and may not guarantee the recovery of your data.
Final Thoughts
The Vulcan Ransomware exemplifies the dangers of cyber threats, reminding users of the importance of vigilance and proactive security measures. By implementing robust defenses, staying informed about emerging threats, and maintaining a cautious approach to online activities, users can significantly reduce their exposure to such attacks. Don't forget that prevention is always better than cure in the realm of cybersecurity.
Stay safe and protect your digital world.