Vegclass Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 376 |
| First Seen: | May 11, 2016 |
| Last Seen: | January 8, 2020 |
| OS(es) Affected: | Windows |
The Vegclass@aol.com Ransomware is a variant of the Ecovector and the Mahasaraswati Ransomware, and an encryption ransomware Trojan that uses email addresses belonging to an India domain, colorful ransom notes with global warming or other related content, and short ransom messages instructing computer users to contact its associated email address. The Vegclass@aol.com Ransomware belongs to a growing family of ransomware Trojans known as CryptoEncoder. The Vegclass@aol.com Ransomware changes the encrypted files' extensions to the email address the Vegclass@aol.com Ransomware and '.xtbl.' Computer users should avoid paying the Vegclass@aol.com Ransomware ransom and, instead, remove the Vegclass@aol.com Ransomware immediately with the help of a reliable anti-malware program. Unfortunately, the files encrypted by the Vegclass@aol.com Ransomware are not decryptable without access to the decryption key, so it will be necessary to restore them from a backup.
Table of Contents
How the Vegclass@aol.com Ransomware Carries out Its Attack on Your Computer
The Vegclass@aol.com Ransomware carries out an attack pattern common among most encryption ransomware threats. In most cases, the Vegclass@aol.com Ransomware is delivered through corrupted email attachments. The presence of the Vegclass@aol.com Ransomware and its variants was noticed on file sharing networks contained inside popular torrent files. Once the Vegclass@aol.com Ransomware has entered a computer, it will carry out the following steps:
- The Vegclass@aol.com Ransomware establishes a connection with its Command and Control server, obtaining configuration data and relaying information about the infected PC.
- The Vegclass@aol.com Ransomware makes changes to the infected computer's settings, making sure that it runs whenever Windows starts up automatically.
- The Vegclass@aol.com Ransomware runs on the victim's computer, searching for certain file types and encrypting them using an advanced encryption algorithm.
When the Vegclass@aol.com Ransomware encrypts a file in a directory, it will drop a text or HTML file in that location. The dropped file contains a short sentence instructing the victim to email the con artists responsible for the Vegclass@aol.com Ransomware infection. The Vegclass@aol.com Ransomware also changes the affected computer's Desktop Image into a ransom message, which is displayed over a background depicting a factory emitting pollution – for some reason, many of the Vegclass@aol.com Ransomware's variants contain messages related to global warming awareness. The following is the message contained in these ransom notes:
To decrypt your data write me to [email@india.com]
When communicating with this email address, computer users will receive a response similar to the one displayed below:
Good morning, dear friend!
We are writing to inform you that our team of network security specialists has analyzed your system and has identified vulnerabilities in the protection.
We kindly draw your attention that defensive operation on your computer is not running properly and now the whole database is at risk.
All your files are encrypted and can not be accepted back without our professional help.
Obviously vulnerability analysis, troubleshooting, decoding the information and then ensuring safety are not a simple matter.
And so our high-grade and quick service is not free.
Please note that today the price of your files recovery is 3 Bitcoins, but next day it will cost 5 Bitcoins.
You should buy bitcoins here https://localbitcoins.com/faq
Read the paragraphs:
1. How to buy Bitcoins?
2. How do I send Bitcoins and how can I pay with Bitcoins after buying them?
The Bitcoin wallet for payment is 1DGMeKSALSkYGkedYDUgcvV8mP77WEGusQ
After the transfer of bitcoins please send email with screenshot of the payment page.
We does not advise you to lose time, because the price will encrese with each passing day.
As proof of our desire and readiness to help you, we can decipher a few of your files for test.
To check this you can upload any encrypted file on web site dropmefiles.com, size no more than 10 MB (only text file or a photo) and send us a download link.
Certainly after payment we guarantee prompt solution of the problem, decrypt the database to return to its former condition and consultation how to secure the rules of the system safety.
Kind regards
As with most encryption ransomware infections, prevention is the best measure. Computer users should protect their computers with a reliable anti-malware program that is fully up-to-date. The best way to nullify the threat presented by the Vegclass@aol.com Ransomware and its variants is to always backup your files on an external device.
SpyHunter Detects & Remove Vegclass Ransomware
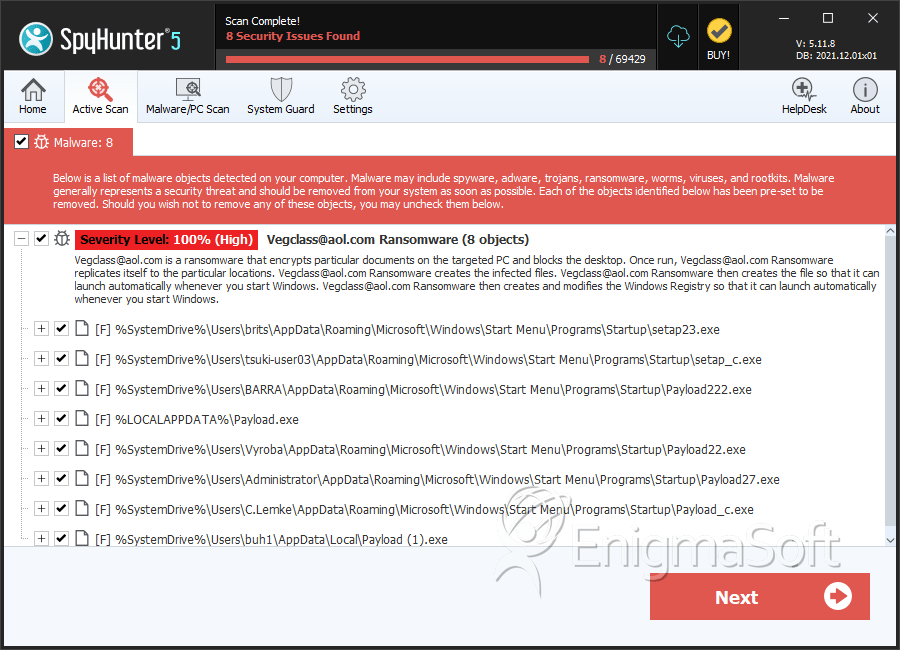
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | setap23.exe | 65076308420a2ec88b78e3a89363ffbc | 58 |
| 2. | setap_c.exe | e24c47ea6734e54abea20f0572e471f1 | 50 |
| 3. | Payload222.exe | bd3799e4b3b800e69f35983062aecc2f | 50 |
| 4. | Payload_c.exe | 9c06ee54141742ad86af69ad56411e56 | 36 |
| 5. | Payload_c.exe | dd868b858d3bfd81a181ab4a8ce5c763 | 25 |
| 6. | Payload.exe | 67c18e418a9d5911df5ac6fbae346054 | 20 |
| 7. | Payload2.exe | 95bc62c8951ef6368c66dae01c4f3cad | 15 |
| 8. | Payload0.exe | ccd2e0e61a83994bc5e3f6397d05fd5a | 8 |
| 9. | Payload22.exe | 1d080db77da3b953f3ee5b412585800e | 7 |
| 10. | Payload27.exe | 441472d28358781aa2c92af4a98082fd | 7 |
| 11. | Payload5.exe | 0e572e3d801e6d0d496e32caee1b4051 | 2 |
| 12. | Payload_c.exe | c50af907d224a9fb880a845c7b44e5d9 | 2 |
| 13. | Payload (1).exe | 6e43a6671c30a5e724f4435df355fdac | 1 |
| 14. | Payload2.exe | b36fd1368b77721bd7484dd6d458f736 | 1 |

