Viro Ransomware
There are countless ransomware Trojans active today. In fact, the ransomware industry has become so large that it is difficult to find unique ransomware Trojans, displaying any semblance of creativity or malice that was a hallmark of threats even as little as a decade ago. As ransomware Trojans have been proven to be effective money makers, new ransomware Trojans that have popped up have become sleeker, focused, and geared towards making money specifically. A ransomware Trojan like the Viro Ransomware seems to belong to a category of threats from an older time, where it is not clear exactly what its purpose is, and it seems that it was designed to harass the victim as much as to gather data or generate a profit.
Table of Contents
The Bad Religion-Themed Joke of the Viro Ransomware
The Viro Ransomware seems to be bundled with other threats. In the Viro Ransomware attacks, malware analysts have detected a keylogger infection (designed to collect data by tracking keys pressed on the victim's keyboard and other information) and a worm (a threat infection designed to propagate itself and replicate on the victims' computers.) When the Viro Ransomware infects a computer, the Viro Ransomware will change the infected computer's desktop image by displaying a picture of the well-known Jesus iconography. However, the picture of a smiling individual has been pasted into the picture, replacing Jesus' face. This picture will appear on the infected computer's desktop repeatedly. The Viro Ransomware also will harass the victim with pop-up messages. These pop-ups are titled 'Computer compromised' and display the following message on the infected PC:
'Computer compromised
Your Computer has been infected by a Ransomware. Send us money and enter the password we send you if you want your files back.
[...]
[OK]'
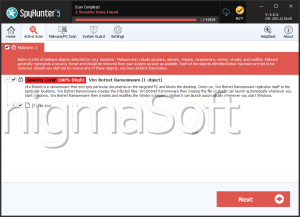
The Viro Ransomware is an Off-Spring of HiddenTear
It seems that the threat bundle with which the Viro Ransomware is delivered is not finished. This is because the worm that is included in the attack does not work properly. Furthermore, the keylogger seems also incapable of collecting passwords and other data, which supposedly is the typical function of a keylogger. Instead, the keylogger associated with the Viro Ransomware will collect the infected Web browsers' histories. However, the Viro Ransomware Trojan itself is capable of encrypting the victims' files. The Viro Ransomware Trojan is based on HiddenTear, an open source ransomware Trojan that was released in August 2015. Since its release, HiddenTear has made possible the appearance of numerous ransomware Trojans, all of which use this easily available open source code to develop new ransomware attacks with an effective encryption strategy. PC security analysts, however, suspect that due to the Viro Ransomware's unfinished nature, dealing with the attack may be possible. Computer users are advised to test existing HiddenTear decryptors to find out whether the files affected by the Viro Ransomware are recoverable. It is also entirely possible that a password to undo the Viro Ransomware infection will be released by malware analysts shortly.
Protecting Your Computer from Threats Like the Viro Ransomware
Ransomware Trojans like the Viro Ransomware will work by encrypting victim's files entirely and then demanding the payment of a ransom. This is an effective attack because the victim's files will remain encrypted even if the Viro Ransomware infection is removed. Fortunately, protecting your files from these attacks is simple. Having file backups on an external memory device or the cloud guarantees that you can recover from the Viro Ransomware attack without needing to pay the Viro Ransomware ransom. In fact, file backups are the single best protection against the Viro Ransomware and other ransomware Trojans, and it is important that all computer users have some backup system in play. Also important is the use of a reliable, fully updated anti-malware program, which may be capable of intercepting the Viro Ransomware before it carries out its attack.


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.