Unlock92 Ransomware
The Unlock92 Ransomware is a ransomware Trojan that is used to make money at the expense of inexperienced computer users. The Unlock92 Ransomware is identical to the Kozy.Jozy, a threatening ransomware Trojan with the same method of attack as this threat. Once the Unlock92 Ransomware enters a computer, it uses an asymmetric encryption algorithm to encrypt the victim's files. After encrypting the victim's files, the Unlock92 Ransomware displays a ransom message, changing the victim's Desktop wallpaper image and dropping text files on the affected computer. If the Unlock92 Ransomware infects your computer, PC security analysts recommend that computer users restore their files from a backup and avoid paying the Unlock92 Ransomware's ransom, since there is no guarantee that the con artists responsible for the Unlock92 Ransomware will honor their promise and deliver the decryption key.
Table of Contents
Although in Another Language, It is Easy to Know that You are Attacked
The Unlock92 Ransomware's ransom note is in Russian and claims that the victim's files were encrypted. The Unlock92 Ransomware threatens the victim, offering to decrypt one file using the key.bin file, which is dropped in each directory where there is content encrypted by the Unlock92 Ransomware. The Unlock92 Ransomware forces computer users to email Unlock92@INDIA.COM so that they will receive further payment instructions. Computer users are instructed to connect to a TOR website to pay the ransom.
Unfortunately, it may not be possible to decrypt the files encrypted by the Unlock92 Ransomware because of the type of encryption process used to take the victim's files hostage. However, in the case of the Unlock92 Ransomware specifically, some computer users have had success using an available decrypter released by PC security analysts. The exact ransom demanded by the Unlock92 Ransomware is still unknown, but most similar threats demand an average of 1 BitCoin (which at the current exchange rate is a little under $700 USD. Computer users should avoid paying this ransom since they will probably lose their money. Instead, computer users should take preventive measures to ensure that their computers are not vulnerable to these kinds of attacks. A backup of all files and a reliable security application that can prevent these attacks are the two best measures computer users can take to ensure that they do not become victims of the Unlock92 Ransomware and similar threats.
How the Attack of the Unlock92 Ransomware and Similar Threats Work
The Unlock92 Ransomware seems to be a clone of Kozy.Jozy but is also nearly identical to a wide variety of threats that have become very popular in recent years. These threats all follow the same strategy, entering the victim's computer through covert means and then demanding the payment of a ransom after encrypting the victim's files. The most common distribution methods for the Unlock92 Ransomware and similar threats and corrupted email attachments, bogus software downloads and updates, and peer-to-peer (P2P) file sharing networks. Taking steps to use these resources safely and a reliable anti-malware program to protect your computer can ensure that you do not become a victim of these attacks. Caution and a reliable security program can ensure that the Unlock92 Ransomware and similar threats do not enter your computer and encrypt your files.
The following is the ransom note (written in Russian) that is used as part of the Unlock92 Ransomware attack:
ВАШИ ФАЙЛЫ БЫЛИ ЗАШИФРОВАНЫ!
Если вы хотите их восстановить то отправьте один из пострадавших файлов и файл Кеу.Ып (из любой папки с зашифрованными файлами) на е-mai1: the Unlock92@INDIA.COM Если вы не получили ответа в течение суток то скачайте с сайта https://www.torproject.org/download/download-easy.html.en ТОВ браузер и зайдите с его помощью на сайт http://fnjmegsn7tbrrnkl.onion - там будет указан действующий почтовый ящик.
Iопытки самостоятельно расшифровать файлы приведут к их безвозвратной порче!
The Unlock92 Ransomware targets files with the following extensions during its encryption attack:
.cd, .ldf, .mdf, .max, .dbf, .epf, .1cd, .md, .pdf, .ppt, .xls, .doc, .arj, .tar, .7z, .rar, .zip, .tif, .jpg, .bmp, .png, .cdr, .psd, .jpeg, .docx, .xlsx, .pptx, .accdb, .mdb, .rtf, .odt, .ods, .odb, .odg.
SpyHunter Detects & Remove Unlock92 Ransomware
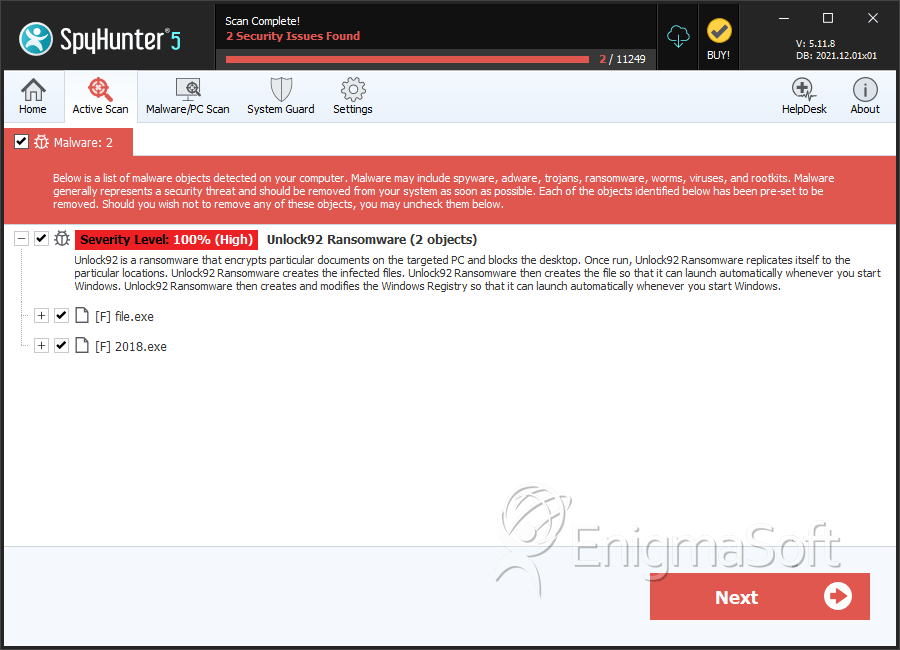
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | b9877c0cbef3dd35a84e9a7fdb5efb46 | 0 |
| 2. | 2018.exe | 1b53e4d8183631874f1c20ac6a670693 | 0 |